SEAL Intel Member Heiner delves into the ever-changing world of DPRK IT Workers. This report uncovers a significant recent shift in their strategy, enhancing fraudulent job-seeking with a scalable model of actively recruiting knowing and unknowing collaborators outside North Korea. Through detailed evidence and analysis, Heiner exposes their systematic playbook for hijacking identities and freelance platforms on a global scale.
Index:
• Executive summary
• Hypothesis: Two Roles — Workers and Recruiters
• Context
• Recruitment Activity Among DPRK IT Workers
• The recruiting process
• Interaction with collaborator
• Systematic Recruitment and Identity Harvesting
• Use of Facilitators and Financial Channels
• Operational Breakdown — North Korean “IT Recruiter” Playbook
• Highlight activity of It worker
• Conclusion
• Recommendation
Executive summary
Recent monitoring of activity on GitHub and freelance platforms such as Upwork has revealed a significant shift in the behavior of certain IT workers — from merely seeking employment to adopting more deceptive and intrusive tactics.
This marks the emergence of a second, more scalable phase in their operations. Increasingly, DPRK-linked IT workers are acting as recruiters, orchestrating coordinated campaigns to enlist collaborators through platforms like Upwork and Freelancer. These recruiters approach targets with a scripted pitch, requesting “collaborators” to help bid on and deliver projects. They provide step-by-step instructions for account registration, identity verification, and credential sharing.
In many cases, victims ultimately surrender full access to their freelance accounts or install remote-access tools such as AnyDesk or Chrome Remote Desktop. This enables the threat actor to operate under the victim’s verified identity and IP address, allowing them to bypass platform verification controls and conduct illicit activity undetected
Operational Hypothesis: Two Roles — Workers and Recruiters
Evidence indicates that IT Workers are increasingly pivoting to recruiter-style activity. Rather than isolated opportunism, the scope and consistency of the material suggest a coordinated, repeatable pattern: actors adapt their tactics rapidly, share operational playbooks, and deploy structured scripts for onboarding collaborators. The volume of artifacts and timestamps point to this becoming common since 2024, and the recruitment-related workflows observed are well-organized and widely shared among the group.
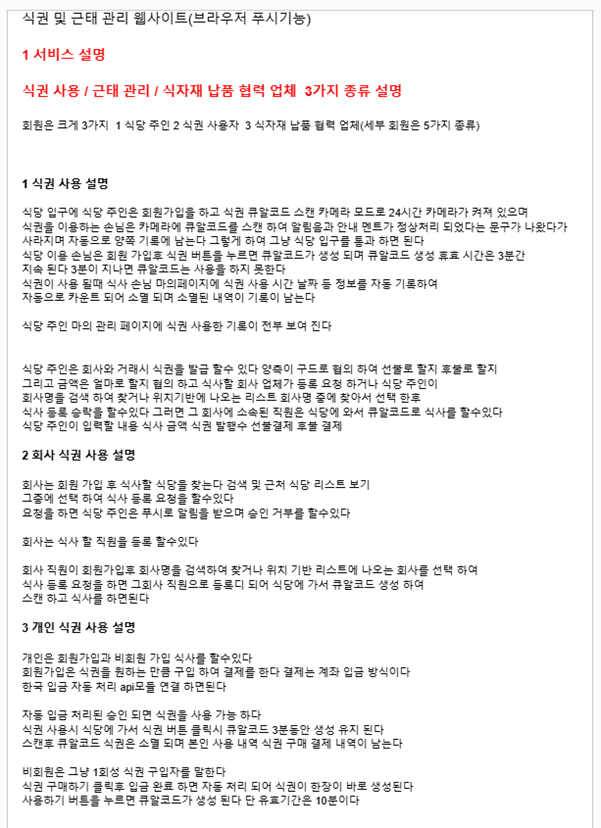
To help visualize this evolving tactic, the following graphic summarizes the eight-step operational model observed across multiple cases. This flow illustrates how DPRK-linked IT workers initiate contact, establish control over freelance accounts, and sustain long-term access through collaborator recruitment.
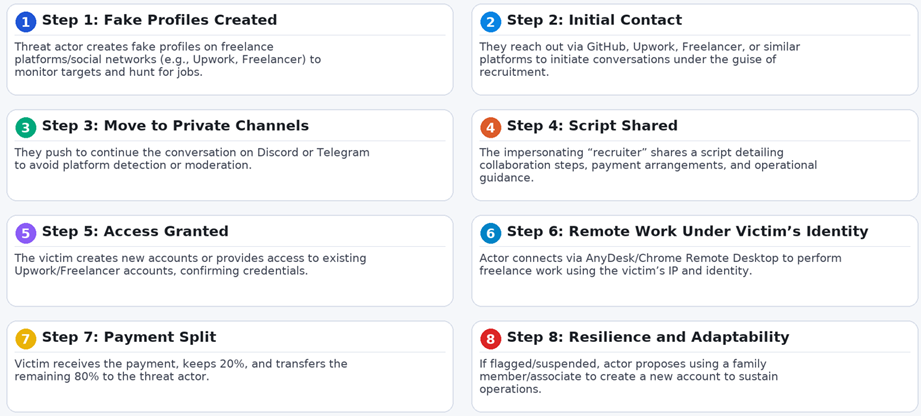
This visual framework reinforces the hypothesis that these actors are operating under a shared methodology rather than acting independently. The recurrence of this workflow across different platforms, identities, and timelines strongly suggests coordination and knowledge sharing hallmarks of a maturing operational model.
Context
For some time, several IT workers have successfully infiltrated companies around the world under false pretense. This activity has drawn the attention from international authorities due to the growing complexity and scale of the operations. In recent years, these workers have been deployed by the Democratic People’s Republic of Korea (DPRK) to secure remote IT roles, often using stolen identities and shell companies.
Notably, monitoring from Microsoft Threat Intelligence and CrowdStrike indicates that these actors are leveraging artificial intelligence, organized workflows, and global “laptop farm” networks to infiltrate companies rapidly and launder profits back to the regime.
These developments underscore a serious threat: what began as opportunistic remote hiring has evolved into a well-coordinated, institutionalized campaign to generate revenue for the DPRK while gaining access to sensitive corporate systems
Alongside this already well-documented activity related to IT Workers and their fraudulent methods of obtaining employment through the use of false or altered identities, ongoing monitoring has revealed additional cases that clearly indicate the existence of a role that could be described as IT Recruiters, who also play a key part in facilitating this broader fraudulent ecosystem.
Recruitment Activity Among DPRK IT Workers
The fraudulent activity linked to DPRK IT recruiters has grown more structured and deceptive, particularly in how they conceal their identities and scale their operations. Rather than solely seeking jobs, many of these actors have pivoted to posing as recruiters a tactic that allows them to expand access, delegate risk, and operate through others.
They exploit a wide range of platforms including Upwork, Freelancer, Fiverr, RandstadUSA, and others — not just to find jobs, but to recruit collaborators under the pretense of legitimate freelance offers. To build trust, they often rely on verified profiles, proxy identities, and occasionally stolen documents.
Once contact is made, communication quickly moves to unmonitored channels like Telegram, Discord, or email. There, they share onboarding steps, operational instructions, and payment terms. This recruiter-first model gives them access to verified accounts, allows them to operate under false identities, and route earnings through intermediaries — all while reducing their exposure.
It remains uncertain whether these individuals operate solely as IT Workers who occasionally engage in recruitment, or if there exists a distinct group of IT Recruiters collaborating with them.
The available evidence suggests a significant overlap between both roles, some actors appear to manage technical tasks while simultaneously coordinating the onboarding of new “collaborators.” However, it is still unclear whether this represents a structured division of labor or simply individual IT Workers adapting their tactics and expanding their activities over time
Operational Evidence from Monitored North Korean It Worker Profiles
During the active monitoring of several IT workers, multiple known behaviors were observed such as the use of AI to alter personal photos. One example involves a Google Drive folder titled “My Photo,” where the IT worker likely edited their own image. Other folders were labeled with different individuals’ names, suggesting that this one specifically belonged to the operator. The following image was found within that folder:

In the following image, the original picture used to alter and replace the individual’s facial features can be seen, showing the transformation from the source image to the modified version

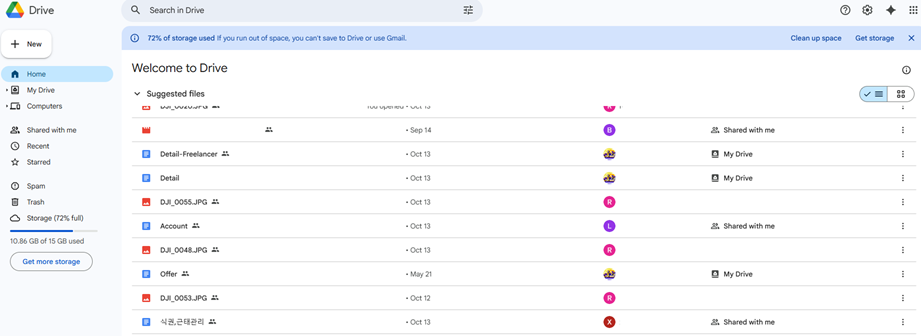
On the other hand, the evidence suggests a significant overlap between the two roles, with some actors simultaneously managing technical tasks and coordinating the onboarding of new “collaborators.” This type of behavior has also been confirmed through various documents hosted in different locations. In this case, evidence was found in a drive linked to a fraudulent profile under monitoring.
Within this repository, documents related to recruitment activities were identified, offering more detailed insight into the techniques being used. As shown in the image below, several files were found that support the existence of this activity:
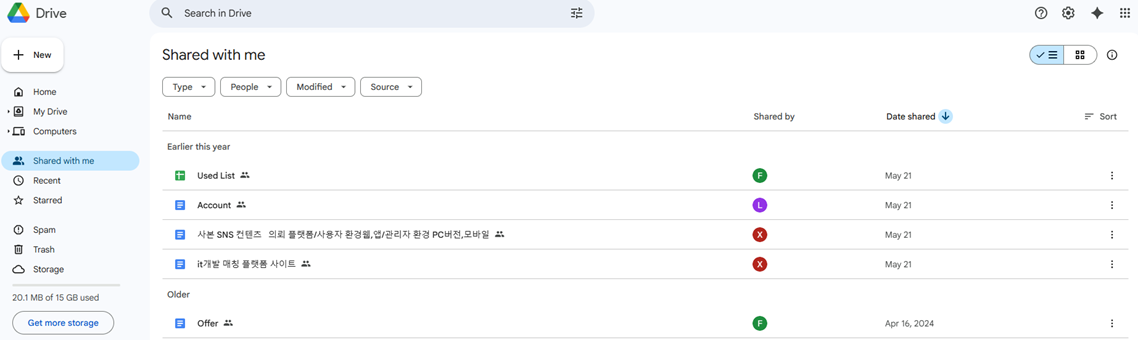
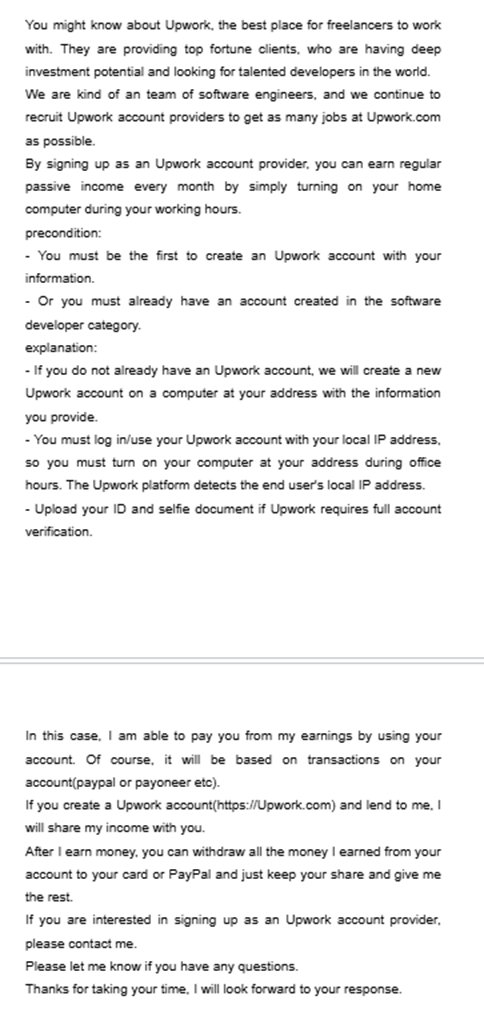
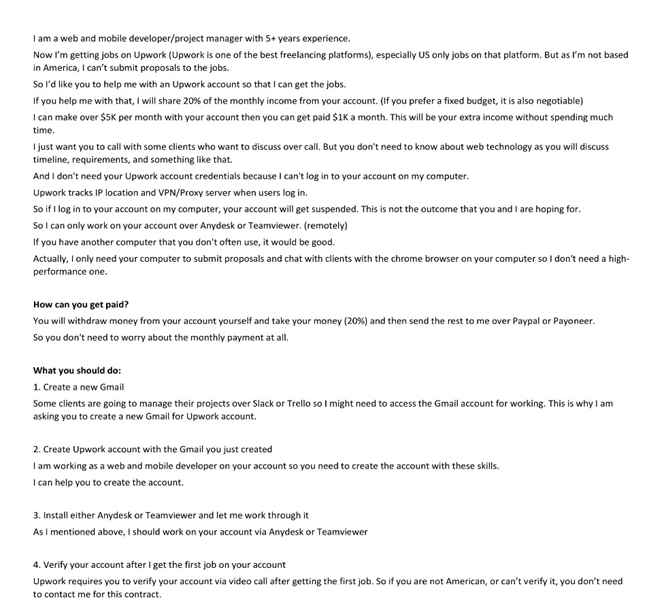
Upon analyzing the document titled “Account,” a section was found containing clear instructions on how to access Upwork, the reasons for doing so, why individuals should work with them, and how the profits are to be divided. As shown in the image below, these details are explicitly outlined:
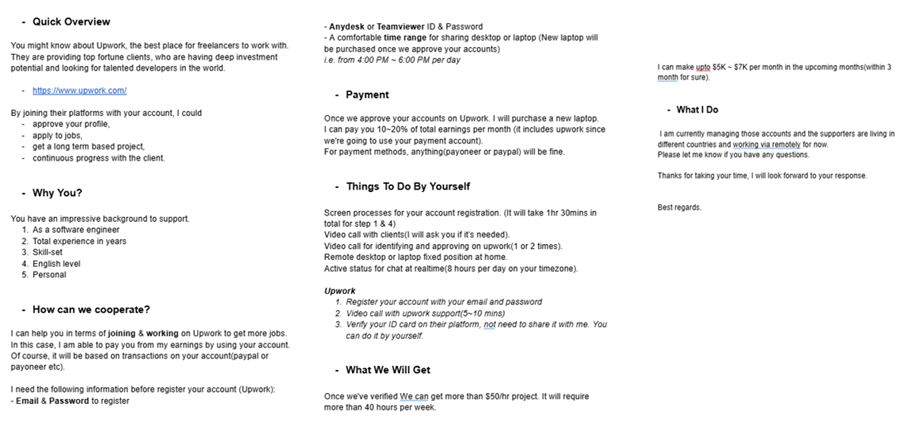
The document titled “Offer” is a shorter version of the same content, presenting a more concise version of the instructions:
In addition to this, several documents were also found in Korean, such as “it개발 매칭 플랫폼 사이트,” which translates to “IT development matching platform site”:
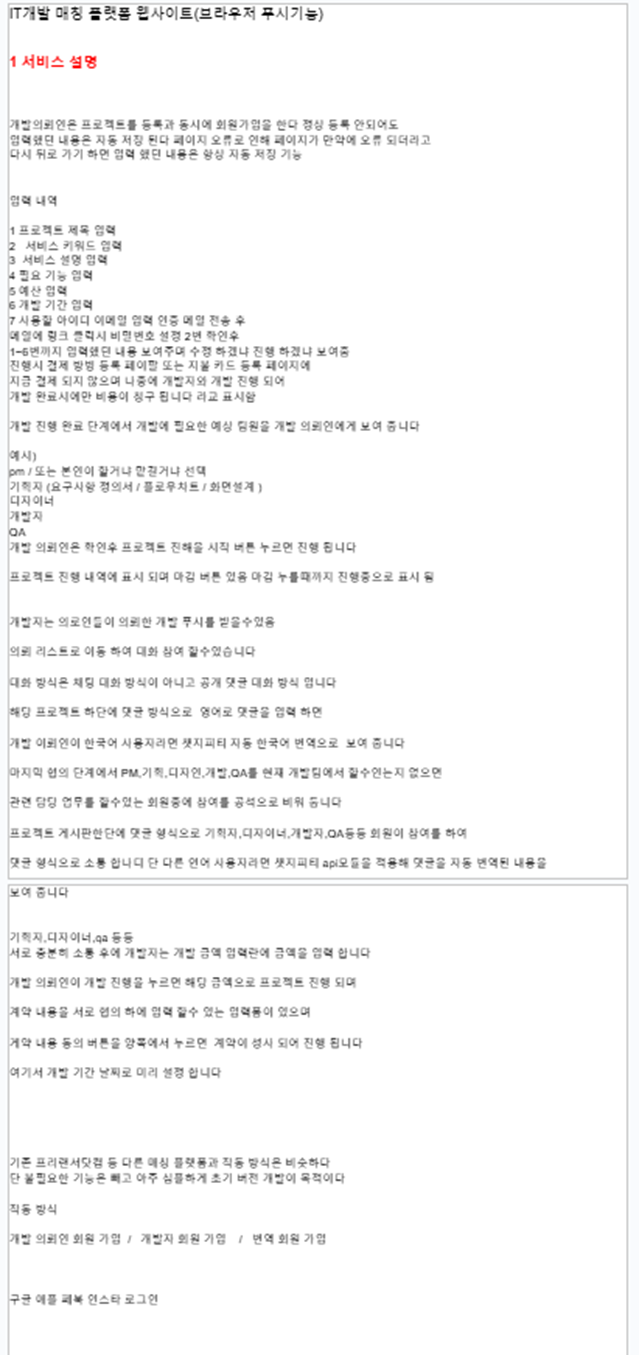
According to the translation, the document provides a comprehensive overview of an IT developer matching platform, designed to connect freelance developers with companies or clients seeking software development services. Conceptually, it mirrors international freelancing marketplaces such as Upwork, Freelancer, or Fiverr, but is specifically tailored to Korean-speaking users and the domestic IT ecosystem.
The platform’s structure emphasizes end-to-end project lifecycle management, offering dedicated environments for companies, developers, and administrators. It enables clients to post projects, define technical requirements, and monitor progress, while developers can create detailed profiles, register their skills, upload portfolios, and apply directly to suitable projects.
Upon analyzing additional related content, further documents were identified that follow this same recruitment method, which appears to be part of a shared script likely distributed among "collaborators." This additional example reinforces the same modus operandi. Likewise, further documents written in Korean were also observed.
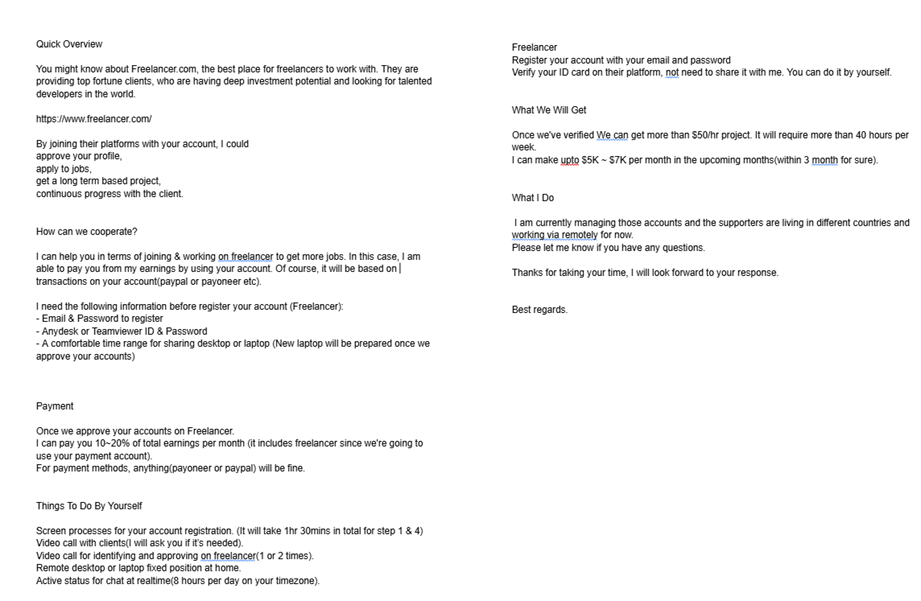
Regarding the document “Detail-Freelancer,” it uses the same type of template, providing instructions on how to work for them and how to manage accounts and passwords. They state that they do not want these documents to be kept; however, the evidence suggests that they retain many of these identities:
Regarding the Korean-language document: it outlines the design and functionality of a web platform for managing meal tickets, attendance, and food supply partners. Essentially, it is a digital system for meal and attendance management that connects restaurants, companies, and individual users—automating the entire process from ticket purchase to meal verification.
Several of the other documents appear to be project files and aerial images related to construction jobs, including the development of blueprints and other types of work they have seemingly acquired.
In addition to these, a PowerPoint presentation titled “Freelancing” was also found, directly related to this activity. It outlines the hiring process with the group, how it is expected to be conducted, and the workflow that should be followed.
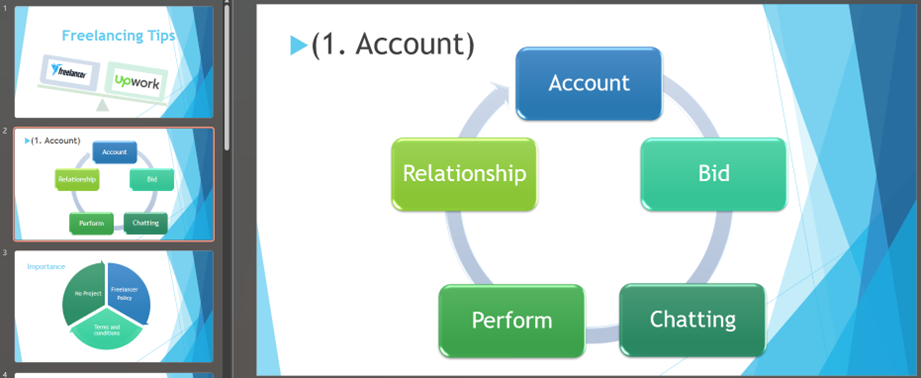
The presentation even includes reference images such as the one below, where individuals are profiled based on specific criteria to assess their suitability. One example shows a person alongside their ID—note that the image has been blurred to prevent public exposure of sensitive information:
Another example of the dialogue used to attract individuals can be seen in the following slide. It features text similar to what has been observed in previous materials, clearly intended to recruit collaborators who can then be leveraged for this purpose.
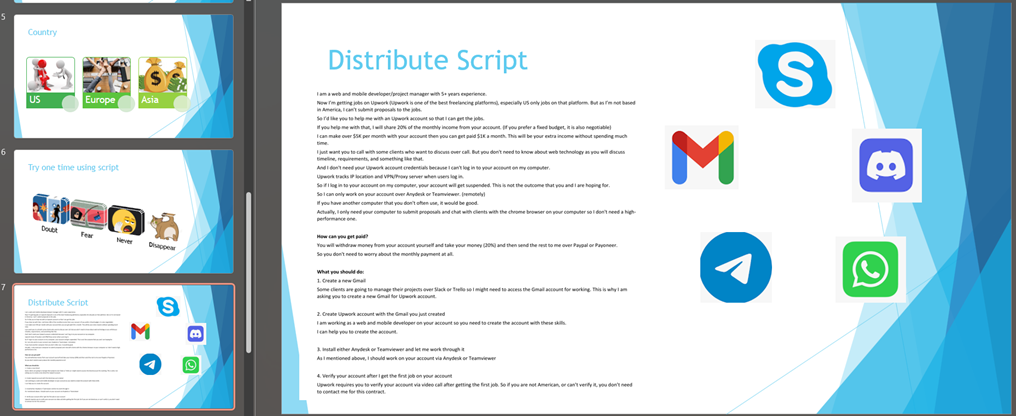
The script or text shown in this slide outlines how to work with them, including details on the payment structure for those who choose to collaborate:
As previously demonstrated, there are numerous texts that serve the same purpose: guiding individuals, potentially victims, toward working or collaborating with them in this manner. The evidence suggests that these texts are widely shared across multiple accounts. In addition, the level of organization and the consistency across different documents containing instructions that point to the same objective strongly suggest this is part of a coordinated campaign.
The recruiting process
In some cases, contact with these individuals is initiated through commonly used social media platforms or Telegram to reach out to potential “collaborators.”
However, one notable aspect of the recruitment process is that it is also being conducted through freelancing platforms such as Upwork and Freelancer, code platforms like GitHub, Job portals to post fake jobs and even used online community website for disabled people and websites like InterPals is the top platform to make new friends.
Some of the information suggests that the most desirable candidates for these actors are located in the United States, Europe, and parts of Asia. Additionally, the evidence reveals specific targeting of individuals from certain regions, with Ukraine and the Philippines appearing most frequently in the analyzed folders.
The following section presents several instances where large-scale recruitment activity was confirmed. In many of these cases, the actors used every possible channel to find individuals willing to collaborate with them
Recruitment in GitHub
The following image illustrates the type of proposals these recruiters send to GitHub users. In some cases, conversations have been observed moving from GitHub to Discord, where the recruitment process continues more privately.
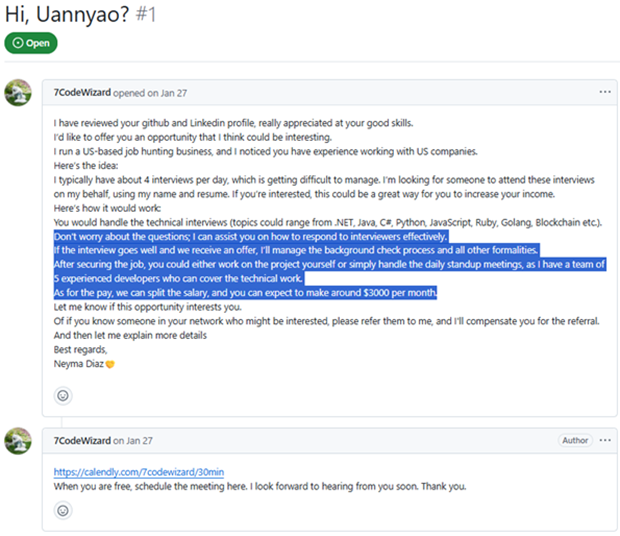
Although this profile has since been removed, there is a growing trend of similar activity in which certain accounts linked to DPRK IT Workers, both on GitHub and across employment platforms, have attempted to recruit other individuals. The information gathered suggests that this recruitment behavior is evolving and increasingly resembles a broader social engineering campaign, where IT Workers attempt to enlist collaborators through code-sharing platforms and job marketplaces.
Recruitment in Job platforms
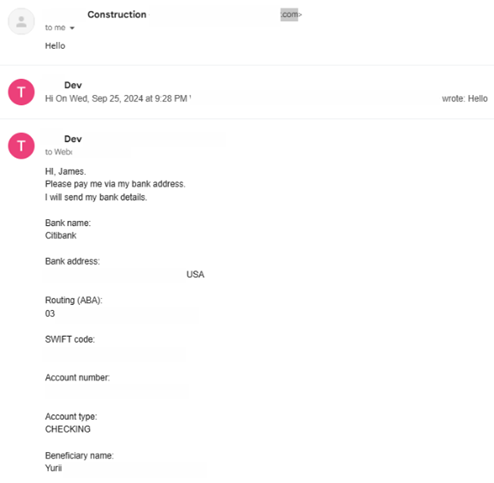
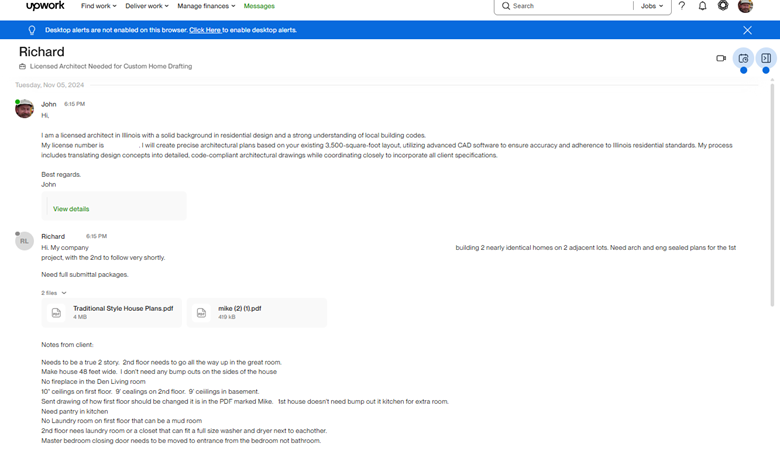
Multiple conversations reveal their approach via Freelancer or Upwork, primarily offering arrangements that align with this tactic. The following exchange between a victim and a North Korean IT worker highlights this hiring process:
Just like this example, there are many instances where job search platforms are used to recruit individuals. In the following image, it is evident that they approach users they are monitoring on employment platforms — in this case, Freelancer.
This evidence shows that employment platforms are also being used for recruitment purposes by these threat actors. Individuals are profiled in various ways on these sites, and it is important to note that this activity appears to have begun in early 2024, suggesting it may already be operating at a broader scale.
Recruitment via Fake job listing
One particular case revealed that an IT recruiter was creating fake job listings under titles such as “Virtual Assistant — Customer Support.” This was observed on platforms like Virtualstaff.ph and Onlinejobs.ph.
Through these job postings, they created communication channels to persuade potential victims to collaborate with them. As shown in the following image, the IT recruiter even referenced Freelancer.com during the exchange:
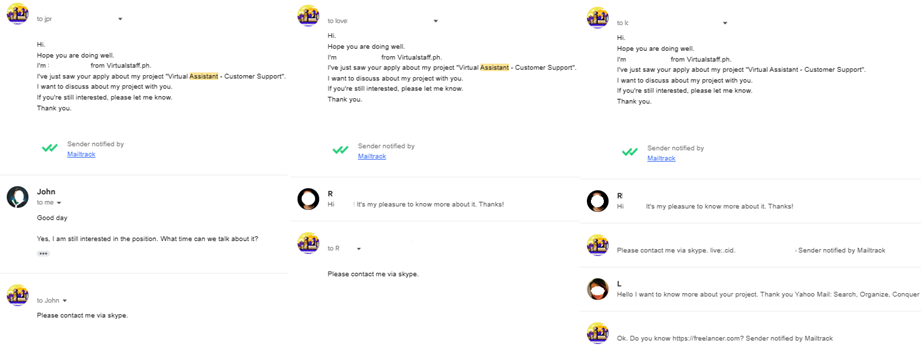
The same job offer previously posted on the earlier employment platform was also published on OnlineJobs, using the same title and description. The IT recruiter received emails in response to this posting and interacted with several individuals. Roles such as “Virtual Assistant” are particularly effective for this type of recruitment, as they can be easily misrepresented by IT recruiters to initiate collaboration under false pretenses:
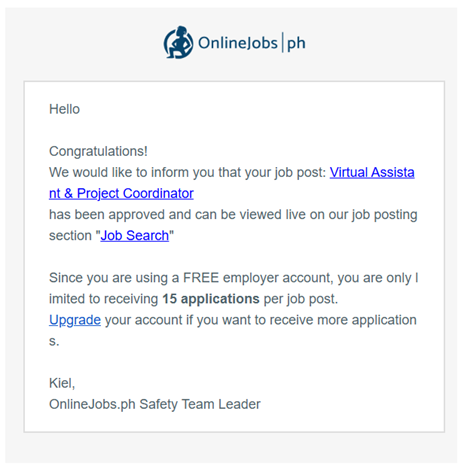
While fake job postings may not be a widespread tactic among all IT recruiters, this particular actor employed more aggressive and intrusive techniques when engaging with potential collaborators
Recruitment Within Communities
As previously mentioned, there is evidence of increasingly aggressive recruitment tactics, including attempts to interact with individuals across various online communities. One notable example involves outreach on AbleHere.com, a website dedicated to people with disabilities:
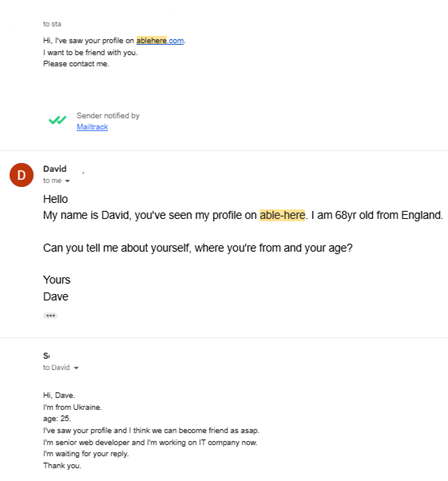
This type of targeted outreach toward specific communities was also evident in the platforms where IT recruiters submitted applications. One such example is e-Buddies, a program designed to foster social inclusion and build friendships between individuals with and without intellectual and developmental disabilities (IDD) in a virtual environment:
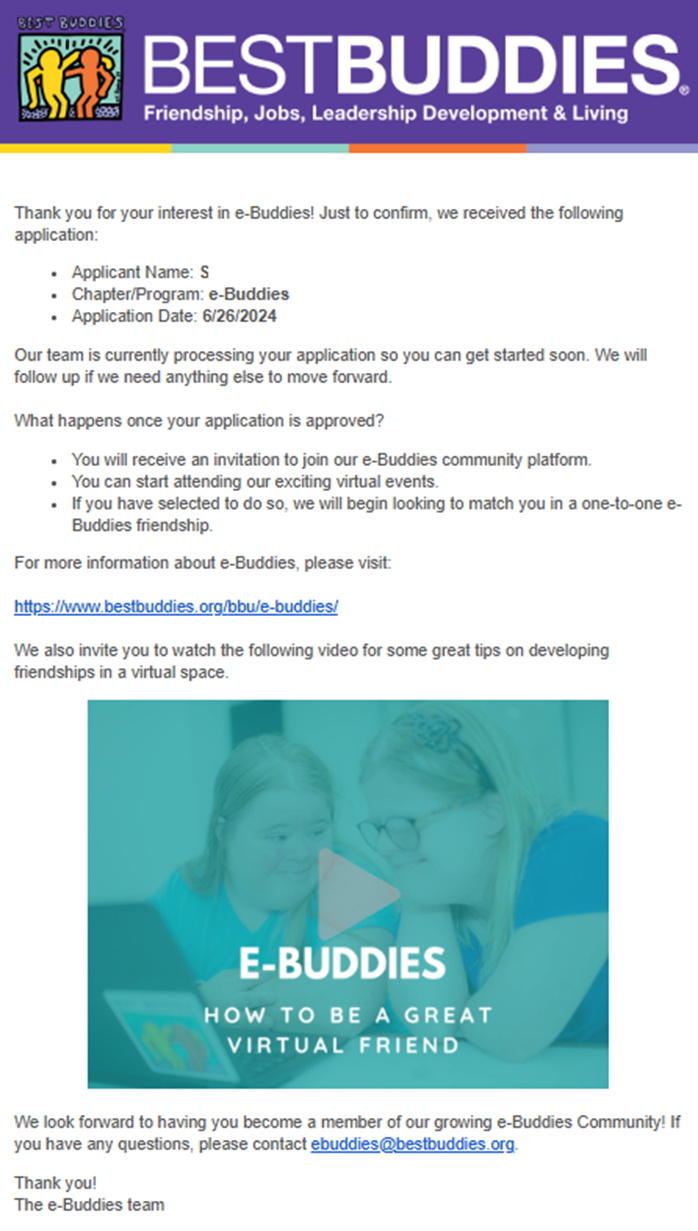
Other instances involve activity within language-learning communities, where recruiters can more easily blend in under the guise of cultural exchange or language practice. One such platform is InterPals, a popular site used to connect with native speakers and travelers around the world:
These interactions with websites associated with communities of individuals with disabilities represent a distinct tactic used by some IT recruiters. While this does not appear to be a systematic practice, there is clear evidence that such actors have engaged in this strategy, targeting diverse audiences who may be more vulnerable to manipulation.
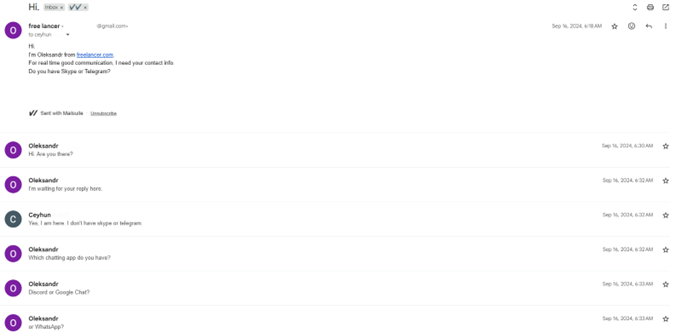
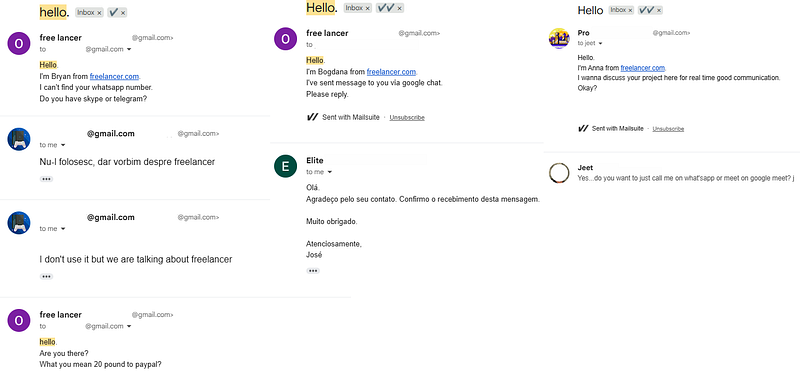
Recruitment via Mail
In other cases, there is evidence of mass outreach to multiple targeted accounts identified across various employment-focused social networks. They distribute offers at scale using tools like Mailsuite-Mailtrack, which allow them to monitor the status of the emails sent.
(More images available, reserved for SEAL use only.)
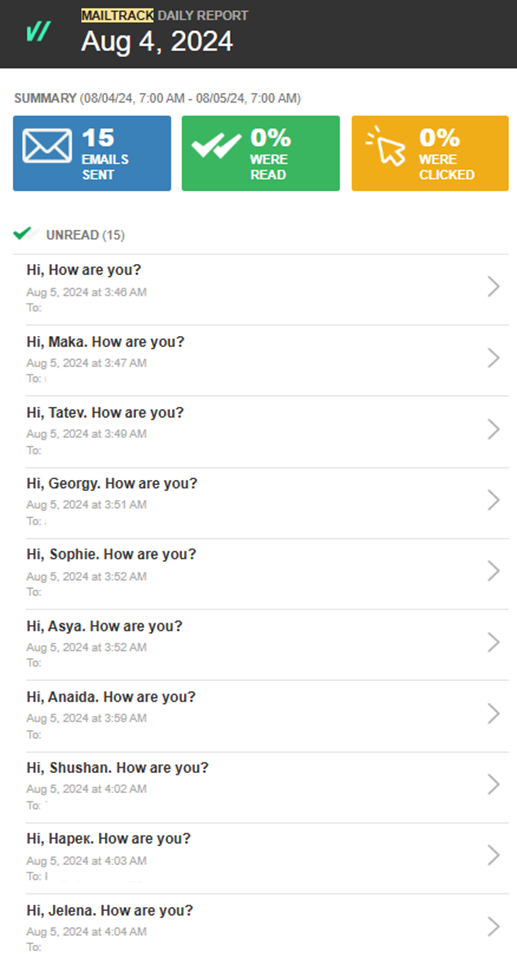
The message that this IT recruiter is observed sending in bulk is as follows:
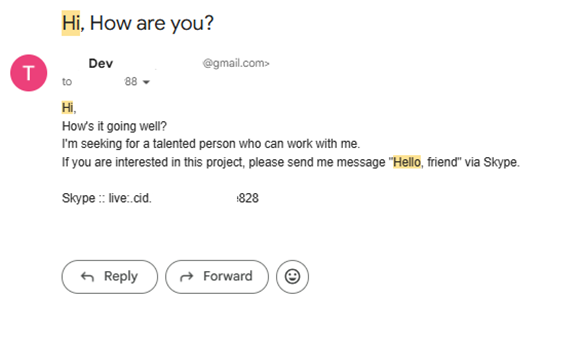
Once contact has been established, several documents and conversations reveal interactions between the recruiters and the individuals they target. These records show how the recruiters initially present themselves and attempt to establish cooperation with their victims.
Interaction with collaborator
The following conversation between the “IT Recruiter” and the victim illustrates this behavior. These exchanges took place in September 2024. Ana is the recruited collaborator, and Monkey is the North Korean IT worker or recruiter.
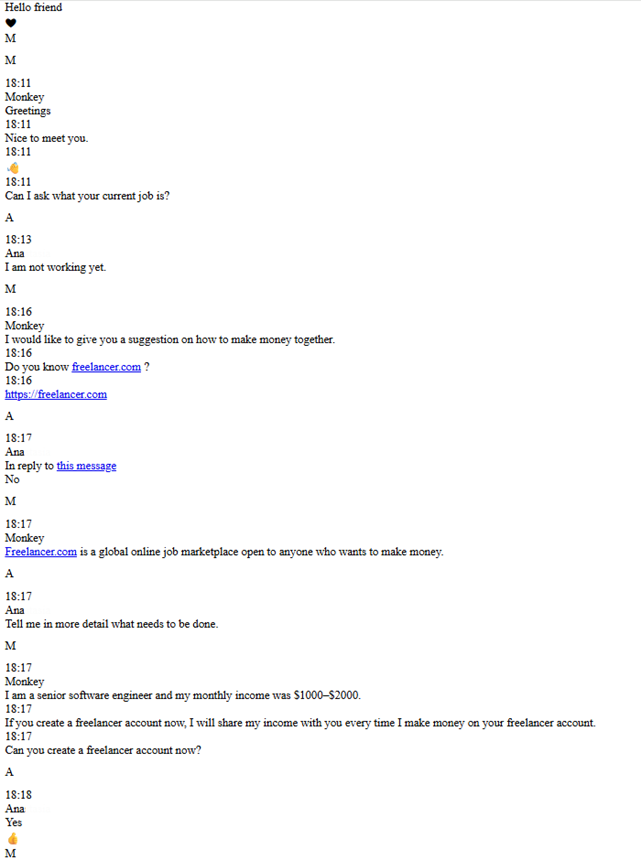
Once the individual completes the registration process, they share this information with the IT recruiter
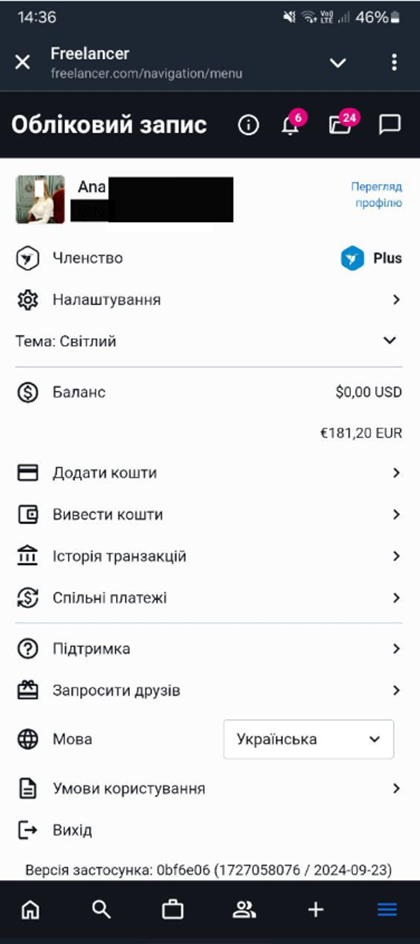
A particular aspect of this IT recruiter is their direct style of communication. It is also notable that the individuals being targeted are from Ukraine, as confirmed in this conversation. In the same exchange, Ana asks how they will make money from this arrangement:
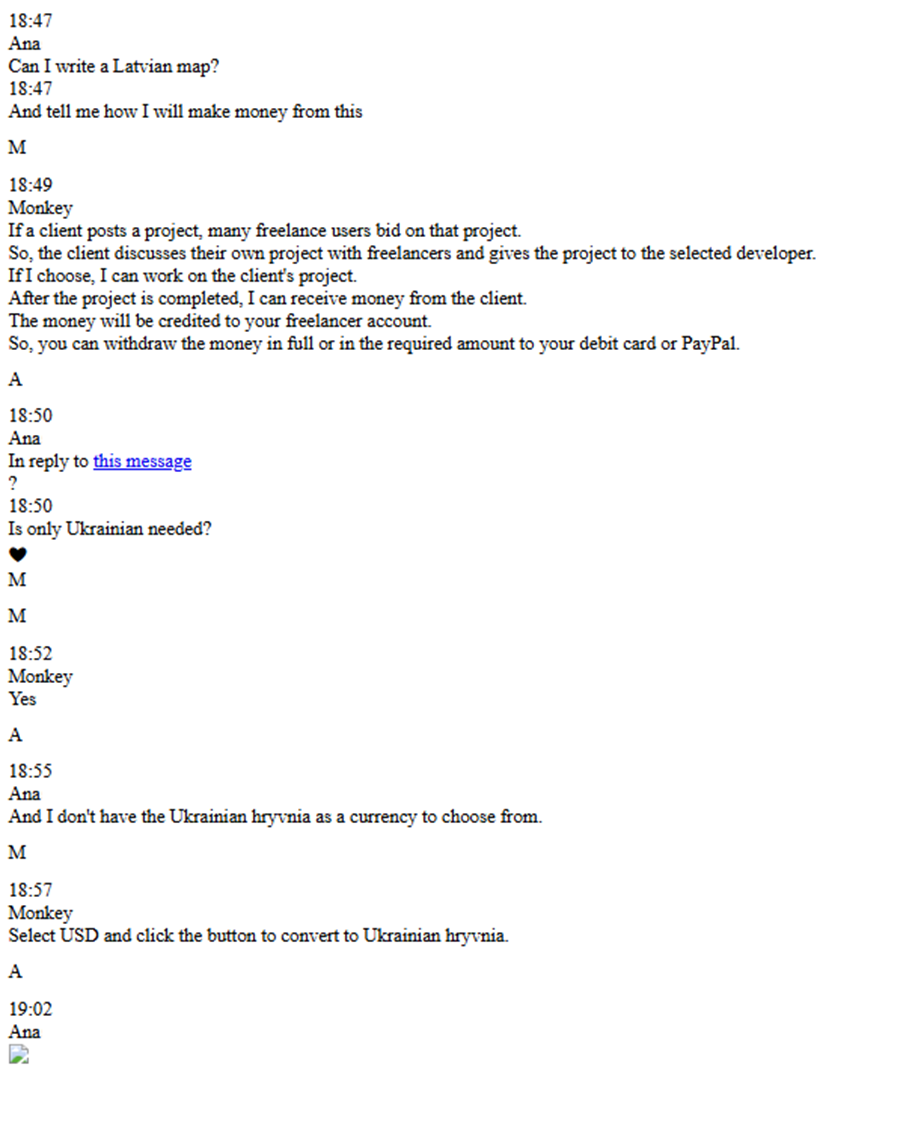
These conversations demonstrate the use of individuals as collaborators, enabling IT workers to operate under their identities. In this scenario, there is a process in which the IT recruiters manage to convince these individuals to allow them to work using a legitimate identity. The IT workers then exploit this access to “work” under the recruited person's profile — in this case, Ana.
It is important to note that this IT worker caused the Upwork account to be blocked due to excessive activity — working at least 19 hours, as described in the following chat:
Following this incident, the individual shares their ID, which confirms that they are from Ukraine.
Systematic Recruitment and Identity Harvesting
This recruitment process on platforms like Upwork involves individuals being required to share their personal information — including identification documents, bank account details, and other sensitive data — in order for earnings to be distributed according to the terms set by the recruiter.
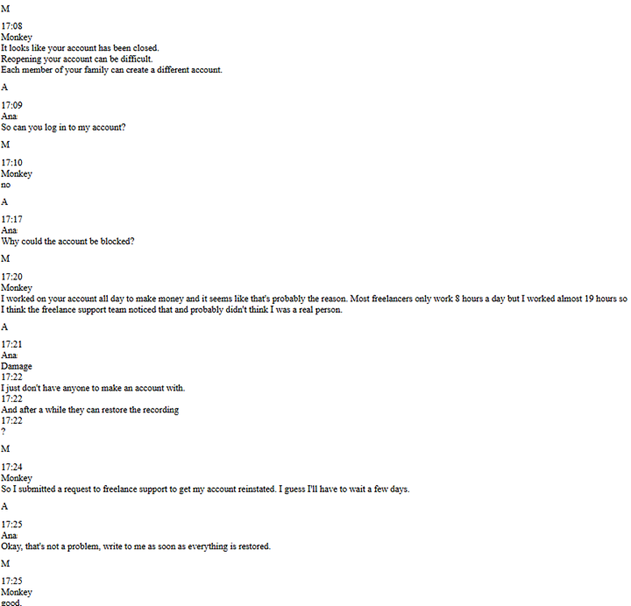
As is widely known, Upwork’s identity verification process requires users to hold their ID physically next to their face to confirm both the person and the legitimacy of the document.
This verification process is often directed by the IT recruiter, who in many cases retains copies of all the documents used to access the platform.
The evidence presented here demonstrates the scale of this operation. Rather than mere collaborators, these individuals are clearly being systematically recruited through freelance platforms and other platforms, ultimately working on behalf of unauthorized actors — often without full awareness of the operation’s true purpose.
It is important to highlight that much of this evidence is stored across multiple folders linked to their activity as IT workers. The following image is part of the evidence suggesting that these individuals are being used, while the IT recruiters or IT workers retain access to their credentials:
This image is evidence of the scale at which these IT recruiters are operating to persuade individuals to work for them. The information associated with these individuals highlights their complicity as collaborators in this type of recruitment activity, which aims to exploit legitimate users to gain access to employment opportunities.
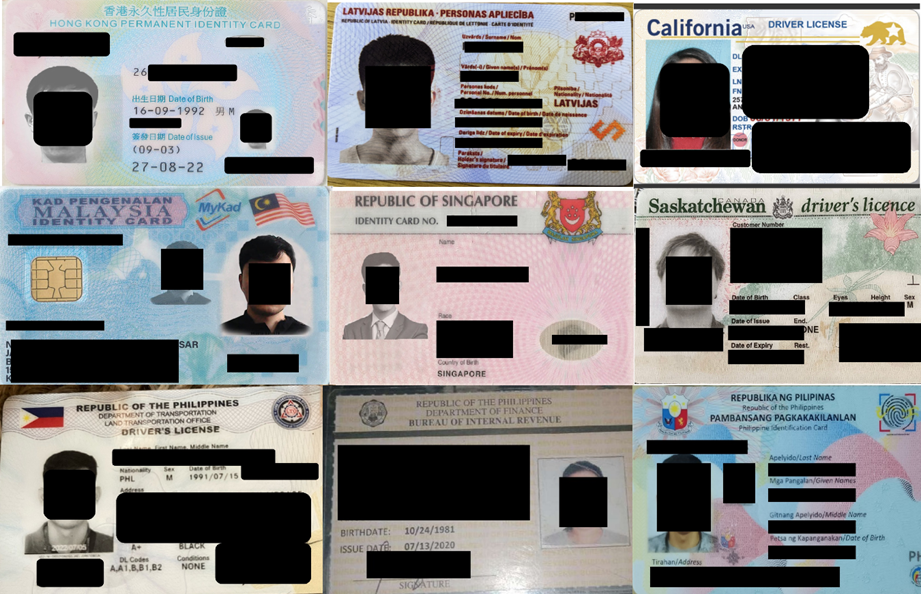
One notable aspect observed in the analysis of the recovered data dump is the presence of identification documents and the origins of many of the individuals involved, as well as a specific pattern in gender. The data reveals individuals from Hong Kong, United States, Philippines, Malaysia, with a particularly high number of Ukrainian women.
This pattern is especially evident in the large volume of IDs linked to Ukrainian women, suggesting a possible preference or targeting criterion in the recruitment of this type of collaborator. The following image shows IDs belonging to Ukrainian women, where increased activity related to identity usage was observed, including conversations with several of these potential victims:
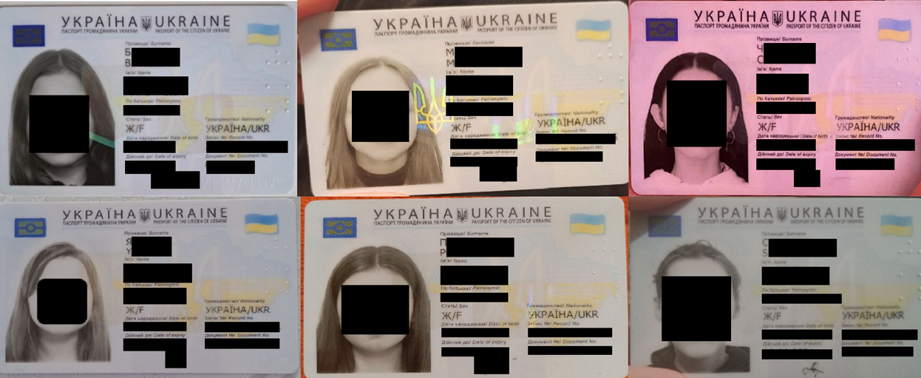
In addition to these legitimate identification documents linked to Ukrainian women, there is also a wide range of documents associated with individuals from various other parts of the world
This North Korean actor appears to have been using “Verif.tools” to generate fraudulent documents. It is important to note that authorities from the Netherlands and the United States recently announced the takedown of an illicit marketplace known as VerifTools, which was used to distribute fake identity documents to cybercriminals worldwide.
The following example shows the use of this website to create a document containing fabricated images and personal data

The previous image highlights certain characteristics commonly observed in manipulated identity documents. These forgeries are typically displayed on flat surfaces. In contrast, when comparing them to legitimate IDs from Ukrainian individuals, we see that the documents are often held in-hand. Natural shadows and hand positioning are significantly harder for synthetic tools to replicate accurately.
Compared to the previous document, this “IT recruiter” also appears to have used legitimate identities. In some cases, there is no need to rely on AI-generated documents. In the example below, the individual shared a driver’s license, a passport, and a U.S. passport card. The following image shows a genuine document, which differs from the earlier forgery by displaying natural shadows, reflections, and folds that are very difficult to reproduce:
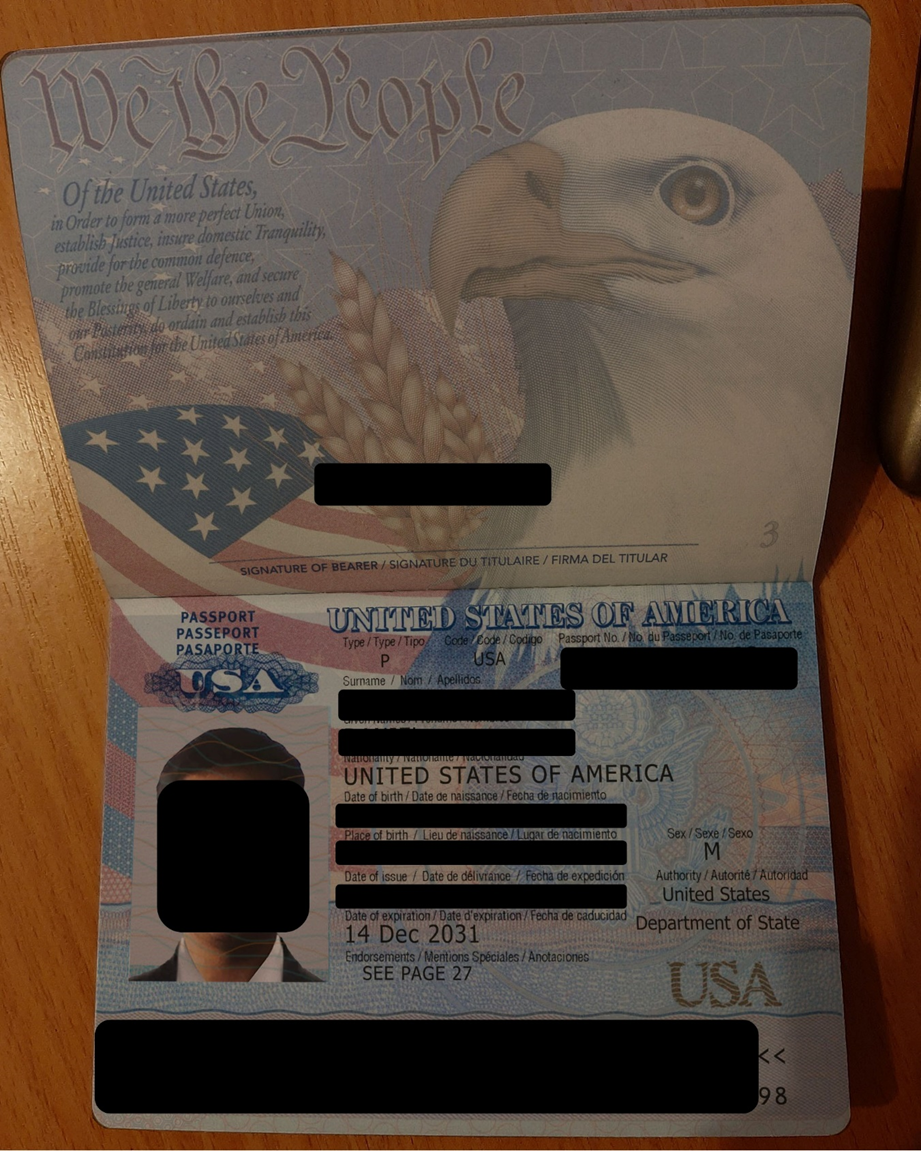
For this reason, requesting ID verification not on flat surfaces and requiring the person to hold the document in a specific way introduces visual complexity that makes it more difficult for AI-driven forgery tools to convincingly reproduce.
In addition to these fraudulent documents, this individual appears to have used the identities of more than a dozen people for various employment-related activities. The presence of these documents and identities highlights the scale of this recruitment effort targeting collaborators. Furthermore, individuals of multiple nationalities appear to have cooperated with them, either knowingly or unknowingly.
This is further illustrated in the following image, which provides additional evidence of how these identities are being leveraged
In addition, evidence has been found linking payment account information to companies based in European countries as well as the United States. These accounts appear to be registered under the names of certain facilitators who also serve as intermediaries for transferring the profits to bank accounts or cryptocurrency wallets.
Use of Facilitators and Financial Channels
As previously mentioned, payments to these individuals are typically agreed upon from the outset. In most observed cases, the arrangement consists of 80% of the earnings going to the IT workers, while the remaining 20% is given to the facilitator. This setup is particularly attractive to the targeted individuals, who often appear to be from low-income backgrounds. This financial incentive often leads them to recruit others into the activity.
In the vast majority of cases, payments are sent to cryptocurrency wallets. However, as shown in the following video, there are also examples of transactions conducted via PayPal. This particular video shows a "test" payment made to a PayPal account registered under a male name, further demonstrating the variety of payment channels used in the operation
https://go.screenpal.com/watch/cT6rXCnbpSy
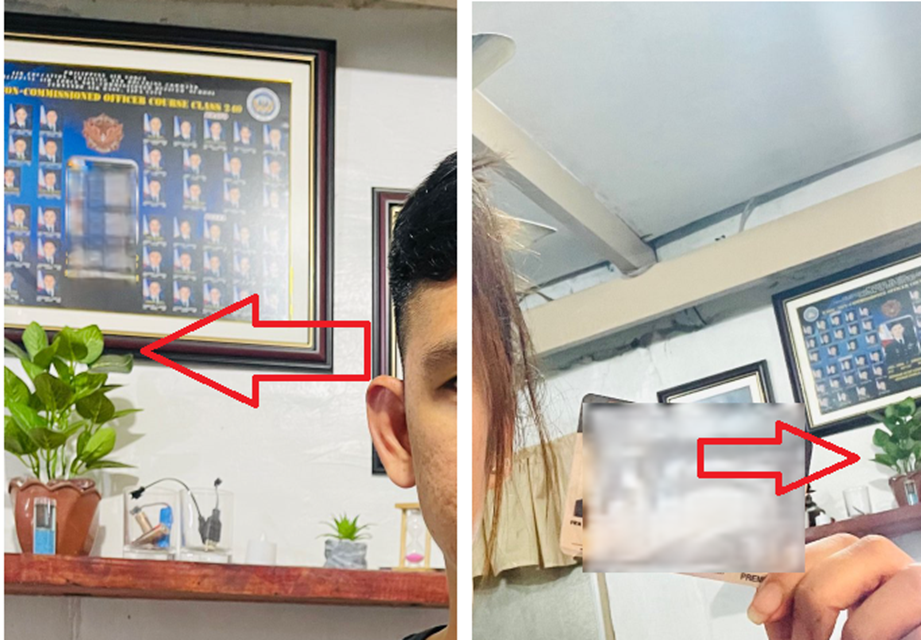
Additionally, the person featured in this video appears to have worked alongside their brother, lending both his own identity and that of his brother to enable work on Freelancer.com.
As evidenced in the following photo, both individuals took a picture holding their identification documents for the Freelancer.com platform. They appear to be in the same location, as both documents share the same last name, and visually, the background elements such as the plant on the shelf and the framed picture on the wall are consistent across both images.
However, not all payments are made via cryptocurrency or PayPal. In several instances, it has been observed that IT workers request payments to be redirected to traditional bank accounts.
In many cases, these individuals successfully persuade the counterpart to cooperate. One such case is shown below, where the IT worker appears to have contributed to architecture and construction projects, delivering completed work to a construction company. As the next image illustrates, the IT worker is requesting that the payment be sent to a Citibank account under the name “Yurii.”
This particular IT worker was using a fraudulent Upwork account based on someone else’s identity, posing as an architect from Illinois. Part of their project proposal is visible, along with the client’s response regarding the completion of architectural plans using CAD software. In the message exchange, the IT worker also claims to follow Illinois residential building standards:
The variety of payment methods observed demonstrates that these actors have the capability to receive funds through multiple channels. It also indicates the presence of collaborators operating within this “supply chain.” Additionally, they leverage a range of identity-related strategies, including the use of legitimate individuals who willingly lend their names, unauthorized use of stolen identities, and even the artificial creation of entirely fake personas.
These distinct approaches must be addressed with tailored countermeasures. A standardized KYC process may confirm who someone claims to be, but it does not necessarily detect whether that person is impersonating someone else.
The Issue and Pivoting Tactics
Evidence shows that for over a year, some IT workers have been actively using freelance job platforms such as Freelancer and Upwork to recruit individuals willing to “work” with them. The recruitment process typically begins with initial contact through these platforms, after which the conversation is moved to other communication channels, usually Discord or Telegram.
Once contact is established, the IT workers propose a cooperation scheme: the recruited individual allows them to use their verified identity on Upwork to apply for and carry out freelance projects. In return, the collaborator receives 20% of the earnings, while the remaining 80% is sent back to the IT worker.
What makes this tactic particularly notable is how these freelance platforms are being exploited not only to find work, but to recruit unwitting accomplices who serve as identity proxies. While these platforms do implement security measures, the success of these operations highlights how easily such protections can be bypassed through social engineering.
In addition, the use of other individuals identities including the sharing of full ID documents and personal information has serious implications. It enables threat actors to pivot into other services, escalate their access, and advance toward more complex scenarios.
With this data, they can evolve their tactics and even leverage AI to enhance and adapt their tradecraft. This was the case with one IT recruiter who, according to the evidence, appears to have been using a fake identity that allows him to receive an invitation from Apple to participate as a developer in one of their programs using the identity of Bryan:
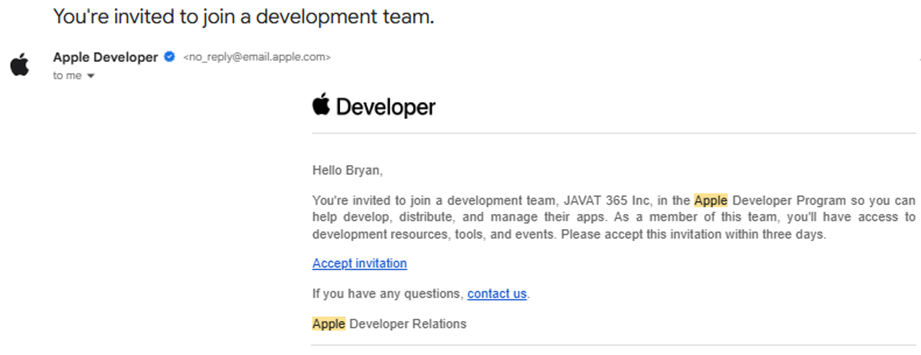
The documents uncovered, which include presentations, guides, emails, and chat instructions, strongly suggest that this is a well-established and widely adopted method. The consistent formatting and repeated content across these materials point to the existence of a structured playbook.
This framework allows IT workers to transition into recruiter roles and scale their operations by onboarding new collaborators, gaining access to freelance platforms, and using multiple identities to pivot into more favorable scenarios or regions where they can continue operating without detection.
Operational Breakdown – North Korean “IT Recruiter” Playbook
The previously documented evidence including chat logs, recruitment scripts, altered identities, and payment coordination illustrates a consistent methodology employed across multiple cases. These findings support the existence of a structured, repeatable workflow.
What follows is a breakdown of this eight-step operational model, detailing how North Korean IT workers transition from initial contact to full exploitation of freelance platforms through identity proxies. The following graphic captures and summarizes the behavior patterns demonstrated throughout the investigation:

The campaign begins with the creation of fraudulent identities across freelance and professional networking platforms such as Upwork, Freelancer, and LinkedIn. These profiles mimic legitimate IT professionals or recruiters, often complete with portfolio items, certifications, and prior reviews to enhance credibility. In parallel, threat actors also create fake accounts on social networks and online community websites including language exchange platforms or forums for vulnerable populations which they likely view as fertile ground for recruitment. The objective is to monitor job activity, identify targets, and strategically position themselves for engagement across multiple ecosystem.
Once embedded in the ecosystem, the threat actor initiates contact under the guise of collaboration or recruitment. This typically occurs via platforms like GitHub, Freelancer, or Upwork, where they may message potential victims with an offer to "work together" or "refer" them to opportunities. The tone is usually professional and subtle to avoid suspicion.
After establishing initial trust, the threat actor urges the victim to shift
communication to encrypted or less-moderated messaging apps like Telegram or Discord. This move is critical — it removes the interaction from the visibility of platform administrators and enables the threat actor to share content that would otherwise trigger moderation or automated detection.
Now positioned as a trusted collaborator, the actor shares a pre-written operational script. This document includes instructions on how the partnership will work:
• Who handles what tasks
• Payment handling agreements
• Security hygiene (e.g., keeping accounts "clean" or instructions on avoiding detection)
These scripts are templated, operationalized, and fine-tuned to maintain efficiency and scalability across multiple victims.
Once the victim agrees to participate, they either:
1. Create new freelance accounts following specific instructions, or
2. Hand over access to their existing accounts (via credentials or tokens).
This gives the threat actor direct access to an account with a trusted reputation, which is difficult for them to build from scratch due to sanctions or IP bans.
With access secured, the actor connects to the victim’s environment via remote access tools like AnyDesk or Chrome Remote Desktop. From this point on, all freelance work — including code delivery, communications with clients, and task submissions — is performed under the victim’s IP address and identity, making attribution nearly impossible.
After job completion, the client pays the victim, assuming the work was done legitimately. Per the agreement, the victim keeps 20% of the payment and transfers the remaining 80% to the threat actor. In many cases, this transfer is done via cryptocurrency or untraceable digital payment methods, insulating the actor from direct financial exposure.
If a victim’s account becomes flagged, banned, or under review, the actor is quick to adapt. They often suggest that the victim enlist a family member or trusted associate to create a new account, effectively laundering operational access through fresh identities. This resilience ensures continuity of operations even under scrutiny.
Highlight activity of It worker:
During the investigation, multiple websites, platforms, and services were identified as being leveraged by the actors to support their operations—both in their roles as IT Workers and as IT Recruiters. Notably, the following resources were observed::
Websites and Platforms Identified:
Job Portals & Freelance Platforms
• https://www.freelancer.com
• https://www.golance.com
• https://latium.org/groups
• https://www.freelancermap.com
• https://www.randstadusa.com
• https://hiringneartalent.com
• https://us.bold.pro
• http://monster.com
• https://kadrof.ru
Proxy Services Used
• https://proxy6.net
• https://iproyal.com
• https://spaceproxy.net
Geolocation / Mapping Services
• https://www.openstreetmap.org
Learning Platforms
• https://mobirise.com
• https://codedthemes.com
• https://themewagon.com
• https://www.creative-tim.com
• https://dashboardpack.com
• https://www.devwares.com
• https://designrevision.com
• https://vuemastery.com
• https://www.kaggle.com
• https://www.postman.com
• https://www.codingame.com
• https://www.codecademy.com
• https://www.hinative.com
VPN Services
• https://cloudzy.com
• https://vps2day.com
• https://usavps.com
Phone/SMS Services
• https://smspva.com
• https://sms.usmobilenumbers.com
• https://smsbower.com
• https://rizzlysms.com
• https://temp-number.org
Communication Platforms
• https://discord.com
• https://slack.com
• https://mastodon.social
Community & Social Platforms
• https://www.bestbuddies.org
• https://ablehere.com
• https://interpals.net
• https://polyglotclub.fr
• https://www.hellotalk.com
Cloud/File Sharing Services
• https://www.myprepaidcenter.com
• https://www.sendgb.com
• https://pdfguru.com
Development Tools
• https://www.openai.com
• https://www.axcrypt.net
• https://www.wappalyzer.com
• https://jasonsavard.com
• https://xdevs.ltd
AI / Chatbot Platforms
• https://poe.com
Crypto / Finance Tools
• https://cwallet.com
• https://coinsbee.com
Email Tracking Tools
• https://mailtrack.io
News / Content Aggregation
• https://follow.it
Blockchain / GameFi Platforms
• https://www.skymavis.com
Stock Media / Images
• https://www.dreamstime.com
• https://www.pixtastock.com
Stock Media / Creative Assets
• https://envato.com
News / Analytics
• https://www.informer.com
Crypto / Online Gaming
• https://nanogames.io
Illicit fake-ID / KYC-bypass marketplace
• Verif.tools
Conclusion:
The observed shift in DPRK-linked IT worker behavior — from individually securing fraudulent employment to actively recruiting and managing collaborators — marks a critical evolution in their operational strategy. This recruiter-first model demonstrates a higher degree of coordination, scalability, and tactical sophistication than previously documented. The recurring use of scripted workflows, credential hijacking, and remote-access tools across multiple platforms indicates not opportunistic abuse, but a deliberate and institutionalized campaign designed to expand access and obfuscate attribution.
As these actors increasingly blur the lines between worker and recruiter roles, they not only increase the volume of compromised accounts but also create a multilayered threat architecture that complicates detection and response. This emerging model allows DPRK operators to amplify their reach, evade platform-level controls, and insulate themselves from direct exposure — all while sustaining a revenue-generating pipeline aligned with broader regime objectives.
This evolution underscores the urgency for both private sector platforms and national security entities to enhance their detection capabilities through behavioral-based approaches. A stronger focus on Indicators of Attack (IOAs) — such as suspicious account handovers, repeated use of remote-access tooling, and scripted onboarding workflows — can help expose malicious intent earlier in the intrusion lifecycle. Without coordinated countermeasures and an emphasis on intent-driven detection, this recruiter-facilitated infiltration model is poised to become a durable and expanding pillar of DPRK’s cyber-enabled financial operations.
Recommendations:
For Users and Freelancers (Avoidance)
• Never Share or Delegate Verified Accounts: Under no circumstances should you create a new account for a collaborator, register on someone’s behalf, or “temporarily” hand over control of your verified job platform accounts (Upwork, Freelancer, GitHub, Fiverr). The actor’s single most critical objective is to work under your identity.
• No Remote Access for Onboarding: Decline any request to install or use remote access tools (such as AnyDesk, Chrome Remote Desktop, or TeamViewer) or browser extensions simply to “bid,” “verify identity,” or “onboard.” Legitimate clients do not need full control of your machine for these purposes.
• Keep Communication On-Platform: Refuse to move conversations to unmonitored messaging apps (like Telegram, Discord, or WhatsApp) for “faster” coordination, especially before a contract is finalized and established on the platform. Be highly suspicious if a recruiter immediately tries to shift comms off-site.
• Verify Payment Structure: Immediately report any job offer that requires you to receive a payment and then manually send a large percentage (e.g., 80%) to a third party or “teammate.” This is a classic revenue laundering scheme.
Trust and Identity Verification
• Scrutinize Recruiter Profiles: Examine the recruiter’s history, language, and posting style. Look for discrepancies, generic/repetitive pitch language, and a lack of specific, verifiable company details.
• Verify Company Existence Independently: If the recruiter claims to work for a company, independently verify the company’s website, LinkedIn presence, and its job postings on its own official careers page (not just relying on the freelance platform listing).
• Guard PII and KYC Documents: Never send scans of sensitive Personally Identifiable Information (PII) like passports or driver’s licenses outside of official, verified platform Know Your Customer (KYC) flows.
Operational Hygiene
• Secure Payments: Only agree to work under the platform’s official escrow service with a clear Statement of Work (SOW), defined milestones, and deliverables. Avoid any offers to “pay off-platform.”
• Report and Disengage: If someone requests account control, identity reuse, or an unusual payment split, immediately stop all contact and report the interaction via the platform’s abuse channel.
Recommendations for HR and Recruiting Teams
HR and recruiting teams on job platforms must establish stricter vetting procedures to detect the fake “recruiter” profiles and prevent account abuse.
• Mandate Platform Use: Implement a strict policy that all candidate communication and work instructions must remain on the official job platform until a contract is fully signed and verified. Any request to shift immediately to unmonitored apps (Discord, Telegram) should be a red flag.
• Require Video Verification: Require a live, interactive video interview as part of the screening process, ensuring the candidate’s appearance matches the profile photo and submitted documents (which are often stolen or generated by AI).
• Standardize Onboarding: Any recruiter sending a generic, pre-written “script” or operational playbook (Step 4) rather than a customized scope of work should raise suspicion. Ensure your internal recruiters are trained to use approved, non-scripted communication methods.
• Ban proxy hiring in writing: Contract clauses: no “representatives,” no shared accounts, no third-party KYC, no off-platform comms pre-offer termination if violated.
• Script detection training: Teach recruiters to spot copy-paste “collaborator” scripts and pressure tactics; require use of approved templates with ticket IDs.
Detection Team Recommendations
• Block Unapproved RMM Tools: Implement Application Control to block the execution of unauthorized Remote Monitoring and Management (RMM) tools like AnyDesk, Chrome Remote Desktop, and TeamViewer on contractor endpoints.
• Monitor RMM/VPN for New Users: Create high-priority alerts in the SIEM/EDR for any traffic or execution of approved or unapproved RMM/VPN tools associated with newly onboarded contractors.
• Flag Impossible Travel: Utilize UEBA to flag sessions showing “impossible travel” — sequential logins from geographically disparate IPs or unexpected time zones — on contractor accounts.
• Audit for Credential Tampering: Immediately alert on attempts to change sensitive account features on new contractor profiles, especially MFA methods, payout bank details, or tax information. These actions signal account hijacking.
Recommendations for KYC/Identity Verification Companies
• Anti-AI document capture: Require photos of IDs on flat, matte surfaces and instruct users to hold documents in specific orientations/angles. Use randomized pose prompts (e.g., “tilt 20°, cover a corner, rotate once”) to make AI-generated spoofs and high-end deepfake tools far harder to replicate at scale.
• Active liveness, not just selfies: Add real-time challenge–response (blink, head-turn, read a short phrase, mirror a gesture) with motion parallax checks and micro-texture analysis to detect screen replays and synthetic faces.
• Behavioral signals: Flag sequences like new device/IP → immediate KYC pass → payout change; multiple KYC attempts from the same ASN/device; scripted onboarding patterns in chat that ask users to share credentials or install remote-access tools.
• During the sensitive KYC/verification flow, implement client-side checks to detect if common Remote Monitoring and Management (RMM) software (AnyDesk, CRD, TeamViewer) is actively running on the user’s machine. If these tools are detected, pause the verification process and display a high-risk warning
Enhanced User Awareness Programs:
• Since legitimate users are the main point of failure, deploy specific, platform-level educational warnings at the exact moment a user is about to submit a sensitive document or grant remote access.
• The warning should explicitly state the risk: “Do NOT submit this document if you were instructed to do so by a ‘recruiter’ on Telegram or if you intend to share access to this account.”