This series aims to provide a recurring in-depth analysis from the frontlines of the ongoing fight against the highly adaptable and continuously vigilant operators of "crypto drainers". We will regularly publish detailed reports on drainers targeting cryptocurrency users, accompanied by a comprehensive list of indicators of compromise and an examination of evolving tactics, techniques, and procedures.
Today’s discussion will encompass novel phishing kits, 'cloaking' methodologies, strategies employed for concealing C2 panels, and various user 'luring' techniques observed in the wild, particularly within the Inferno, Rublevka, Eleven, and Vanilla Drainer families. Our objective is to delineate a broad landscape of the perpetually evolving threat campaigns for the benefit of both general users and security professionals responsible for the blocking and remediation of such operations.
Should you encounter a malicious page conforming to any of the descriptions provided below, please report it via the SEAL Phishing Bot. For any other information, please contact the SEAL Tips Bot. We only accept verified leads with actionable IOCs and TTPs, validate your claims to the best of your ability before contacting us.
Intro to Crypto Drainers
For those unfamiliar with the term crypto drainer (‘drainer’ for short), a drainer is a piece of malicious JavaScript which is loaded into a phishing site. The purpose of a drainer is to trick users into giving up control of their crypto assets, either by signing a transaction which causes all of their funds to be sent to the hacker under the guise of something innocuous such as claiming an airdrop, or by giving up their seed phrase entirely. Drainers are typically developed through a SaaS model, wherein the operators are responsible for the development and maintenance of the drainer software and backend infrastructure, while the affiliates are responsible for the deployment and targeting of potential victims. Profits are split between operators and affiliates at an average of 20/80, with operators taking more or less commission depending on the overall profitability of the affiliate.
Drainer Updates
Inferno
Recently, Inferno Drainer has been the most active among all drainer families we’ve observed. It supports EVM, Solana, and Tron wallets, and modern variants can be identified by an initial request sent to /secureproxy or /secureproxy.php. This file exists as a result of SEAL Intel’s efforts over the past year to collaborate with Web2 and Web3 partners to neutralize centralized Inferno Drainer infrastructure where possible. Today, this file loads a C2 domain from a smart contract and proxies requests to that domain through the landing page host. This allows Inferno to circumvent subresource-based blocking. The latest C2 domain being used is jdfkgkgkfkjjkfkffdkfdkdfkdkdk.com, which was configured in the following transaction.
Certain deployments of Inferno Drainer have also begun renaming the secureproxy file, likely in an attempt to defeat fingerprint-based analysis. This indicates that the drainer operators and affiliates are continuously refining their techniques to evade automation, and that further investigation is required.
Rublevka
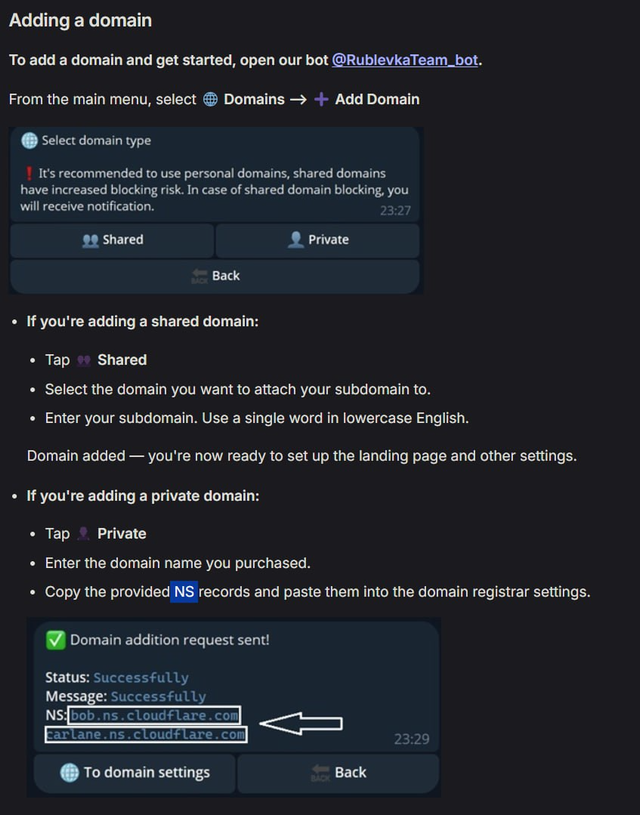
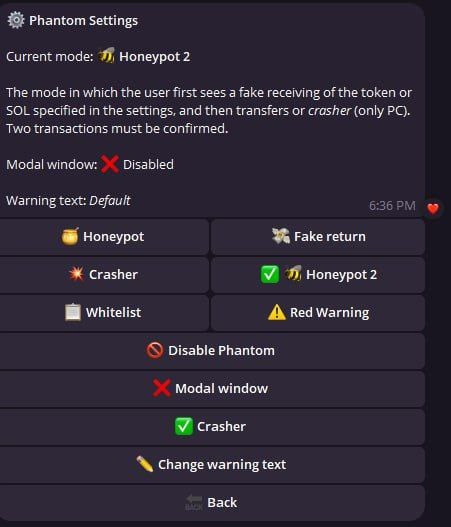
Rublevka Team offers a Solana focused drainer which is unusually well documented. SEAL Intel conducted an operation to block hundreds of Rublevka-controlled C2 domains. All domains were registered with NameCheap and proxied via Cloudflare. Due to the large volume of domains, we won’t be enumerating all IoCs here. However, we provide archives of their documentation and other useful information in case they are deleted.
Home Page (Archive)
Solana Drainer (Archive)
Settings (Archive)
Additional Resources (Archive)
Changelogs (Archive)
Administrators:
- @sinactive (1636170234)
- @nft4x (7696738707)
- @BalaclavaRTD (7479395455)
- @r_boost (7854699763)
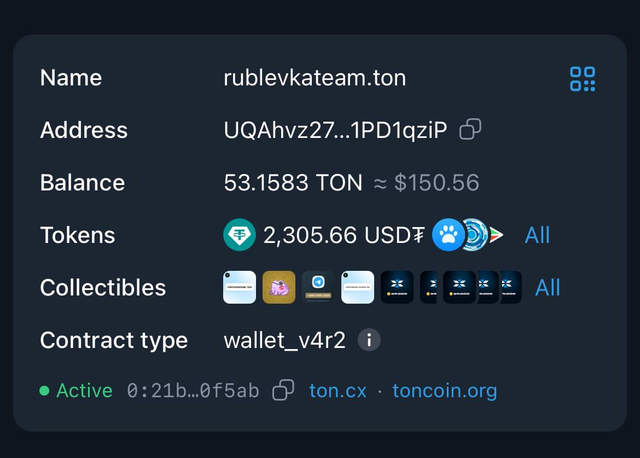
Additionally, a TON address (UQAhvz27eT_nglB2kf8_oGuedYmXVtLSj6pBh3Z91PD1qziP) seems to be associated with this team.
Eleven Drainer
SEAL Intel was informed of a new drainer known as Eleven Drainer. Similar to Rublevka, this particular team publicly details its operations, even offering a BMW M4 giveaway for their top affiliate, which includes a professional interview.
> Customer ID presented with the gifted car in the background
> Are you "shocked"? The affiliate answers: “Fully”
> You weren't scared to come here? Why did you agree? The affiliate answers: Initially, I was scared. However, upon reflection, I realized I had not violated any laws of the Russian Federation nor acted against Russia.
The contest winner frequently uses expletives during the interview. The interview addresses various aspects of his activity (his first profit was only $200), history (he began scamming people around 2018), and team building (he works with a few 'buddies'). He also praises the Eleven Drainer team. Furthermore, the interview serves as an advertisement for newly launched functionalities.
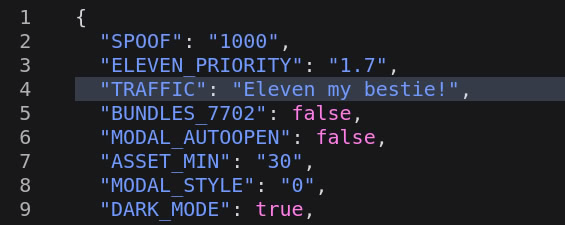
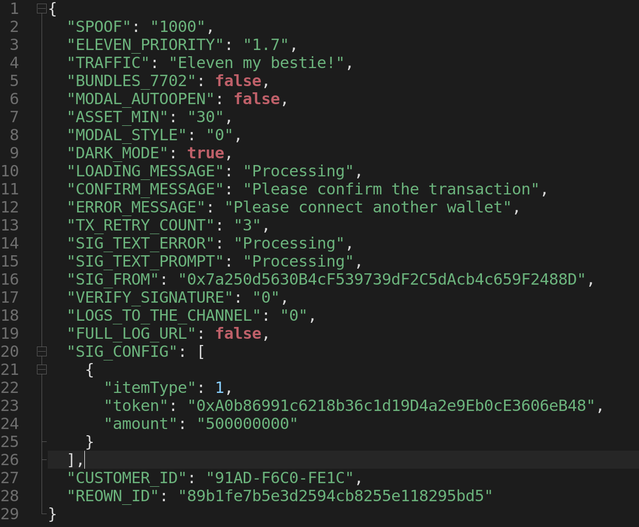
Eleven Drainer loads its payload from the eleven.js script and its configuration data from settings.json. The actual C2 domain is only revealed after a successful wallet connection. Additionally, C2 panels are actively rotated, which complicates blocking efforts.
Campaigns
Google Ads
In January 2025, Malwarebytes reported massive compromises of various advertisement network accounts. Instead of setting up their own Google Ads accounts, enduring the complexities of verification, and risking a rapid account ban, attackers chose to gain access to legitimate businesses running ad campaigns for legitimate brands and deploy malvertising directly from these compromised accounts. An interesting caveat is the utilization of advanced browser fingerprinting and built-in Google Ads geolocation for precise target selection. Attackers can limit the display of advertisements to intended targets from a particular region or even a specific city, and they can freely choose demographics and language preferences. Furthermore, phishing kits allow for filtering 'unwanted' traffic - such as security researchers, sandboxes, or crawlers - by displaying legitimate content for clicks not originating from desired sources and redirecting the most promising victims to the actual phishing website.
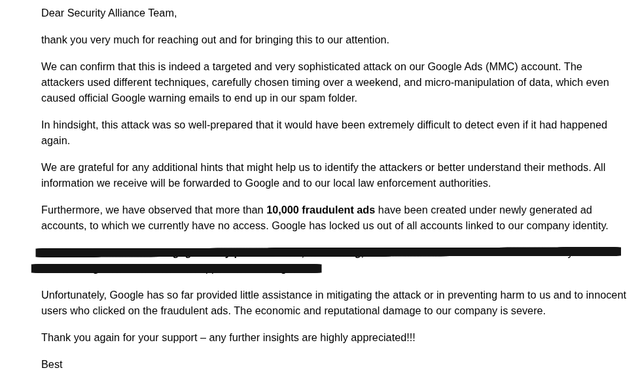
We contacted one of the affected legitimate advertisers from Europe and received the following information. As you can see, the issue of account takeover is well-known among big advertising networks.
For an exact understanding of the scale of Google Ads abuse, we recommend reading "Keyword Research" by Phish Destroy, a comprehensive document that outlines how many crypto-specific keywords are actively targeted by malicious actors.
Through our own pivots, we have discovered numerous pages utilizing URLs such as https://sites.google.com/view/[randomid]/[randomid] and driving traffic from Google Ads toward phishing kits of one of the drainer families. We also observed visible 'brand tags' allowing us to track the keywords used to direct traffic to these websites. The following results cover the last 30 days and are not exhaustive, as attackers tend to have their URLs quickly blacklisted for specific keywords.
1. phantom wallet (91 Hits)
2. coinbase (26 hits)
3. trezor (20 hits)
4. metamask (19 hits)
5. uniswap (13 hits)
6. phantom (5 hits)
7. blockchain usb miner (2 hits)
8. ledger (2 hits)
9. opensea (2 hits)
10. paraswap (2 hits)
11. debridge (1 hit)
12. coinomi (1 ht)
13. axiom (1 hit)
Google Sites and Other Trusted Hosts
Drainer affiliates are compelled to be creative, not only in acquiring traffic to their websites but also in obfuscating the maliciousness of the code they employ for exploiting user wallets. If drainer code were to be combined with the website's code and both loaded from the same host, a block and takedown would be nearly instantaneous. Consequently, we have observed attackers adopting several new strategies and engaging in near real-time experimentations to avoid being added to SEAL's blocklists.
- Hosting a clean landing page (without any malicious code) on a high-reputation domain like sites.google.com/view/[site_id]/[page_id].
- Re-registering previously whitelisted domains (often of defunct legitimate cryptocurrency protocols) for malicious purposes.
- Deploying fingerprinting on the landing page, which blocks malicious displays from sandboxes and researchers. In such cases, a fake CAPTCHA loading screen is displayed or a redirect to the legitimate website is applied without loading the malicious iframe.
- Hosting malicious code on yet another high-reputation website. We discovered the following hosts used for such purposes: cdpn.io / sites.google.com / storage.googleapis.com / view.pagesection.com / fiddle.jshell.net / cdn.jsdelivr.net / reown.com (This list is not exhaustive, and any such provider is at risk).
- If necessary, the chain of fetches can be extended to yet another high-reputation host, including fetching directly from GitHub repositories of throwaway accounts created solely for this reason.
It’s worth noting that evasion strategies differ among affiliates of a given drainer family and are not necessarily enforced at the drainer service level. We still observe less experienced operators attempting to brute force their way in with quick deployments of less sophisticated stacks, prioritizing quantity (a high number of registered domains) over quality (deploying sophisticated cloaking).
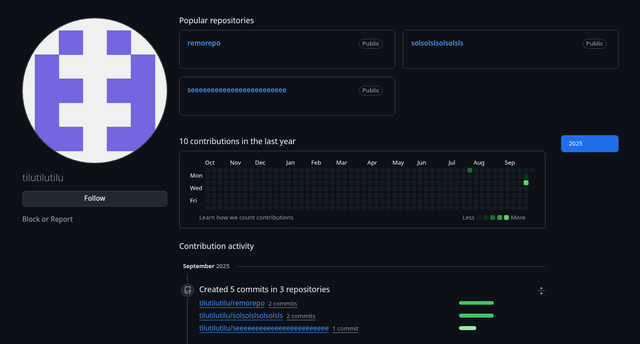
In one example, we observed an affiliate operating several Hyperliquid phishing sites that employed cdn.jsdelivr.net to directly fetch malicious payloads from their GitHub account from the following URL:
https://cdn.jsdelivr.net/gh/tilutilutilu/seeeeeeeeeeeeeeeeeeeeeeee@main/material-card-3.3.8.min.js
The associated GitHub account is linked to [email protected]. Interestingly, this attacker also opened a ticket on the MetaMask/eth-phishing-detect repository.
The presence of multiple malicious payloads on this account suggests that the attacker is likely managing numerous campaigns concurrently. Decoding JWT data from a script in the solsolslsolsolsls GitHub repository revealed Inferno-related customer data, including
customerId: vpZNKDfzL5group_id: 914iat: 1758650454
While the attacker has since changed their methodology and no longer loads payloads from jsdelivr, it is highly probable that this technique will be reused in the future.
GitHub Issues Spam
Between September 20th and 25th (when the last batch of spam issues was observed), the attacker created a total of 30,181 issues, utilizing 38 different GitHub accounts as well as various GitHub applications deployed specifically for this spam campaign. The GitHub security team reacted promptly, and after September 22nd, most of the new spam messages were deleted within minutes. In most cases, the attacker chose to impersonate the Gitcoin fundraising program, but they also experimented with posing as Ycombinator, Paradigm, or individual cryptocurrency protocols like Lido, Plasma, or Kamino. A full breakdown of activity, as well as a list of malicious domains, is presented in the table below.
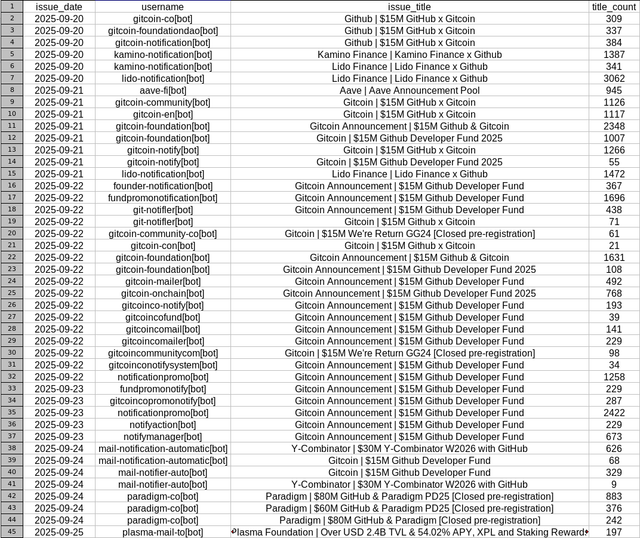
In total, the attacker deployed twenty different domains for hosting Inferno Drainer. Domains were often reused across different spam batches, regardless of previous removals from GitHub.
hxxps://github-application[.]com
hxxps://grants.paradlgm[.]com/
hxxps://y-comblnator[.]com/apply
hxxps://gitcoin-eligibility[.]com
hxxps://plazma[.]network
hxxps://app.aveeix[.]com/dashboard
hxxps://passport-gitcoin[.]com
hxxps://github-fundation[.]com/
hxxps://gitcoin-passport[.]com
hxxps://paradlgm[.]com/
hxxps://github-verification[.]com/
hxxps://github-apply[.]com/
hxxps://github.lido-pools[.]com/staking
hxxps://gitcoin-rewards[.]com/
hxxps://github-fund[.]com/
hxxps://foundation-github[.]com
hxxps://github-foundation[.]com
End
This inaugural report highlights the dynamic and persistent nature of cryptocurrency drainer operations. We've seen how operators of families like Inferno, Rublevka, Eleven, and Vanilla are constantly evolving their tactics, techniques, and procedures to lure users and evade detection. From sophisticated cloaking methodologies and C2 panel concealment to diverse user "luring" techniques across platforms like X (Twitter), Google Ads, and GitHub, the threat landscape remains complex and challenging.
A key takeaway is the drainers' continuous experimentation, even by individual affiliates, with new ways to hide malicious code and exploit user wallets. This includes leveraging high-reputation domains for landing pages and payload hosting, re-registering previously legitimate domains, and deploying advanced fingerprinting to thwart security researchers.
If you encounter a phishing site, please report it via the SEAL Phishing Bot. If you have any information regarding the operators of these drainers, or if you would like to join our effort to combat drainers, please contact the SEAL Tips Bot.

